Over the last few days Radware’s Emergency Response Team (ERT) has been tracking a number of RDoS (DDoS for Ransom) campaigns from groups claiming to be the Armada Collective and XMR Squad.
Download a Copy Now
Abstract
Over the last few days Radware’s Emergency Response Team (ERT) has been tracking a number of DDoS for Ransom (RDoS attacks) campaigns from groups claiming to be the Armada Collective and XMR Squad. XMR Squad has evidently been spamming (sending volumes of emails) ransom demands to multiple targets / prospective victims while in contrast, the Armada Collectives campaign has focused mostly on the financial sector in Central Europe.
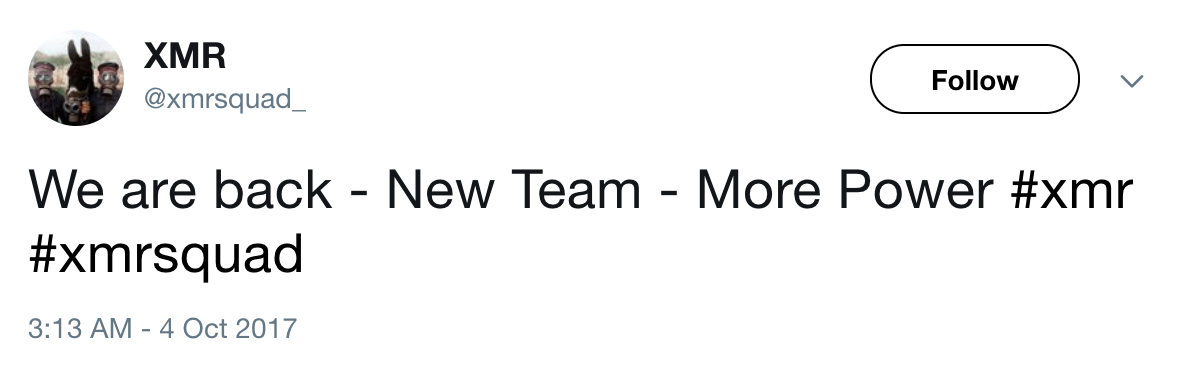 Figure 1: XMR Squad
Figure 1: XMR Squad
Background
The original Armada Collective first surfaced in 2015 with a series of attacks on banks, e-commerce sites and hosting services in Russia, Thailand and Switzerland. The group would send ransom demands to a few companies in a single industry demanding Bitcoin under the threat of a largescale DDoS attack. To demonstrate their power, they would launch a sample attack. If the ransom was not paid in the allotted time, the target would face a persistent, multi-vector attack.
In the spring of 2016, after a lull in RDoS attacks, a new group emerged calling themselves the Armada Collective, but their modus operandi had changed. The Armada Collective then targeted dozens of victims at once without launching a sample attack. RDoS attacks can be financially rewarding to cyber-criminals for little to no investment. Because of this, many other hacking groups started imitating this new methodology The result was an explosion in RDoS cases from hackers using infamous names like Armada Collective and Anonymous to spread fear and gain credibility for their threat.
This week a group claiming to be the Armada Collective re-emerged in central Europe. This group closely followed the modus operandi of the original Armada Collective and has been observed targeting a handful of cryptocurrency companies. The group sent a ransom note to its victims that is very similar to the original Armada Collective ransom note. The group has demanded 2 Bitcoin under the threat of a DDoS and has been observed launching sample and follow through attacks.
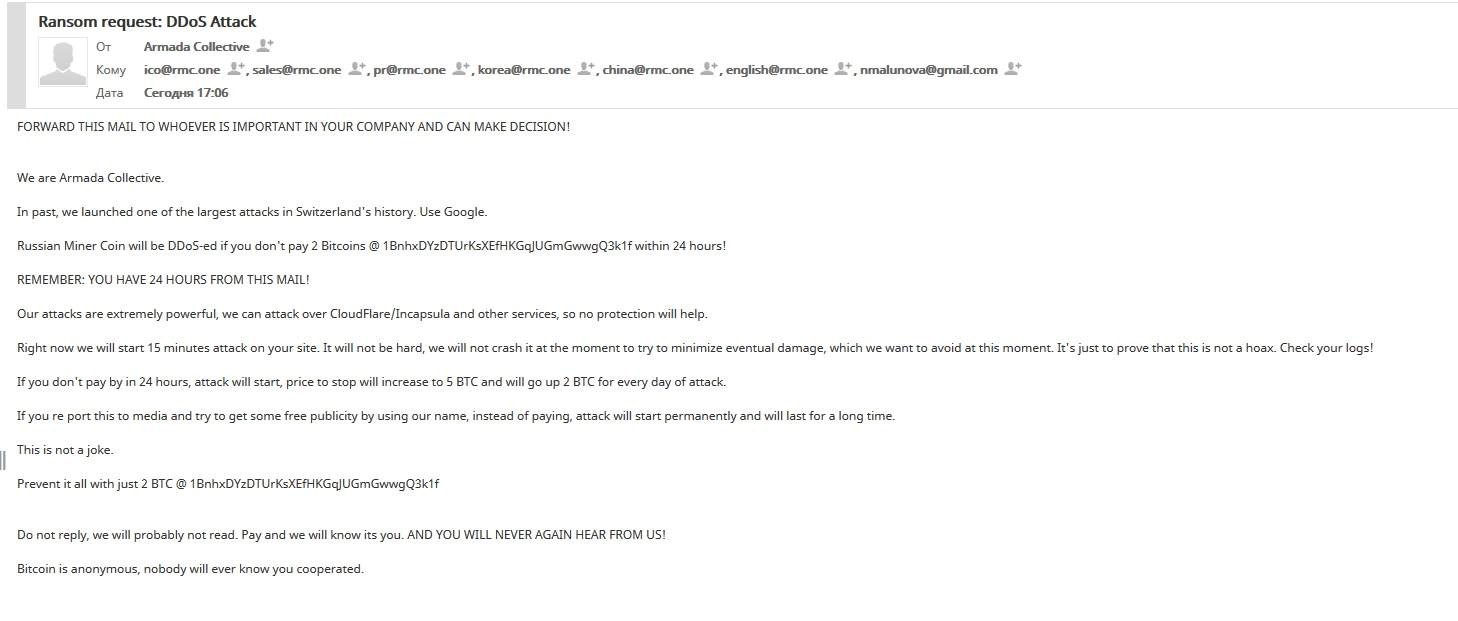 Figure 2: Ransom note sent to RMC from Armada Collective
Figure 2: Ransom note sent to RMC from Armada Collective
Earlier this year Radware’s ERT began tracking an RDoS group going by the name XMR Squad. This group was observed in May targeting companies in Germany and the United States. Targeted companies experienced a denial of service attack from the original XMR Squad if a ransom was not paid.
XMR Squad originally demanded 250 euros for testing their victim’s DDoS mitigation system and followed through with their original threats. Shortly after their disappearance a different group going by the name XMR Squad appeared requesting 2-3 Bitcoins under a threat of a 300-600Gbps attack. The time for payment in that campaign was 24 hours.
More recently the group going by the name XMR Squad has not been following through with their original threats. Radware’s ERT has received a large number of extortion letters from XMR Squad recently but never observed a sample or follow-through attack after the original group disappeared. The ransom demand in the most recent case was poorly written, looked nothing like prior demands and switched from BTC to Monero In addition, the window for payment was 10 days. This kind of time allows targeted victims time to put mitigation and an emergency plan in place.
It’s believed that XMR Squad has no idea who they have ransomed in this current campaign. In their note they state, “If you are Google, Microsoft, Amazon – you have nothing to fear. Just delete this email.” There is a low probability of XMR launching an attack during this campaign based on historical analysis, but with the Armada Collective launching attacks in central Europe again, those that receive any ransom note from an extortionist should take the proper steps to prepare for an attack in the event that XMR Squad changes their modus operandi.
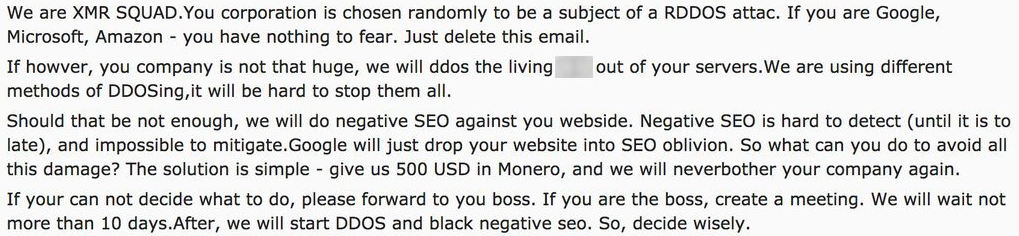 Figure 3: Ransom demand from XMR Squad (Reddit)
Figure 3: Ransom demand from XMR Squad (Reddit)
Reasons for Concern
In 2016, ransom was the number one motivation behind cyber-attacks; half of organizations were subject to this extortion threat, according to Radware’s
2016-2017 Global Application & Network Security Report. In parallel to the
ransomware plague, Radware witnessed an emerging trend of hackers (and copycats) that extort organizations by posing an imminent threat of
DDoS attacks – one out of six organizations was a victim. As IoT botnets have become more powerful, Radware has witnessed an increase in the number of DDoS for ransom attacks (RDoS attacks) threats that companies have received in 2017.
RDoS attacks can be financially rewarding to a cyber-criminal who enjoys making large amounts of money for little to no investment. Because of this, many hacking groups now imitate this model and spam similar ransom threats using other group names, with no intention of launching an attack.
The main reason for concern with the recent campaign is the pattern of not following through with an attack has been broken. The Armada Collective has recently demonstrated that its threats are serious by launching sample attacks and following through with the original threat. This demonstrates a shift in the RDoS threat landscape. Companies targeted should take these threats seriously as the group claiming to be the Armada Collective is launching attacks again.
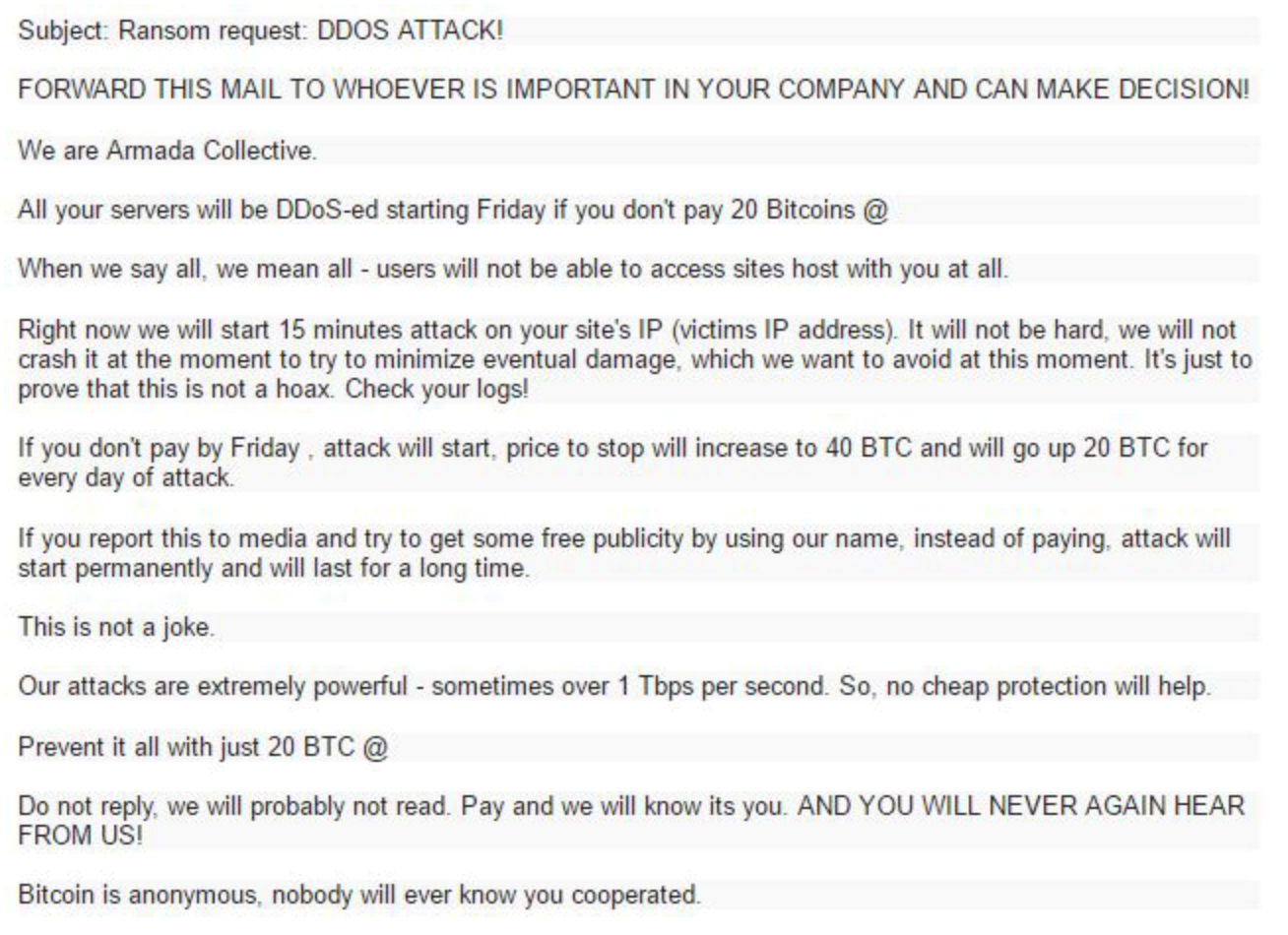 Figure 4: Original Armada Collective Demand (2015)
Figure 4: Original Armada Collective Demand (2015)
Targets
Armada Collective
- Financial Services in Central Europe (Crypto Currencies)
- Countries which seem to have a lot of focus on them:
- Slovakia
- Slovenia
- Eastern-Europe / Former Soviet Union (FSU) Crypto Currency companies
Attack Vectors
Most of these DDoS for ransom groups that actually launch attacks are running their own
network stressers, however some leverage publicly-available stressers to conduct campaigns. When experiencing a DDoS for ransom attack, expect 100+ Gbps and multi-vector attacks simultaneously. The attack is likely to be persistent and last for days. Attack vectors include floods using the following protocols:
- TCP RST
- TCP SYN
- SYN Flood
Dealing with a Ransom Letter
Companies are advised not to pay an extortionist and seek professional assistance for mitigating RDoS attacks. Such a threat usually provokes the need for a scrubbing service, ACL/BGP reconfiguration, as well as the usual DDoS protection essentials to assure uptime and SLA.
Evaluation – Is It Real or Fake?
Although it is almost impossible to determine whether a ransom note comes from a competent hacking group or an amateur unit, there are several indicators to distinguish between the two:
- The fake RDoS groups often request a different amount of money than the original
- "Real" groups prove their competence; fake groups exclude the "demo" attack
- These groups do not have official websites or target lists
- When hackers launch real RDoS attacks, they normally target less than a dozen companies under the same industry
- Look for suspicious indicators. Is this group known for DDoS attacks? In the case of Fancy Bear, they do not launch DDoS attacks.
Effective DDoS Protection Essentials
- Hybrid DDoS Protection - (on-premises +
cloud DDoS protection) – for real-time
DDoS attack prevention that also addresses high volume attacks and protects from pipe saturation
- Behavioral-Based Detection - to quickly and accurately identify and block anomalies while allowing legitimate traffic through
- Real-Time Signature Creation - to promptly protect from unknown threats and 0-day attacks
- A Cyber-Security Emergency Response Plan - that includes a dedicated emergency team of experts who have experience with Internet of Things security and handling IoT outbreaks
For further
DDoS protection measures, Radware urges companies to inspect and patch their network in order to defend against risks and threats.
Under Attack and in Need of Expert Emergency Assistance? Radware Can Help.
Radware offers a DDoS service to help respond to security emergencies, neutralize the risk and better safeguard operations before irreparable damages occur. If you’re under DDoS attack or malware outbreak and in need of emergency assistance,
Contact us with the code "Red Button".