Information Availability is needed before Integrity & Confidentiality!!!
Before I get into this heresy talk, let me start off by saying “I’m a security guy!”
I am a lifelong information security veteran who sees himself as a ‘practitioner’ - - that is I am an active participant in practicing the fine art of information security. I view my role in life metaphorically as I envision a Medical Doctor's role - - trying to best deploy the highest efficacy of a ‘solution’ towards an ailment.
The Practice of Information Security
Where Doctors have ‘diseases’ and ‘ailments,’ we security folk have ‘risks’ and ‘vulnerabilities’ which need addressing. Where Doctors prescribe drugs and healthy living regimens (diet, exercise, lifestyle changes), we prescribe architectures, configurations, policies and tools. Where Doctors use routine checkups and diagnostic tests to sample progress, we use audits, assessments, alerts and SIEMs to gauge progress. Where Doctors have emergency rooms for acute triage, we leverage incident response teams and real time attack mitigation techniques to address the acute issues of the day.
The Idea of Information Security
In as such, I am beholden to no idea, schema, architecture, model, product or company in the practice of information security.
In fact, I see the practice of information as a constant struggle between the classic deployment of models & controls and the eventual decay in those models to the point whereby self-renewal is required in order to gain an advantage in the classic world of “chess” we play with nefarious actors.
Confidentiality – Integrity - Availability
With that, today I would like to speak to all those who also see themselves as true security professionals and who partake in the daily fight to bring strong security to their employers. To those folks I would like to present a renewal to the mental model we’ve all been living with for at least two decades - - that is the CIA triad. This ‘triad” is one in which we’ve all taken as a matter of great faith and one in which I subscribe to emotionally.
If you are not familiar with the CIA triad – a quick review is in order as this triad is that basis for all CISSPs, CISMs and security + professionals. The idea is that the world of information security has three main principles and they are all created equal. These principles are, as stated earlier, the classic triad of information security: Confidentiality, Integrity and Availability and encompass the reason behind everything we do to control and adjust risk profiles within organizations. The triad is often shown in this sort of a format (diagram below), however you may also see it commonly displayed as a Venn-diagram variant.
So now, let’s talk about this model’s main problem - - first is that it treats the three areas of security as equal when in fact there are dependencies. For example, you can have availability without having confidentiality or integrity; however you cannot have confidentiality without having access to (e.g. availability to) the information you seek. Also there is clearly a dependency in which confidentiality has on integrity. That is, you cannot have confidentiality without having integrity first.
Now, I can blow out this model ad nauseam, however the point is that there is CLEARLY a dependency here which has not been illustrated in ANY of the “Common Body of Knowledge” of a security professional and one in which I believe looks more like the following diagram:
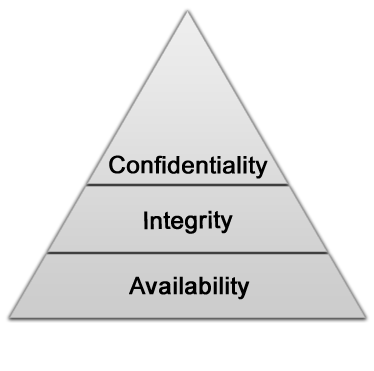
If this is indeed a true theorem, then this dependency dramatically changes the way in which we deploy controls and information security models as priorities are assigned differently to requirements.
In other words, if you believe as I do, in order to have secure, confidential data, you must first have reliable and available information, then that means that confidentiality is a higher-order attainment. Yes, much like Maslow’s hierarchy of Needs helps illustrate Man’s various attainment of needs, this idea helps place into context that secure data cannot be reached until more basic forms of security are achieved.
The infamous anonymous group and their influx of DDOS attacks illustrate that our efforts must focus on the basic and primal needs of our organization’s availability. As security professional’s we must protect our networks from these attacks and avoid the loss of productivity, revenue and reputation.