Over the years, I have tracked a number of Anonymous operations. I like to consider myself a historian of sorts, but recently it seems that everyone is intentionally forgetting the past so they can reshape the future to fit their agenda. To add to the confusion there are a number of outlets who are unable to verify threat actors and their activity from just a few years ago. Let’s clear up a few things about OpIcarus.
Recently, Rogue Security Lab wrote a blog stating that Anonymous hackers were preparing to relaunch OpIcarus 2.0. The author goes on to write, “#OpIcarus was largely considered one of the most successful hacking operations of the last decade.” Let’s pause and recap.

Figure 1: Rogue Security Labs
Firstly, OpIcarus was originally promoted by Harvey Harris three years ago and began on February 8, 2016, less than a decade ago. The operation was originally billed as a physical protest of the Bank of England and the New York Stock Exchange, but grew during the build up to include members of the Bank for International Settlements (BIS) as digital targets. The second issue is related to the title “Anonymous Launches #OpIcarus 2.0.” OpIcarus 2.0 (aka Re-Engage) was launched almost three years ago on May 6, 2016. The 5th phase of OpIcarus was issued on June 11, 2017.
Figure 2: JTSEC3313
To add to the confusion, there are Anon spam accounts like JTSEC3313 who are continuously distributing posts containing target information in hopes it catches someone’s attention but doesn’t mean someone is actual going to attack. This is either because JTSEC (aka Jonathan Tremblay) is unable to actually hack these targets, or he is hoping someone else will carry out the attacks for him.
In the tweet above he is also seen hash tagging several operations such as #OpIcarus, an operation against international banks, #StopActa2, an operation against the Anti-Counterfeiting Trade Agreement, and #YellowVest, an operation in support of the political YellowVest movement against rising fuel prices and the cost of living in France. Clearly this actor is throwing what every he can against the wall to see what will stick and who will follow.
This is a change from the prior operators of OpIcarus. The new operators do not understand the content of the operation or the players that came before them; the result is a lot of repetitive information being posted. In the past, competent operators published target lists and their tools for the operation for those that chose to participate. Typically, these posts were followed by news of an outage, but this hasn’t been the case recently. At one time, OpIcarus even had a GitHub page full of tools that could be used against their list of targets.
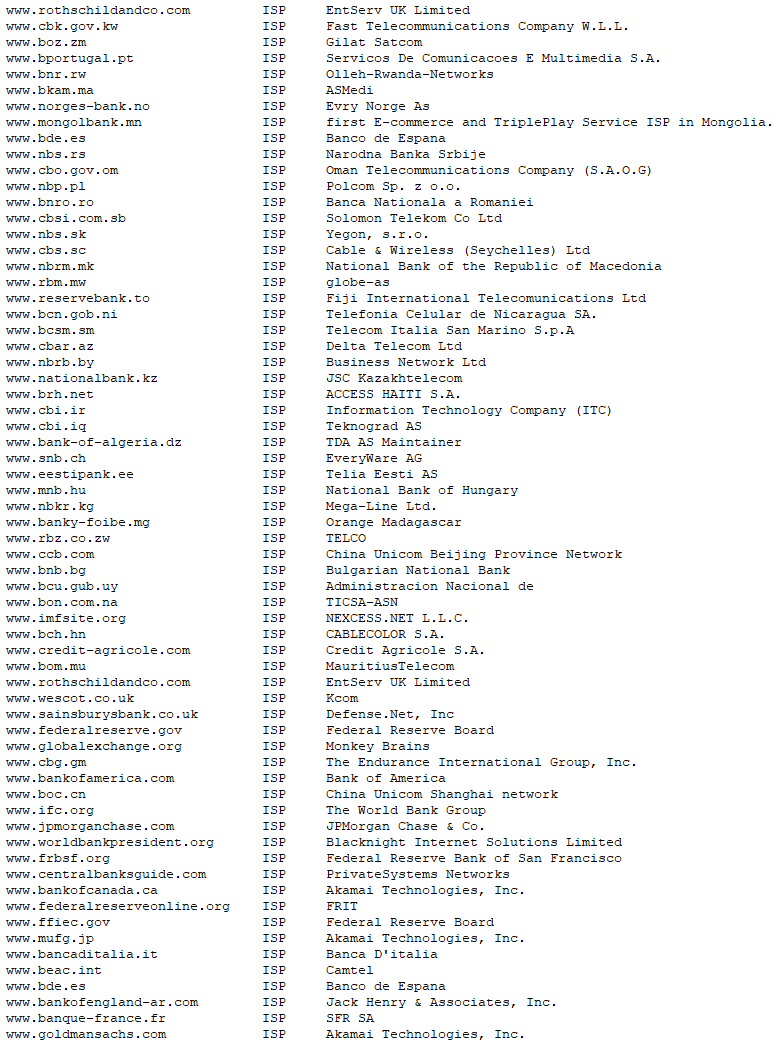
Figure 3: JTSEC OpIcarus Recon Targets (Current)
Today, JTSEC and other Anon’s associated with OpIcarus appear incapable of launching an attack. Instead they have chosen to recycle old target lists with little effect. I think it’s fair to say that the operation is still ongoing, but with limited resources compared to prior phases. At the moment, the actors only seem engaged in information-gathering operations, leveraging web application reconnaissance tools such as WAFW00F, The Harvester, Metasploit, XSStracer, WPScan, and TestSSL, as well as other tools used by criminals to map networks and look for vulnerabilities.
The Changing Face of Hacking
It is also important to note that the financial industry has been under attack for some time as OpIcarus enters its fourth year of operation. Those that have been targeted have had plenty of time to prepare and mitigate the risk presented to them by hacktivist and their toolkits. If OpIcarus wants to succeed in the future, they will need to find small- to medium-sized banks not previously targeted. They will also need to find more participates who possess the skills required to take down larger networks and applications.
Here is additional analysis of previous OpIcarus operations.