For a large number of online gamers that planned to spend their holiday break playing online games such as League of Legends, Minecraft, DayZ, Eve Online, and even ClubPenguin, they were met with an unpleasant surprise. A hacker group with the name “DERP” was attacking many of the Massively Multiplayer Online Games (MMOG) sites over the last couple of days.
While DERP suggests that the group is using Low Orbit Ion Cannon (LOIC) which is a well-known DDoS attack tool used in various attacks (e.g.: Operation PayBack), and while it is a fair to assume that DERP uses a number bots for the attacks, the exact attack tools being used are not clear. DERP suggests that it is attacking the login servers, which make sense, as these servers are more susceptible to attacks than the application servers in such sites.

Providers of online games have faced a large number of DDoS attacks the last couple of months. As these sites are usually an opulent source of users’ private information (passwords, email addresses and also payment information), cyber criminals trying to hack such sites to get control of this sensitive private information. While some of these data harvesting attacks are done silently, some use Distributed Denial of Service (DDoS) attacks as a way to distract IT administrators of these sites from the real target of the attack. This type of distraction technique is similar to the 20th century military combat doctrine that used massive artillery strikes in one area to cover surgical commando operations in another. Criminal attackers targeting financial services are commonly using DDoS attacks for exactly the same reasons.
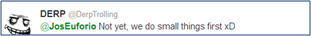
It is unclear if the DERP DDoS attacks are just “artillery cover” for other hidden cybercrimes. Looking at its Twitter account name DERP suggests that it is just trolling. But if you read the Tweets it posts, there is something completely opposite of that. Although it is against the interest of uncaught criminals to discuss their activities in public (and DDoS attack is a criminal act), we saw different hacking groups going public before they attacked their targets. The hacking group Anonymous is famous in announcing their attacks post-attack or while they are happening, as found in many of their posted YouTube videos. The Twitter conversation that took place on the last couple of days was even stranger than that. DERP, was having live conversations with some of its more than 40,000 Twitter followers, and even getting requests to take servers down.


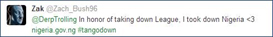
Interestingly enough, as the number of followers grew at a rate of close to 1,000 new users per hour, there were some that tried to imitate DERP activities by taking down non-gaming websites:
As the massive attack passed its third day, I’m hoping that DERP will stop disrupting the online gaming industry. I’m sure there are many kids out there (my daughter included) who really miss their Club Penguin character.
Like this article? Receive similar articles by subscribing to our blog today!