Radware researchers have been following multiple campaigns targeting the financial industry in Europe and the United States.
Download Complete Alert
Abstract
Radware researchers have been following multiple campaigns targeting the financial industry in Europe and the United States. These campaigns are designed to commit fraud via credential theft by sending MalSpam, malicious spam that contains banking malware like Trickbot and Emotet to unsuspecting users. If the users open the document, they will become infected, and the malware will harvest and extract data from the victim’s machine for fraudulent purposes. Once the data is retrieved from their c2 server, the stolen credentials will be used to commit fraud against the victim's bank account, leveraged in a credential stuffing attack or quickly sold for profit.
One of the things that make these two pieces of banking malware stand out is their ability to evolve and consistently update their modules to allow additional capabilities. Additionally, we have seen denial of service attacks in the past that have coincided with these security events. Occasionally attackers have been known to launch a flood of malicious traffic, known as a smoke screen attack, to distract network operators from other nefarious activity such as data exfiltration. These attacks typically will not exhaust network resources since the criminals still need access. These actions also highlight the fact that a DDoS attack are not always the first vector of attack but simply just an option in a series of attacks under the same campaign.
Infection Methods
Banking malware is designed to masquerade itself as a useful or non-malicious item with the purpose of infecting and gaining access to a user financial credentials. The malware is typically spread via exploit kits and spamming botnets, as well as packed inside a variety of free programs and cracked software. Once opened, the hidden executable performs its malicious activity in the background unannounced to the user.
The malware will establish a connection to the C2 server the attacker remote and unauthorized access to the infected machine to perform additional actions. After the initial infection, the banking malware will begin utilizing their modules to perform task such a compromising the user's browser to steal credentials, cookies and saved passwords as well as harvesting additional user data or moving laterally to further exploit devices on the network. Banking malware can also be the delivery vehicle for additional payloads once infected. It is also becoming common to see banking malware acting as downloaders for other banking malware.
Infected Attachment – A phishing email designed to trick the victim into opening a malicious document (typically a Word or Excel file). Once opened, the user will be prompted to enable macros so that the malware can execute.

Figure 1: MalSpam – Infected File with a Macro Containing Malicious Script
Embedded Link – In this scenario, the phishing email is designed to trick the victim into opening an embedded link that will download an infected file to the user’s device. Like infected attachments, the user will be prompted to enable macros when they download and open the document.
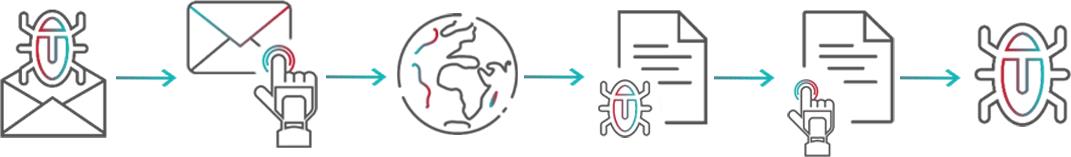 Figure 2: MalSpam – Embedded Link
Figure 2: MalSpam – Embedded Link