Abstract
Hajime is a sophisticated, flexible and future-proof IoT botnet. It is capable of updating itself and provides the ability to extend its member bots with ‘richer’ functions, both efficiently and fast. The Hajime botnet was first reported
by Sam Edwards and Ioannis Profetis from Rapidity Networks, who discovered the first occurrence of Hajime back in October, 2016, including the
update blog by Ioannis (@psychotropos), and the more quantitative research by
Symantec, which assesses the size of the threat.
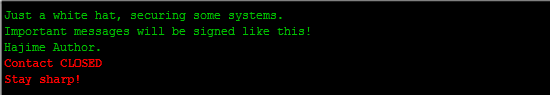
Figure 1: Message periodically displayed on the terminal by Hajime.
The distributed bot network used for command and control and updating is overlaid as a traceless torrent on top of the well-know public BitTorrent peer-to-peer network using dynamic info_hashes that change on a daily basis. All communications through BitTorrent are signed and encrypted using RC4 and private/public keys.
The current extension module provides scan and loader services to discover and infect new victims. The efficient SYN scanner implementation scans for open ports TCP/23 (telnet) and TCP/5358 (WSDAPI). Upon discovering open Telnet ports, the extension module tries to exploit the victim using brute force shell login much the same way Mirai did. For this purpose, Hajime botnet uses a list consisting of the 61 factory default passwords from Mirai and adds two new entries, ‘root/5up’ and ‘Admin/5up,’ which are factory defaults for Atheros wireless routers and access points. In addition, Hajime is capable of exploiting ARRIS modems using the password-of-the-day “backdoor” with the default seed as outlined
here.
Hajime does not rashly follow a fixed sequence of credentials, from Radware’s honeypot logs, we could conclude that the credentials used during an exploit change depending on the login banner of the victim. In doing so, Hajime increases its chances of successfully exploiting the device within a limited set of attempts and avoid the system account being locked or its IP being blacklisted for a set amount of time.