The trend toward remote work, which was initiated by the pandemic, still persists today. To minimize in-person interactions, individuals and companies are increasingly relying on remote access. Consequently, there has been a rise in attacks on converged networks that integrate voice and data, making them vulnerable to malware and security breaches at the network and application levels. As a result, VoIP services are prone to disruptions from both known and unknown (zero-day) attacks, just like other areas of information security. This places greater emphasis on service providers to meet evolving cybersecurity requirements in order to enhance the customer experience (CX).
Collaboration Tools Have Quality and Reliability Challenges
VoIP and video conferencing systems, including Unified Communication as a Service (UCaaS), rely on two protocols — Session Initiation Protocol (SIP) and Real-Time Protocol (RTP). While both protocols support Transmission Control Protocol (TCP) for direct communication, their primary choice is User Datagram Protocol (UDP). It’s better for real-time or live data transmission that can’t afford delays. However, UDP lacks packet delivery assurance and packet ordering capabilities found in TCP, which can lead to quality issues in VoIP and video conferencing systems. UDP is more about speed, TCP is more about reliability.
Collaboration Tools are Vulnerable to DDoS Attacks
The UDP protocol used by these systems is vulnerable to various types of attacks. This includes Layer 4, volumetric attacks, such as UDP Floods, UDP Garbage Floods, Reflection Floods and direct Layer 7 attacks targeting RTP and SIP (e.g., SIP Invite and Register Floods). In addition to these attacks, common UDP Flood attacks may include sending garbage payloads or leveraging reflection and amplification attacks on service protocols, like DNS, NTP, SSDP and Memcached for amplification attacks.
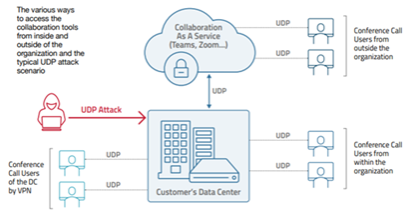
Attackers exploit normal behavior to cause congestion on targeted networks. They achieve this by sending numerous UDP datagrams from either legitimate or spoofed IP addresses to random ports on a target server. The excessive traffic overwhelms the server, preventing it from processing every request and consuming all available bandwidth. Consequently, the server sends "destination unreachable" packet replies via ICMP (Internet Control Message Protocol), which confirms that no application was listening on the targeted ports.
Radware DefensePro: Comprehensive Protection for VoIP and Unified Communications Networks
Radware's DefensePro solution offers a multi-layer defense system that addresses both known and unknown VoIP attacks through behavior- and signature-based approaches. By combining both approaches with machine learning (ML) capabilities, DefensePro provides advanced threat detection and prevention mechanisms. More importantly, it operates seamlessly in high-speed environments, minimizing the impact of traffic latency and ensuring scalability.
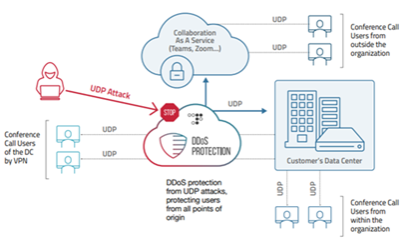
With DefensePro, accurate detection and prevention technologies are employed, which significantly reduces false positives and effectively prevents voice quality degradation. This makes DefensePro an ideal solution for safeguarding VoIP and unified communication networks; it ensures uninterrupted and secure communication.
For More Information
While the move to remote working occurred seemingly overnight, there’s no question it’s here to stay. The reliance organizations now place on VoIP and unified communications will only increase. Just remember that neither are immune to cyber-attacks. That’s why contacting the cybersecurity experts at Radware should be one of the first steps you take, whether creating or enhancing your security roadmap. You can reach them HERE. This is where you can get more information about Radware DefensePro. It provides automated DDoS protection from high-volume, fast-moving, encrypted and short-duration threats. If you’re using VoIP and/or unified communications, DefensePro needs to be part of your security plan.