Educational institutions are no strangers to cyberattacks. Every year they see a segment of their student population turn into threat actors, looking to manipulate the registration processes, delay tests, or target digital learning platforms for several reasons, including just for fun.
Read the Complete Advisory
Persistently Targeted
Educational institutions are no strangers to cyberattacks. Every year they see a segment of their student population turn into threat actors, looking to manipulate the registration processes, delay tests, or target digital learning platforms for several reasons, including just for fun. But more recently, external to the student body, extortion-based threat groups have entered the educational threat landscape with terrorizing attacks, further opening educational institutions up to a wider variety of threats.
Recent Wave of Cyberattacks
Over the last two months, following the return to school, there has been a wave of cyberattacks targeting educational resources worldwide. These attacks have ranged from denial-of-service attacks and defacements to credential stuffing attacks and extortion-based campaigns.
Credential Stuffing
Credential stuffing is a sub-technique of brute force account cracking. The attack consists of threat actors leveraging credentials obtained from a public data dump to access unrelated accounts via credential overlap due to users reusing the same password across personal and business accounts.
In September, threat actors were able to compromise Seesaw, an interactive learning platform used by elementary schools. The platform was targeted by a credential stuffing attack (T1110.004) that leveraged compromised accounts. The threat actors in this event used their access to send an inappropriate image to users for entertainment purposes.
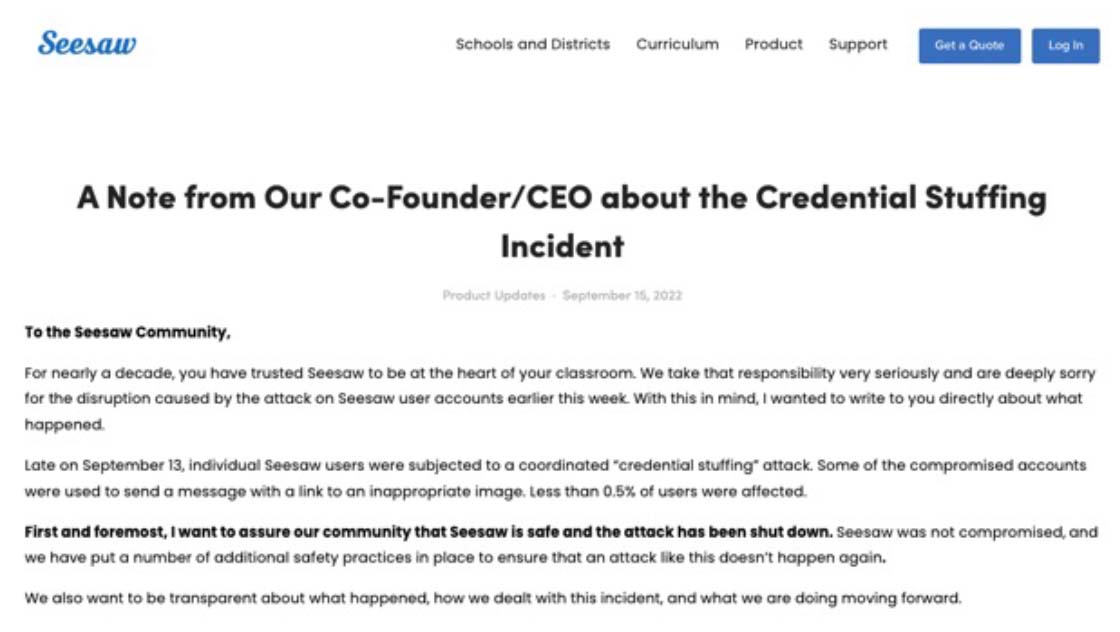 Figure 1: Seesaw Credential Stuffing incident
Figure 1: Seesaw Credential Stuffing incident
Defacement Campaign
A defacement attack is a widespread technique often used by threat actors to modify the visual appearance of a website. Typically, threat actors deface websites to spread political or religious propaganda related to a specific event. Defacements may also cause users to distrust and question the system's integrity post-compromise.
In September, Russian threat group NoName057(16) compromised and defaced (T1491.002) the Kyiv National University of Trade and Economics website. The threat actor launched the attack to spread pro-Russian propaganda in response to the Russo-Ukranian war.
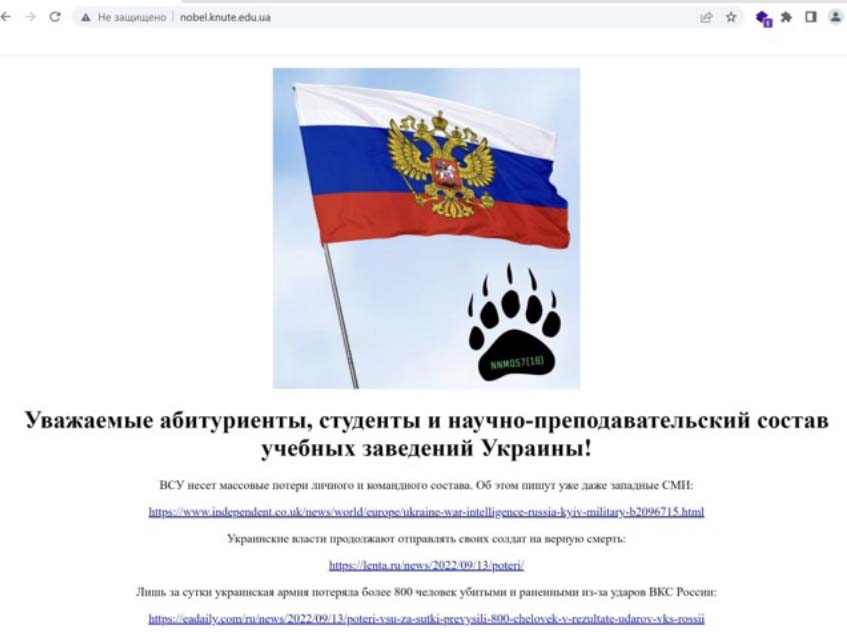 Figure 2: Kyiv National University of Trade and Economics website deface by NoName057(16)
Figure 2: Kyiv National University of Trade and Economics website deface by NoName057(16)
Denial-of-Service
An application exhaustion flood is a form of a denial-of-service attack that targets resource-intensive features of an application to cause service degradation.
In August, threat actors were able to take down QuickLaunch on the first day of school via an application exhaustion flood (T1499.003). QuickLaunch is an identity-as-a-service platform (IDaaS) that manages educational institutions' and organizations' human and device authentication, authorization, and access control. The threat actors flooded password.quicklaunch.io with repeated requests, causing multiple passwords reset calls to exhaust system resources and deny access to the application. As a result of the outage, students could not log in to their university email or learning management systems.
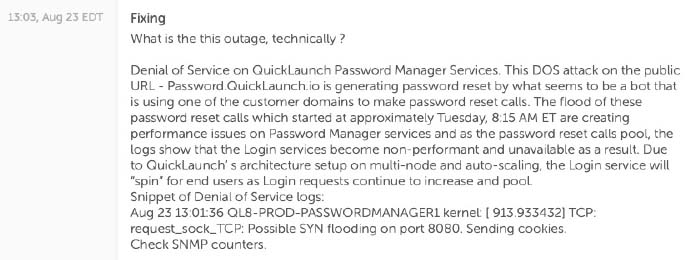 Figure 3: QuickLaunch’s notification of the denial-of-service attack
Figure 3: QuickLaunch’s notification of the denial-of-service attack