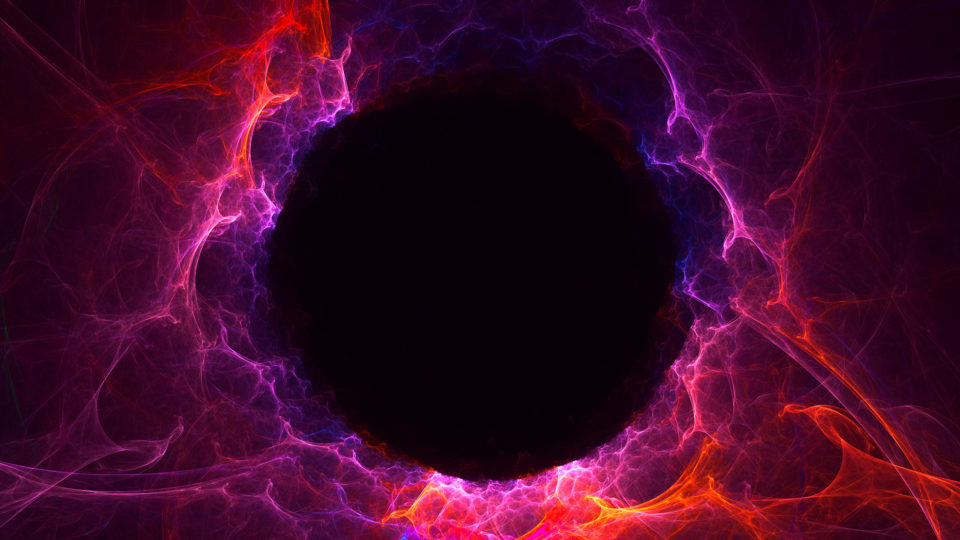
Your cloud provider may blackhole YOU when under attack.
Blackholing is a technique to mitigate DDoS attacks by discarding incoming or outgoing traffic silently (hence the name black hole). Service providers are using black holing to mitigate DDoS flood attacks by discarding excessive traffic destined for specific IP addresses under attack. The problem? It discards ALL traffic destined to a victim, making it invisible and unavailable.
Let me portray some mitigation strategies for DDoS attacks to understand when blackholing would act against you.
DDoS Mitigation Strategies in Public Clouds
CSOs and CIOs of organizations who run their applications in public clouds may deploy several strategies to mitigate a DDoS threat. They may opt for the provider’s DDoS mitigation service (such as AWS Shield, Azure DDoS Protection or Cloud Armor), or treat DDoS attacks as a networking issue by auto-scaling their application capacity.
When you opt for your provider’s DDoS mitigation service, you are protected against common L3-L4 DDoS attacks. More sophisticated attack vectors, or L7 attacks, will go undetected by the provider’s mitigation service.
[You may also like: What To Consider When Evaluating DDoS Mitigation Services]
Auto-scaling is also a valid strategy to deal with DDoS attacks; attackers increase the application traffic volume by generating traffic from fake users, aiming to consume your application resources and make them unavailable to legitimate users. Auto-scaling of your application resources converts DDoS attacks into a matter of cost.
The hidden assumption behind both strategies is that your cloud provider has unlimited networking and compute capacity to mitigate attacks or absorb them. This is true up to a certain level of attack. But in an era where attacks are becoming gigantic, providers fall short.
What Happens When Your Provider Falls Short?
When your provider’s capacity is exceeded, their main concern is that the attack that's targeting you will deny service from neighboring tenants. After all, it is a shared infrastructure. The provider will black hole all traffic destined to your IP address space – to save the rest of their customers.
A key consequence of using blackholing when good traffic is also affected is that the attacker has essentially accomplished their goal of disrupting traffic to the target network or service. And your provider is helping facilitate this.
[You may also like: DDoS Protection is Like Airbags in Your Car]
Effective DDoS mitigation strategy requires expertise, capacity and reputation. If your application is critical to your business, then availability is your main concern. Go for a world class DDoS mitigation provider that can guarantee full attack coverage and near unlimited capacity to offload any attack campaign that may target your business.

Read Radware's “2019-2020 Global Application & Network Security Report” to learn more.
Download Now