Putinstresser.eu is a recent DDoS-as-a-Service tool and is one of the newest additions to the growing array of low-priced services commonly known as ‘booter’ or ‘stresser’ services.
Download a Copy Now
Abstract
Putinstresser.eu is a recent DDoS-as-a-Service tool and is one of the newest additions to the growing array of low-priced services commonly known as ‘booter’ or ‘stresser’ services. The site illustrates the ease of access these services have reached. It provides different payment options, discovery tools, customer support and a variety of attack vectors for a wide range of customers. According to its FAQ, the booter performs up to 350Gbps per stress using DNS amplification attacks. TCP stress provides 600,000pps per stress.
Background
There are hundreds, maybe thousands, of DDoS-as-a-service tools such as Putinstresser.eu on the dark and clear nets to make money from customers looking to perform illegal DDoS attacks. Their target audience varies and includes hacktivists, ransom engineers and even businesses.
Attack Methods
The attack methods or vectors available to choose from include the ‘golden standards’ such as DNS, NTP, SNMP amplification attacks as well as the latest Memcached DDoS attack. It also includes traditional TCP XSYN, XACK and XMAS floods, GRE-based assaults, attacks dedicated to TeamSpeak servers using the TS3 protocol and attack vectors that target different multi-player gaming platforms such as Valve Source Engine (VSE), Minecraft, Counter Strike (GK_CS), Steam and San Andreas Multi-Player (GK_Samp). The owners of the site advertised their attack vectors on Pastebin with a short description and some help for unseasoned attackers.
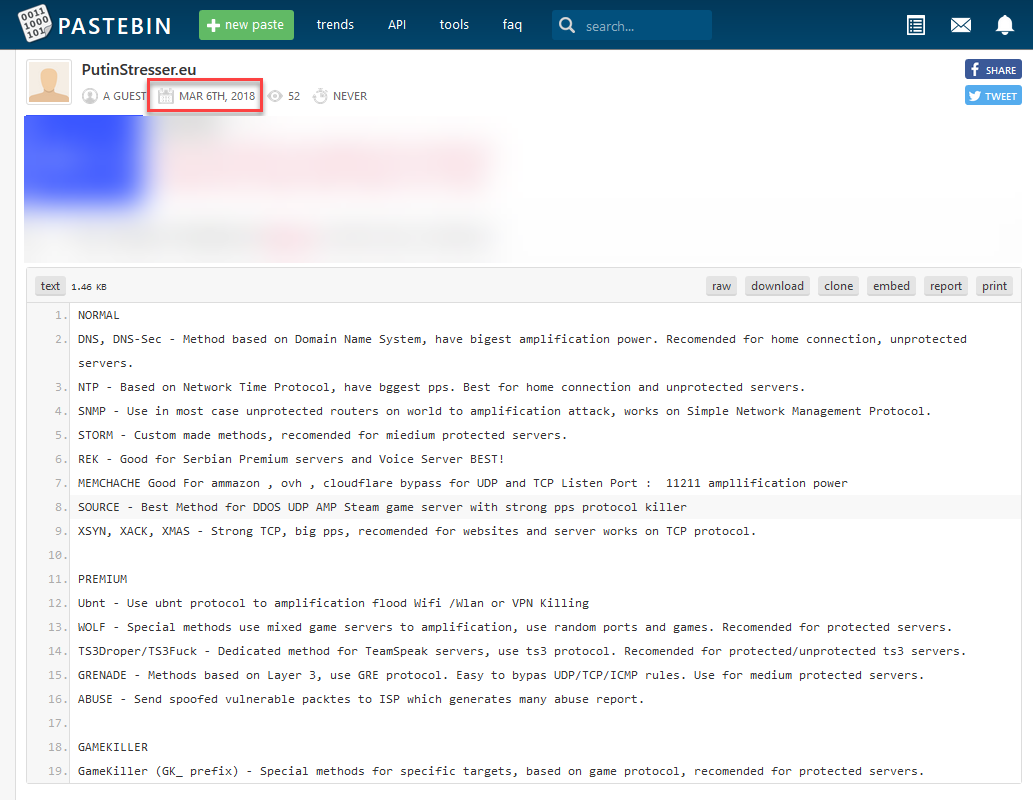
Figure 1: Attack vector library on Pastebin
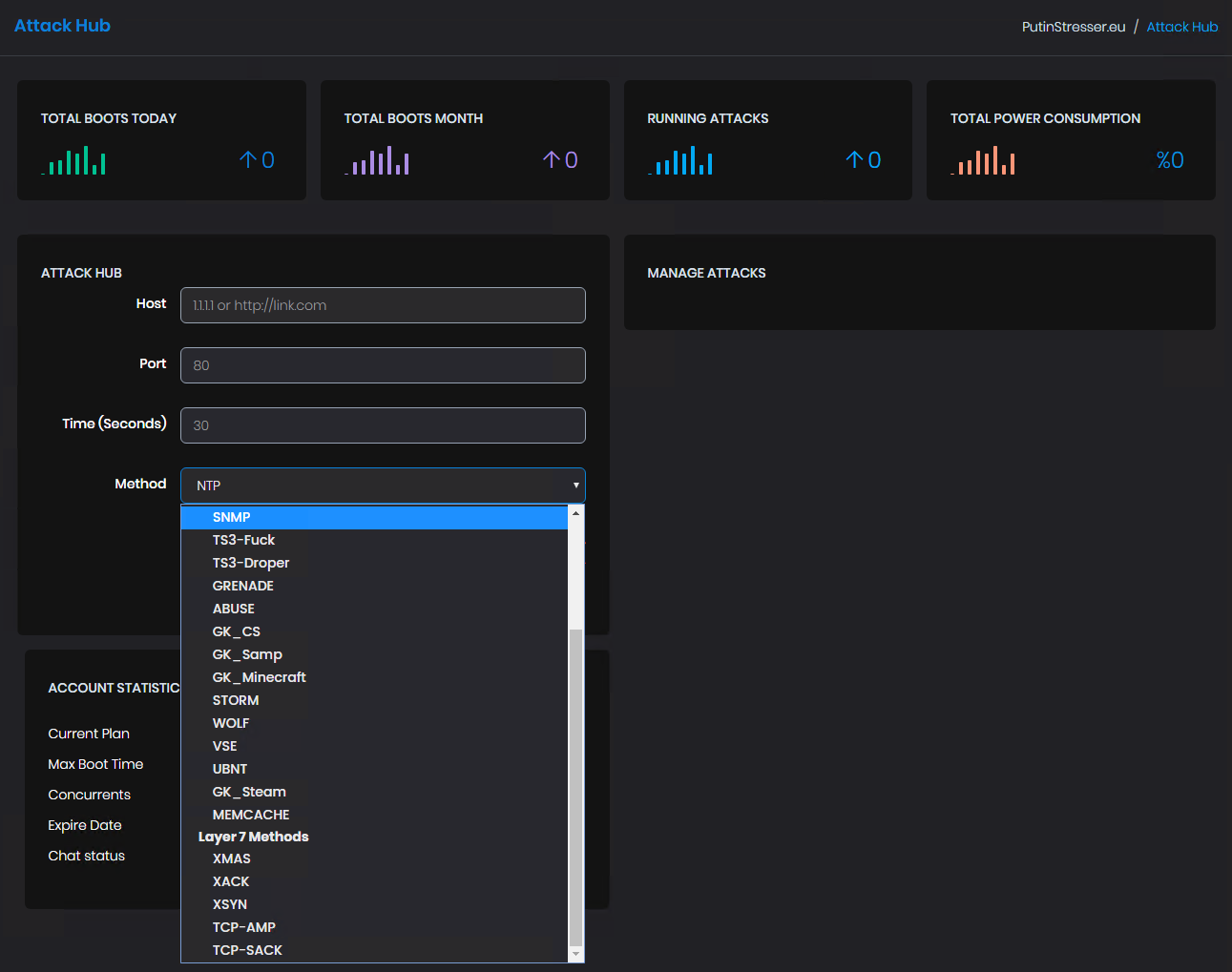
Figure 2: Attack vectors dropdown menu from the attack hub
Plans and Products
Putinstresser plans start with a trial plan at $5 for a 400-second attack time that remains valid for one week. The first full plan starts at $10 per month for a 600-second attack time with one concurrent attack. The highest plan provides nearly 3.5 hours of attack time for $400 and includes the ability to run six concurrent attacks.
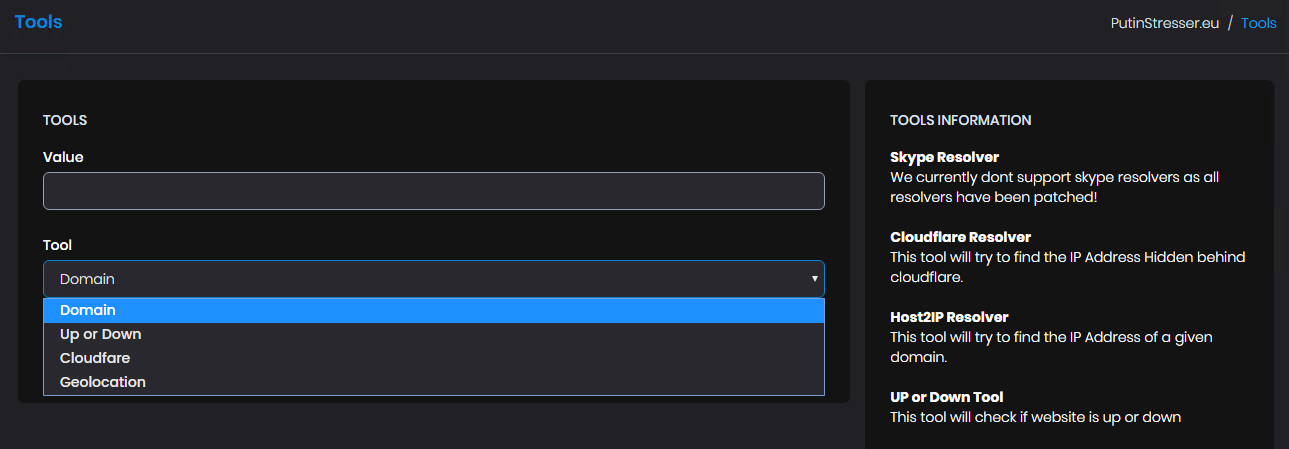
Figure 3: Subscription pricing
The Putinstesser site provides several payment options including PayPal, Bitcoin, paysafecard, Skrill and CSGO Skins (CSGO skins have turned into a currency between gamers and can be traded online via sites such as csgo-skins.com and skins.cash).
The Putinstesser DDoS-as-a-service operators offer live chat and support for users requiring assistance and features a support feature to submit and track support tickets as well as live chat options via
Discord.
The Putinstesser site features convenient tools for resolving IP addresses and checking if a targeted website is “up” or “down.” It also includes an option to find the IP address of services protected (hidden) behind Cloudflare.
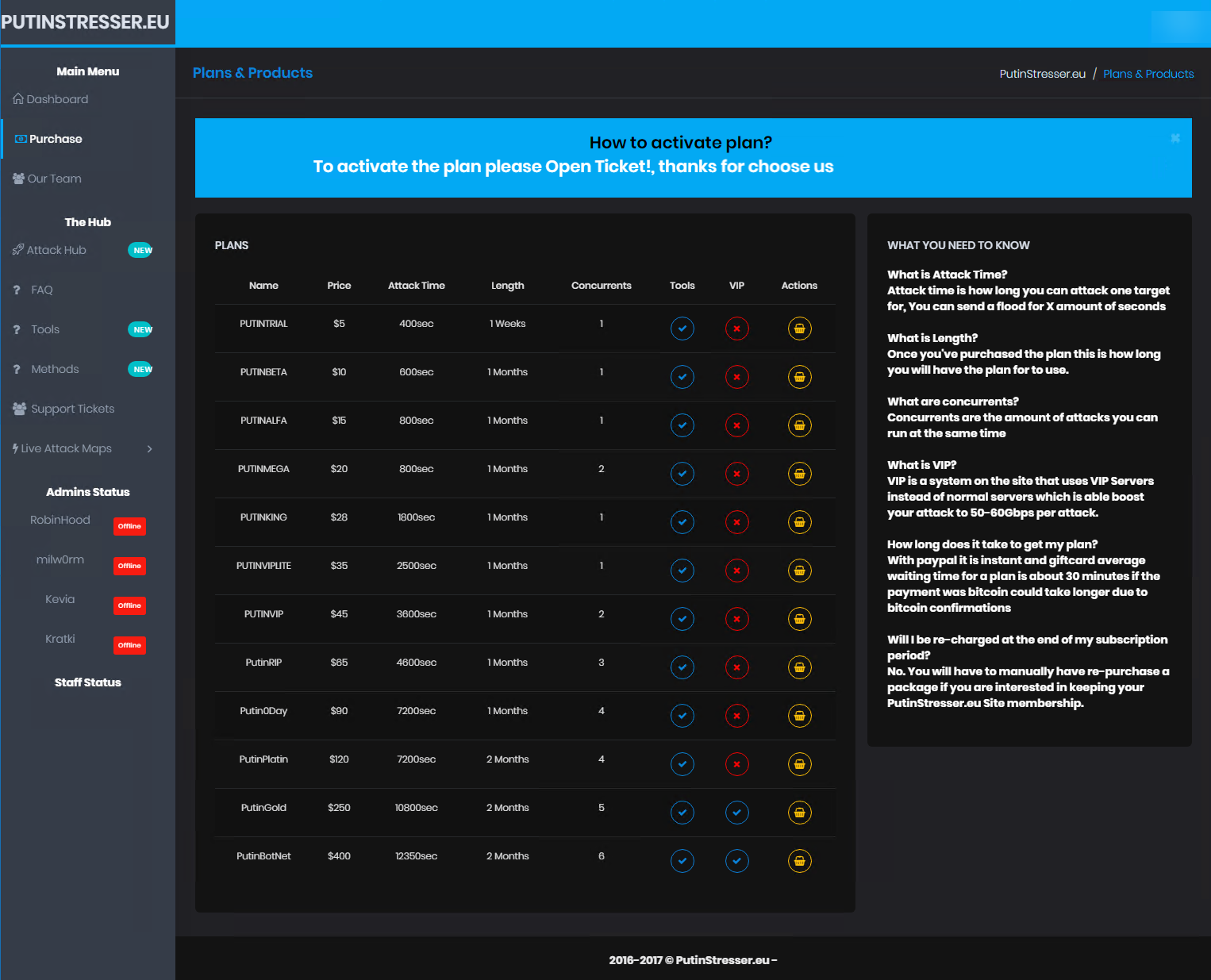
Figure 4: Monitoring tools
Effective DDoS Protection Essentials
- Hybrid DDoS Protection - On-premise and
cloud DDoS protection for real-time
DDoS attack prevention that also addresses high volume attacks and protects from pipe saturation
- Behavioral-Based Detection - Quickly and accurately identify and block anomalies while allowing legitimate traffic through
- Real-Time Signature Creation - Promptly protect from unknown threats and zero-day attacks
- A Cyber-Security Emergency Response Plan - A dedicated emergency team of experts who have experience with Internet of Things security and handling IoT outbreaks
- Intelligence on Active Threat Actors – high fidelity, correlated and analyzed date for preemptive protection against currently active known attackers
For further network and
application security and DDoS protection measures, Radware urges companies to inspect and patch their network in order to defend against risks and threats.
Under Attack and in Need of Expert Emergency Assistance? Radware Can Help
Radware offers a
DDoS protection service to help respond to security emergencies, neutralize the risk and better safeguard operations before irreparable damages occur. If you’re under DDoS attack or malware outbreak and in need of emergency assistance,
contact us with the code "Red Button."