Federated Authentication
Federated authentication plays a pivotal role in modern identity management by allowing users to access multiple applications or services with a single set of credentials. This system is crucial for enhancing user experience by reducing password fatigue and simplifying the login process. It also significantly improves security by minimizing the number of attack surfaces, as users are less likely to resort to weak or reused passwords. Moreover, federated authentication streamlines the management of user identities for IT departments, offering a centralized approach to handle access controls and permissions. By leveraging trusted identity providers, organizations can ensure that user credentials are managed securely and efficiently, reducing the risk of data breaches. Additionally, federated authentication supports the modern work-from-anywhere model by providing secure and flexible access to corporate resources, regardless of location or device. This adaptability is essential for businesses looking to enhance productivity without compromising on security. While federated authentication introduces complexity into application architecture, the benefits of improved user experience and strengthened security posture often outweigh the challenges of implementation. Federated authentication is a cornerstone of enterprise security, balancing the needs for convenience and protection in the digital landscape.
The federated authentication process relies on a partnership between identity providers (IdPs) and service providers (SPs). The IdP is responsible for verifying user identities and issuing security tokens, which the SPs then use to grant access to their resources. Key elements of federated authentication include the trust relationship established between the IdP and SPs, the security tokens used as proof of authentication, and the protocols that govern the exchange of information between all parties involved.
SAML, OAuth, and OpenID are the three most commonly used protocols for Federated authentication.
Security Assertion Markup Language (SAML): SAML is an open-source authentication system that provides a secure method for transferring authentication details and data from the IdP to the service providers. SAML makes use of XML files to communicate the authentication data between the IdP and the SPs.
This is ideal for authentication of anything web-based, but not effective in the authentication of apps and software that are not web-based.
OAuth 2.0: OAuth is much more of an authorization protocol than an authentication protocol. The difference is authentication simply verifies a user, but authorization verifies what all tools, apps, and resources a user can access.
OAuth 2.0 makes use of a token-based authorization. It can give users restricted access to resources and apps without revealing the authorization credentials. This protocol can eliminate the process of creating an account to access OAuth-enabled apps and tools.
OpenID Connect (OIDC): OpenID Connect is more of an extension to OAuth 2.0 and it allows organizations to verify users using an authorization server. Although the OpenID connect uses an authorization server it deals with the authentication of the user rather than the authorization. Even though OpenID can perform most of the functions of OAuth 2.0, it is a bit different from it. OpenID connect is more API-friendly, so it can be used for web-based tools as well as apps. Also, OpenID provides more secure encryption to the authentication token.
Single Sign-On: Single Sign-On is a concept that allows users to create accounts and access tools, apps, or resources within a service, using the same set of credentials from another service in the same domain. It is like logging into your Google account to access different services offered by Google. SAML and OIDC are the most widely used federation protocols for web based single sign-on.
Alteon Authentication Capabilities
An Application Delivery Controller (ADC) functioning as a federated authentication service provider can offer numerous benefits. It simplifies the development process by separating user authentication from application code and delegating it to a trusted identity provider. This approach minimizes the need for user administration and enhances the user experience by allowing them to use a wider range of identity providers, such as corporate directories or social accounts. Moreover, it supports a claims-based access control model, where applications authorize access based on user claims contained in security tokens. This model is particularly beneficial in multi-application environments where users interact with various services provided by different organizations. By implementing federated authentication, an ADC can help reduce security vulnerabilities, as it ensures immediate deprovisioning of user access when necessary and streamlines user management for administrators.
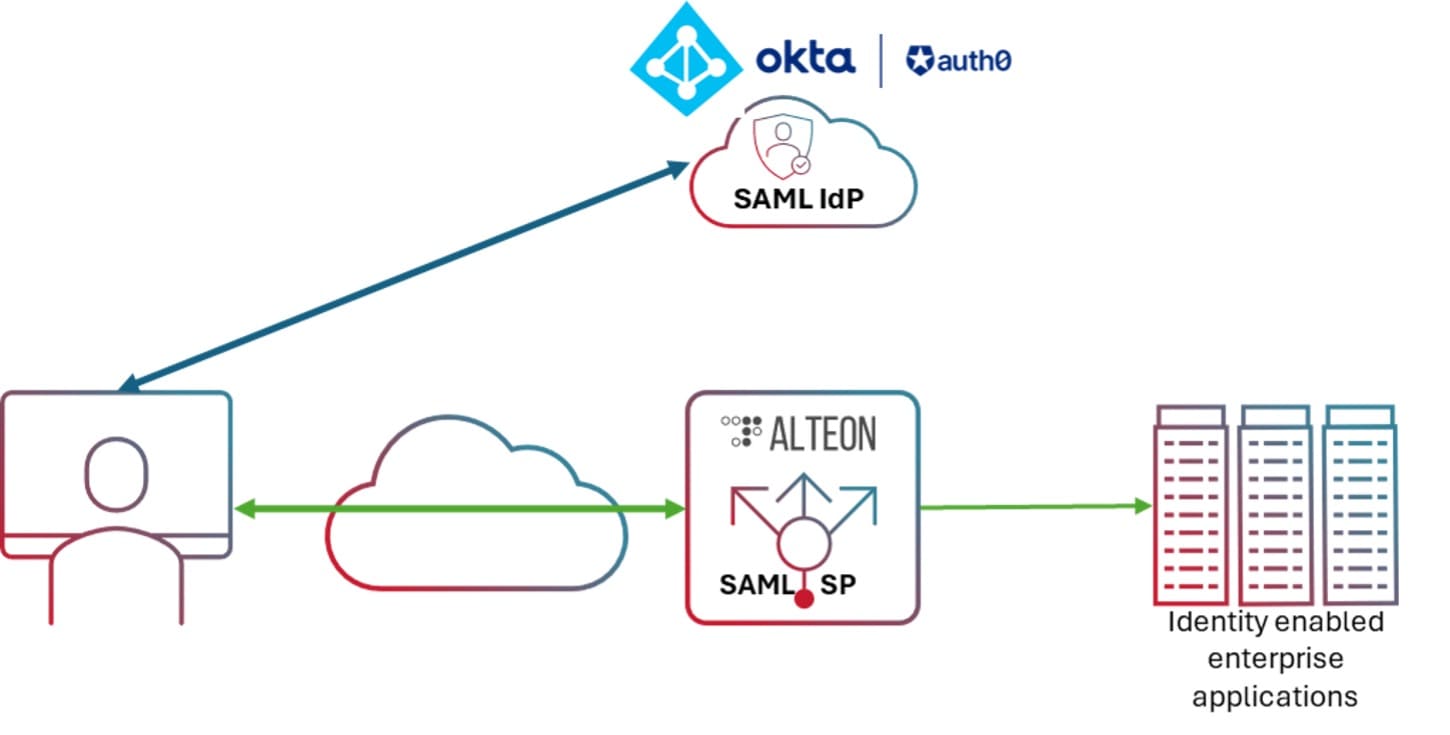
The following example illustrates how Alteon serves as an authentication gateway for application in a SAML environment. Alteon acts as a SAML SP and evaluates client requests when users attempt to access protected applications. If the client is unauthenticated, Alteon redirects the request to the SAML Identity Provider (IdP) for authentication.
The integration of SAML SP within Alteon offers several benefits:
- Enhanced Security: By leveraging SAML, Alteon can provide a more secure single sign-on (SSO) experience. User access is authenticated via SAML assertions, reducing the need for multiple passwords, and decreasing the risk of password-related breaches.
- Improved User Experience: Users enjoy seamless access to multiple applications with a single set of credentials, streamlining the login process and improving productivity.
- Flexibility and Interoperability: Alteon, as a SAML Service Provider (SP), is designed to be compatible with a wide range of Identity Providers (IDPs), including cloud services like Microsoft Entra (formerly Azure AD) and Okta, as well as on-premises solutions. This interoperability is crucial for organizations that rely on different authentication systems across their applications and services.
- Attribute Handling: Alteon can extract user information from the SAML token, which can then be passed on to backend servers or utilized for further authorization.
- Ease of Configuration: Alteon supports metadata files for configuration of both SAML SP and IdP, simplifying the setup process. Administrators can export the SP metadata file from Alteon and import the IdP metadata file to Alteon, making it easier to manage SAML configurations on both Alteon and the IdP.
Conclusion
To encapsulate, the integration of authentication capabilities within Alteon provides significant improvement in the realm of secure access management. This capability not only fortifies security measures but also enriches the user experience and simplifies administrative tasks. The administrative tasks become more manageable with this feature, as it reduces the complexity involved in managing access controls.
For organizations that are on the lookout for efficient ways to refine their access control procedures, this feature serves as an invaluable resource. It extends their cybersecurity arsenal, equipping them with a tool that is not only effective but also easy to manage.
To learn more about how Radware can help protect your application check out check out Alteon solutions