Last year 86% of enterprises were impacted by a DDoS attack (Radware annual security report). This means 86% of businesses suffered outages that at a minimum impacted their employees and as a worst case, impacted their customer experience and revenue. There’s no room for mistakes when choosing your security technology and approach. Enterprises need to ensure that the selected vendor is capable of defending its network and applications from the latest DDoS burst and multi-vector attacks.
What happens to businesses without the right protection?
Here’s an example. An APAC bank became the latest target of a DDoS attack campaign which began in early September. The attacks initially impacted the bank’s primary service provider. Although the bank deployed Akamai’s Cloud DDoS protection service a few days before the attack, this service was not able to identify and mitigate all bad traffic. Bad traffic “leaked” from the Akamai solution, impacting the bank’s Checkpoint Firewalls, causing additional service outages. Unfortunately for the bank, these outages captured public attention.
The bank’s IT team initially thought they could handle the DDoS attacks with their existing solutions. However, after more unsuccessful mitigation attempts including damaging news stories, the bank’s management called a meeting between their IT team, Cisco and Radware to architect a solution.
[adbutler zone_id="276005"]
SOLUTION
The team recommended Radware’s on-premise DDoS device to provide enhanced protection from the latest attack vectors which the Akamai service couldn’t handle.
In mid-September the first appliance was deployed inline, initially in Report mode. Ten days later, the bank IT team needed assistance with a large volumetric UDP/TCP flood attack, with burst characteristics, against its VPN. The Akamai Cloud DDoS solution handled up to 100 Gbps of the attack but “leaked” another 2-2.5 Gbps of bad traffic, causing remote connectivity issues and disruption to their banking operations. The attack traffic leaks continued until Akamai initiated blacklists for the bad traffic.
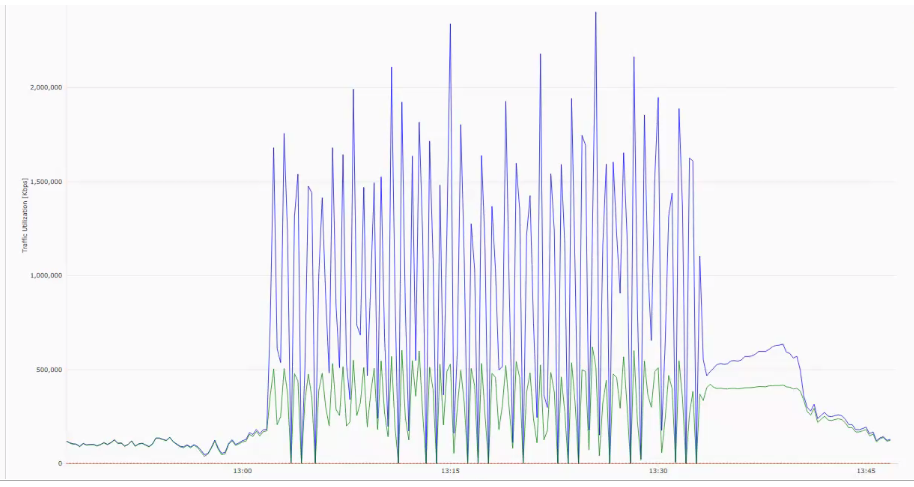 Figure 1. Attack traffic leaks from Akamai Cloud DDoS solution halted by blacklisting
Figure 1. Attack traffic leaks from Akamai Cloud DDoS solution halted by blacklisting
[You may also like: Smart DDoS Protection During the COVID-19 Crisis]
The DDoS protection appliance in Report mode immediately identified attack vectors the Akamai service was not able to identify and mitigate, including UDP FRAG and ICMP/UDP/DNS reflection attacks. Radware’s DDoS solution offers protection against advanced DDoS attacks, including Burst attacks, low and slow attacks, UDP fragmentation and SYN Floods, that cloud scrubbing services are unable to provide. Cloud services, by definition, look only at inbound (ingress) traffic; they are unable to protect against attack vectors which require two-way visibility into traffic.
Once the Radware team performed a thorough traffic analysis to ensure there were no false positives and moved policies from Report to Block Mode, the bank was fully protected. The bank appreciated Radware’s technology to identify and defend against attacks . Since the incident, Radware’s DDoS protection appliance has been installed in all of the bank’s data centers. The bank has not suffered any additional outages and now enjoys the benefits of Radware’s DDoS protection.
For additional information, see the bank case study here.
Questions to Ask In Order to Evaluate Security Vendor Capabilities
When evaluating security solutions, make sure to ask vendor whose products you’re evaluating the following questions:
- Can you ensure business continuity under attack?
- What attacks does your solution defend against?
- Do you use behavioral learning algorithms to establish ‘legitimate’ traffic patterns?
- How do you distinguish between good and bad traffic?