The escalating pace of digital transformation and the critical need to increase business agility are two of the main factors driving organizations to the cloud. By 2022, the global analyst firm Gartner predicts that the revenue from worldwide public cloud services will reach a massive $354.6 billion.
As the rate of adoption of the cloud continues to increase, customers prioritize the security and availability of applications as they move to the cloud. For example, distributed denial-of-service (DDoS) attacks, attempts to exhaust an application’s resources, are not uncommon. These attacks can render application unavailable to legitimate users, and potentially damaging hard-earned user trust.

DDoS Risks in Public Clouds
In public clouds, DDoS attacks can be targeted at any endpoint that is publicly reachable through the Internet, or from within the cloud environment.
There are two main attack categories:
- Volumetric network attacks—These are traffic floods (for example UDP/TCP reflection attacks) that exhaust resources by creating high bit/s or packet/s rates. These attacks can overwhelm compute resources, resulting in auto-scaling, which poses a moving-target infinite-billing risk, and in other cases might impact applications’ availability when auto-scaling is neither supported (for example, “lift-and-shift’ applications) nor required (for example, monolithic applications such as gaming rooms).
- L4-L7, smart attacks—These attacks impact customers’ applications. Resource-exhaustion attacks (for example, TCP floods) exploit vulnerabilities in the L4 protocol stack to render a target inaccessible. Application attacks like HTTP/S floods take out services by exploiting weaknesses in the application, which disrupts its ability to normally serve legitimate traffic. HTTP/S attacks such as cache-busting, bypass CDN services to overwhelm application services with randomized URL queries, resulting in over-consumption of CPU resources.
[You may also like: Layer 7 Attack Mitigation]
DefensePro VA DDoS Protection
Radware's DefensePro VA for AWS smoothly integrates within the AWS VPC environment to provide inline DDoS protection, ensuring applications’ availability and security.
Radware's DefensePro VA for AWS provides the following benefits:
- Comprehensive DDoS protection coverage—Patented machine-learning algorithms enforce positive and negative security models to reduce false-positives.
- Keyless protection against encrypted application attacks—Encrypted HTTP/S floods impose a challenge for all DDoS mitigation techniques, since traffic decryption is needed for visibility into L7 attack patterns. DefensePro VA provides keyless protection against in-session floods and brute-force attacks without scarifying data privacy.
- Customized and precise DDoS protection tailored to the applications’ security needs—DefensePro VA provides granular DDoS protection policies according to specific application use cases and behavior.
- North-south and east-west protection—Protects against DDoS attacks from the Internet, as well as from within the AWS environment.
- Full control and integration with on-premises security policies—Leverages already-available security policies on-premises for coherent security protections across hybrid cloud deployments.
[You may also like: Deploy and Scale DDoS Protection in the Public Cloud]
DefensePro Integration with AWS Gateway Load Balancer
AWS Gateway Load Balancer is a new managed service that makes it easy to deploy and manage a group of horizontally scalable and fault-tolerant inline network virtual appliances, such as DefensePro. AWS Gateway Load Balancer works in a transparent manner without altering packet headers or payloads, simplifies security inspection, and prevents changes to users and applications.
Radware is participating in the launch of Gateway Load Balancer, integrating and testing DefensePro VA to guarantee mature and stable interoperability.
[adbutler zone_id="276005"]
Deploying DefensePro VA in a Dedicated DDoS Inspection VPC
There are many ways to deploy DefensePro VA with AWS Gateway Load Balancer to achieve north-south and/or east-west inspection. AWS Gateway Load Balancer adheres to multiple deployment use cases and network architectures. The AWS Gateway Load Balancer provides the VPC Endpoint Service, which allows customers to mimic on-prem networking paradigms, such as hub-and-spoke, across different VPCs and accounts. Customers can create a VPC dedicated to DDoS inspection where a group of DefensePro appliances is deployed with a Gateway Load Balancer. By utilizing AWS Ingress Routing, customers have full control of traffic routing to and from the DDoS inspection VPC.
The following network topology illustrates a simplified deployment of DefensePro VA in a dedicated DDoS inspection VPC.
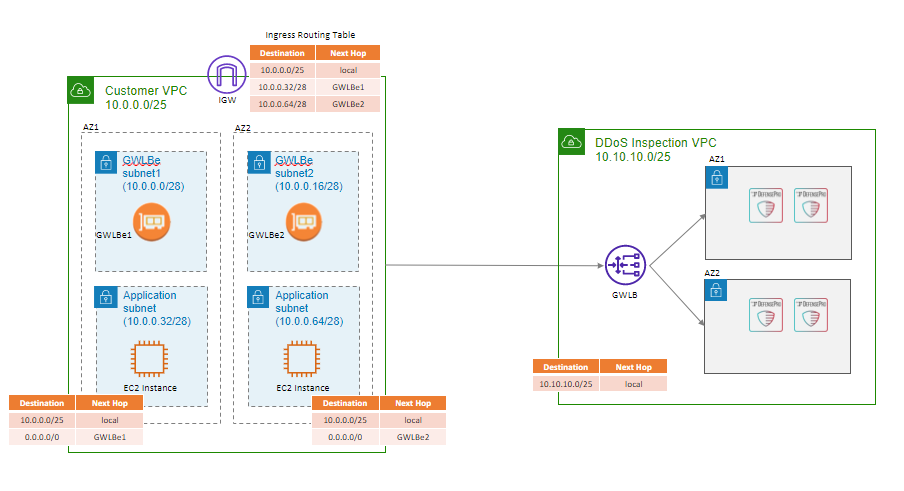
There are two VPCs: the Customer VPC, which is Internet-facing, and DDoS-Inspection VPC. The Customer VPC has two Availability Zones for high availability of applications instances. Each zone includes an AGWe (end-point service) that steers traffic to/from the Gateway Load Balancer located in the DDoS-Inspection VPC. A group of DefensePro VAs is deployed in the DDoS Inspection VPC, spanning two Availability Zones, for high availability. The Gateway Load Balancer load-balances connections across multiple DefensePro VAs, taking care of connection stickiness. Elastic scalability and resiliency are maintained for the group of DefensePro VAs to ensure that DDoS inspection is always available in a cost-effective manner.
Ingress traffic from the Internet is routed through the AGWe to the DDoS Inspection VPC for inspection by DefensePro VA, and routed back to the application instances, and vice versa.
[You may also like: From Survival to Security and Availability]
The Gateway Load Balancer can integrate with AWS Transit Gateway to achieve highly scalable deployments. Customers may separate north-south and east-west inspection to enforce different security policies by implementing dedicated VPCs for each. While north-south inspection is most common, east-west attacks from within a cloud environment can be very stealthy and require a finely tuned security policy.
Combining Radware’s Cloud DDoS Services with DefensePro VA
The Gateway Load Balancer and DefensePro VA provide an elastic and resilient DDoS protection solution. However, DDoS attacks can scale to very high volumes. In such cases, mitigating the attack might be too expensive due to the auto-scaling of the DefensePro VAs. Worse still, if auto-scaling reaches its pre-configured limits, the whole application availability might be affected. For such cases, Radware offers Cloud DDoS services.
Cloud DDoS services can protect against very large-scale attacks by diverting the traffic (for example, DNS diversion) to Radware’s DDoS scrubbing centers before the traffic reaches AWS regions. Radware’s Cloud DDoS services utilize the same DefensePro technology to enrich traffic baselines and attack information between DefensePro VA in the AWS VPC and in the scrubbing center. This allows accurate and fast time-to-mitigation of attacks.

Download Radware's C-Suite Perspectives report to learn more.
Download Now