Over the last few years, the network and application threat landscape evolved and accelerated significantly. Organizations had to deal with several highly critical vulnerabilities, zero-day exploits, organized cybercrime groups, patriotic hacktivists and nation-states working in the shadows, hiding behind and between freedom fighters. The invasion of Ukraine by Russia brought with it a slew of patriotic crime groups on both sides of the war. Those groups democratized denial of service (DoS) attacks, making DoS accessible to a growing crowd of volunteers. After a year of causing nuisance and trouble across the globe, these new threat actors more became experienced, and their tactics and tools improved considerably. Hacktivism is not slowing down, quite the opposite, the threat from hacktivists is growing in both the number of groups as well as their targets. Their tactics have improved, automating their attacks to target more organizations, and hit where it hurts most by moving to more effective attack techniques. Alliances have come and gone, not every group sees eye to eye, but when objectives are aligned, the enemy of my enemy is my friend.
2021 – the year of accelerated digitalization and increased attack surfaces
COVID-19 globally affected digital transformation. The pandemic accelerated the adoption of digital technologies and accelerated many businesses' migration to the cloud while working from home became the new normal. As businesses migrated more applications to the public cloud, their attack surfaces expanded quite rapidly and significantly. The need to expose applications previously running within a secured perimeter and to allow access for a remote workforce increased the vulnerability of the organization against relentless initial access brokers looking to cash in a big paycheck from ransomware operators. Accelerating projects with the same means cannot be done without trade-offs. Soon a slew of new applications with known and unknown vulnerabilities, that were once contained within a secure perimeter, got exposed to the internet, a public service free and accessible for all.
2021 started in the shadow of the SolarWinds supply chain attack. By January, a ransomware assault led Colonial Pipeline's executives to halt their oil distribution. As the year drew to a close, a vulnerability in the widely used log4j logging component rattled the digital realm. This flaw, prevalent in countless Java-based systems, became public knowledge in December 2021, causing a massive stir in the cybersecurity community. This security lapse enabled attackers, without authentication, to utilize easily accessible exploits for remote command execution (RCE). Many experts branded it not just as the most critical flaw of the year but possibly the worst of the decade.
In October 2021, UK VoIP providers faced multiple Distributed Denial of Service (DDoS) assaults. Bandwidth.com later reported a significant financial hit due to these attacks, with losses of $700,000 in their Q3 revenue. The company projected a staggering $12 million in combined real and reputational damages. 2021 marked a year when Ransom DoS made a dominant appearance in the DDoS threat scene.
The year also witnessed significant crackdowns on organized crime. In Europe, unprecedented arrests in drug trafficking took place, largely credited to prior actions by European police who infiltrated encrypted devices used widely by criminals. In the cyber domain, collaborative actions between Eastern and Western entities delivered a tough hit to ransomware activities. This partnership created a challenging environment for ransomware operators and their affiliates. Notably, Russian crime groups, primarily targeting organizations outside Russian territories, faced a bleak future when Russian officials apprehended members of the REvil group within their borders.
2022 – the start of an invasion
Amidst extended lockdowns, the information technology industry was confronted with an evolved reality. The prevalence and vast resources behind cybercrime reached alarming levels. The intricacies of hybrid architectures made defense more challenging, creating expansive threat landscapes.
Compounding these issues, there was a shortage of skilled security professionals who could pick up the pieces and close the gaps quickly. Cybercrime was the new pandemic, and it was growing year after year.
On February 24, 2022, the world was shaken with the news of Russia's special military operation against Ukraine. This date, which marked the start of the war, will be engraved in our memories for a long time. Preceding the army movements, cyber operations attributed to the state actors of the Russian nation were already, for some time, waging against Ukraine.
What unfolded were multifaceted cyber battlefronts, where the digital warfare spanned various layers and was not just confined to the countries in direct conflict. New cyber legions emerged; , some rooted in government initiatives, others grown out of moral patriotism. Both cybercrime factions redefined their arsenals, reset their goals, and deployed aggressive cyber strategies with intentions to destabilize governments, sow discord, and control narratives.
The lines of the battlefields were often blurred. Patriotic hacktivist operations served as convenient fronts for the warring nations. Identifying the actual perpetrators became challenging, and any assertions came with the risk of eliciting counterattacks, potentially escalating conflicts. It remains ambiguous which groups operate autonomously for a common goal, and which are mere puppets in a strategic game of thrones.
While the Russia-Ukraine conflict dominated headlines, other cyber adversaries did not suspend their activities. As the world's focus remained on Russia, numerous cyber entities operated stealthily. In June 2022, a joint advisory from the CISA, NSA, and FBI (AA22-158A) highlighted that state-backed actors from the People's Republic of China persistently exploited known vulnerabilities. Their objective was to establish a vast network of compromised infrastructure spanning both public and private sector organizations. The advisory accentuated how these actors infiltrated major telecom and network service providers.
The ethos for the year seemed to be “DDoS is not a crime." Vigilantes on both sides of the Russo-Ukrainian war leveraged whatever knowledge and resources they had to support their nation through hacking campaigns, convinced of the fact that their actions were morally acceptable and legal. 2022, without a doubt, became the year where network-level DDoS reached new heights, both in terms of volume and size.
2023 – Denial of Service Attacks Moving Up the Stack
The cybersecurity landscape continued to rapidly evolve in the first half of 2023, with a significant shift in Denial-of-Service attack patterns. There is a growing trend where DoS attacks are ascending to layer 7, targeting not just the online applications and their APIs but also essential infrastructure such as the Domain Name System (DNS). In the first half of this year, there was a considerable growth in DNS query floods while Web Distributed Denial-of-Service (Web DDoS) attacks have become more sophisticated, utilizing high Request Per Second (RPS) traffic combined with randomization of multiple elements of the request to create seemingly legitimate traffic. Such techniques have been adopted by multiple hacktivist collectives, including the likes of Anonymous Sudan and NoName057(16).
Figure 1: 2023 Major Attack Trends (*)
Hacktivists constitute a major part of the L7 DDoS problem. The effectiveness of these attacks has been significantly amplified by nationalistic volunteers participating in crowdsourced botnets or by equipping volunteers with custom attack tools and comprehensive tutorials on carrying out such attacks.
Though HTTPS Floods have existed for some time and might be perceived as old news, their scale and force have surged remarkably in recent times. Concurrently, the craftiness and aggressiveness of the culprits have been on an upward trajectory.
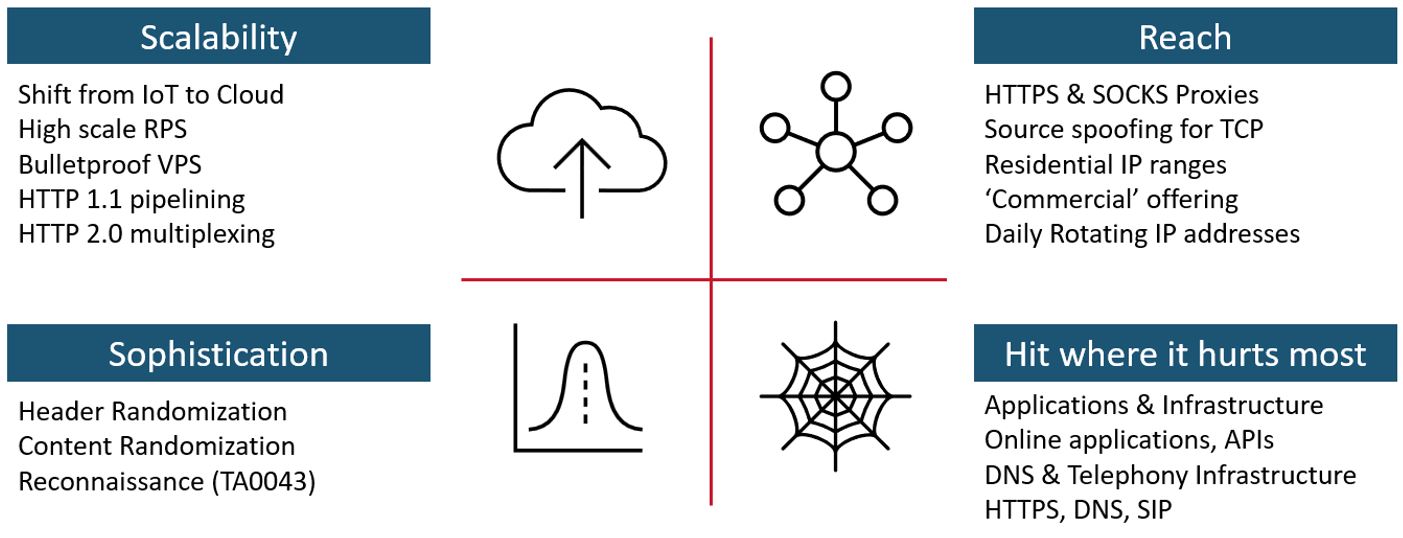
Figure 2: 2023 Tactics and Techniques
A noticeable trend is the transition of malicious actors to cloud-based operations. Instead of relying on compromised IoT devices, they are now leveraging the scalability and cost-effectiveness of cloud services with high-speed internet connections. This allows them to orchestrate a limited number of powerful nodes instead of compromising and maintaining large networks of devices without getting noticed. The advantages are considerable: they maintain control over their servers, suffer no loss from device reboots, and run a lower risk of detection by security researchers. By utilizing bulletproof hosting and proxy services that provide frequently rotating residential IP addresses, they have established the perfect platform to launch high-frequency, sophisticated Web DDoS attacks.
Concluding
Cybercriminals have redirected their attacks in 2023, targeting online applications and their surrounding infrastructure. While overall global DDoS activity held steady compared to 2022, attention has shifted from network DDoS attacks to more sophisticated, application-level Web DDoS attacks. Organizations must adapt as attackers turn to the cloud for additional scale, agility, and control.
Learn how the threat landscape changed in the first half of 2023 by reading our 2023 H1 Global Threat Analysis Report.
(*) Images created using Microsoft Bing image creator powered by DALL-E (https://www.bing.com/images/create/)