How do real world DNS Flood look like? What is the impact on your DNS infrastructure and what can you do to boost your DNS security posture?
2023 DNS Flood Trends
We noted a considerable surge in DNS floods during H1 2023. DNS Floods—application-layer attacks that overload a server’s capacity to manage DNS requests—have increased in scale since Q4 2022, with the largest attack in Q2 2023 reaching a rate of 1.29 million DNS queries per second. Despite this, the traffic volume of these attacks remained under the 1Gbps threshold as they aimed to overload servers rather than saturate internet connections. The most common DNS query used in DNS Floods in H1 2023 was the regular hostname to IPv4 query, accounting for 76.5% of all DNS Floods, followed by MX, TEXT, OTHER, and AAAA queries.

Largest DNS Flood in Q2 of 2023 1.29 million DNS queries per second

DNS amplification produce the highest volume of amplification attacks at 61.6%
DNS amplification produced the highest volume of amplification attacks at 61.6%. DNS Amplification Attack is a type of network-level, reflection-based, volumetric DDoS attack where the attacker crafts a DNS query packet with a forged source IP address (the victim’s). It sends it to a legitimate open DNS resolver which subsequently replies to the victim with a large amount of data. The goal is to overwhelm the victim’s network with traffic.
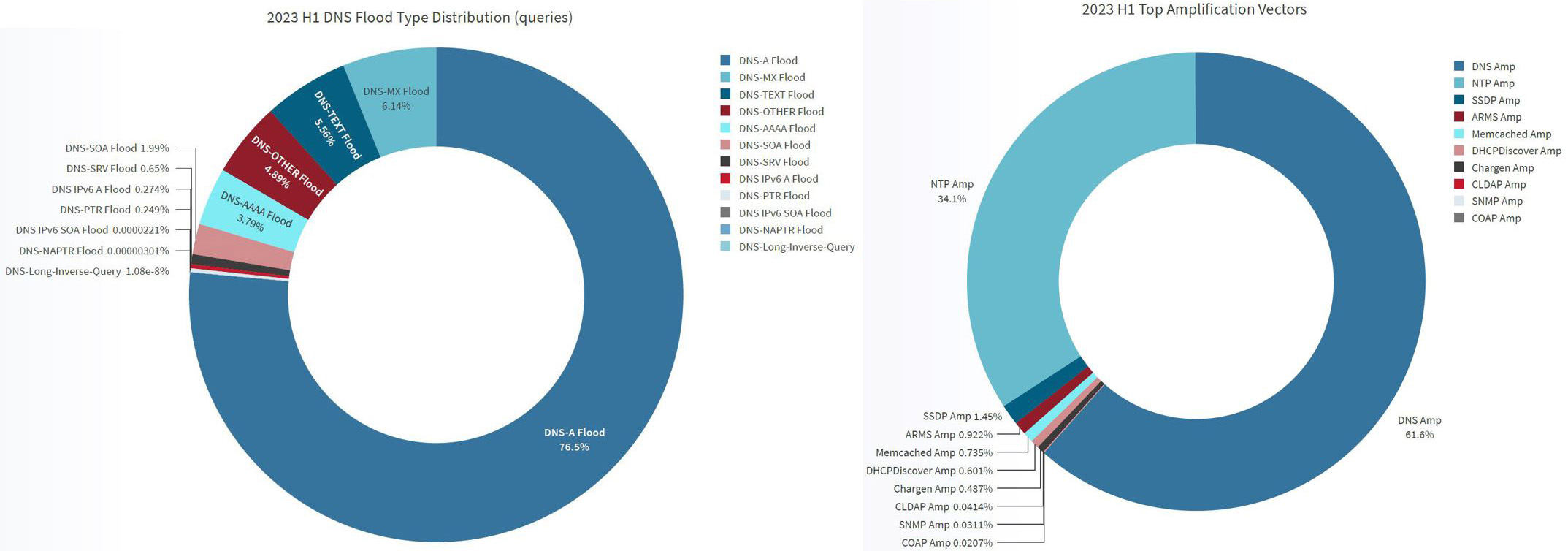
DNA A query type flood was top attack vector comprising of
76.5% of all DNS flood in H1 of 2023
DNS Amplification vector produced majority of amplification attacks
in H1 2023
Real-world DNS Flood Attacks
We analyzed real-world DNS flood attacks, selected from the many DNS flood attacks blocked by Radware DDoS protection during H1 2023. The analysis of the DNS flood attacks produced interesting insights that can hint on attacker's agenda, and attack techniques. These insights are essential to help security managers understand the risks of DNS flood attacks and improve the DNS security posture.
Key insights from DNS flood attacks analysis:
Global DNS Attack Campaign: During H1 2023 there was a surge in DNS flood attacks affecting multiple organizations around the world. Looking at the DNS attacks and their characteristics we suspect that they belong to one or more global DNS attack campaigns. We were able to identify significant DNS attack activity world-wide and were able to identify correlations between attack events to different DNS servers.
Attack Agenda – The organizations that were targeted by these DNS flood attacks all belong to the financial and commercial segment. We detected and mitigated DNS flood attacks targeting banks, retailers, insurance etc. This can hint on the DNS campaign's agenda, and help similar organizations protect their DNS services.
Attack vector: There was a single attack vector repeating in all DNS attacks and that is the random subdomain, also known as DNS water torture. Interestingly, we identified different types of invalid subdomains used in the attacks. In some cases, it was purely random with high entropy1 including case randomization and in other cases the attack subdomains were human-readable, but non-existent. We suspect that attackers are trying to avoid detection by entropy methods. For example, if we consider example.com as the target domain, then the random attack queries can look like – rThnBzl.example.com, tngkoK8nbdms.eXamPle.com, geTalup5Nmk.examPle.Com and the human-readable look meaningful but non-existent for example itsecurity.example.com, news4all.example.com etc
What is a DNS Water Torture / Random Subdomains Flood?
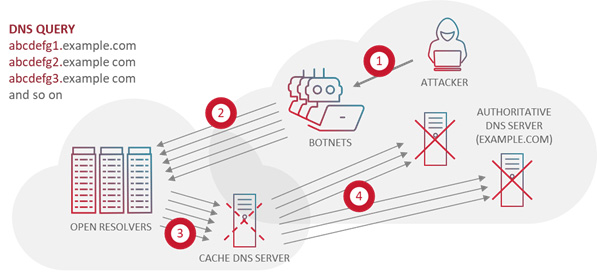
In this attack vector, the attacker sends a massive number of requests for non-existent subdomains of a valid and existing domain. The attacker typically sends the requests through different recursive resolvers. This causes the authoritative server to consume resources trying to resolve these non-existent subdomains, eventually leading to a denial of service.
The attacker’s objective is to disrupt the DNS service and make the websites and online services that rely on it inaccessible. These attacks exploit different aspects of the DNS protocol, making them challenging to defend against and highlighting the importance of implementing robust DNS security measures.
Attack botnet(s) and scale: When looking at the source IPs of the attack events, we identified many repeating source IPs and IP blocks (CIDRs) that generated more than a single DNS query. We identified that a relatively small portion of queries originated from open resolvers. This implies that most attack sources were non-spoofed, but rather coming from a real IP botnet. We identified similarities between attack patterns which can imply that the attackers used the same attack tools, and perhaps even the same botnet to launch more than one DNS flood attack. This also streteghn our suspicion that this is a global DNS attack campaign.
How to stay protected
Now that we know more about real-world DNS attacks, we can take the insights towards designing a robust DNS security solution.
Here are the most important elements you should not compromise on:
Automation: make sure your protection can automatically detect and mitigate DNS water torture attacks. This DNS attack vector that can degrade or even halt the DNS service. If you rely only on manual rate limits there is a risk of false positive, leading to blocking legitimate DNS queries. In addition, without automation, constant tuning will require high expertise and lead to longer time to mitigate attacks.
Attack isolation: make sure your protection can automatically isolate the domains under attack and isolate the attack pattern. This is a critical step to achieve surgical attack mitigation, with zero interference to legitimate DNS queries. If you rely on experts to manually identify the target domains under attack, it will take long time putting your DNS infrastructure at risk.
Fast time to mitigate: make sure your DNS protection can detect and mitigate a DNS flood immediately, in a matter of seconds. Every second counts, so you should prefer solutions that rely only on ingress traffic for detection, before there is an impact on the DNS servers. Protections that inspect DNS responses for detection pose a risk on the DNS service. Waiting for bad responses can take too long, and during that time the DNS server may slow down or fail.
Stateless, first line of Defense: make sure you are protected from DNS floods with a stateless solution that protects your entire infrastructure. That is the only way to ensure protection from high-rate DNS floods. A strong DNS server is important but cannot protect from a DNS flood that can risk your entire infrastructure long before reaching the DNS server.
Click HERE to get more information about Radware’s DDoS Protection solutions and how we keep organizations secure and safe from cyberattacks. If you’d like to speak with a Radware cybersecurity professional and better understand how to protect your applications and infrastructure, reach out to us HERE. We’d love to hear from you.