Over the last month there have been numerous TeamViewer users reporting unauthorized access into their computers that resulted in financial loss and stolen credentials. TeamViewer is a software package used by both personal and enterprise users for remote control, desktop sharing, file transfers and more. TeamViewer also uses end-to-end encryption to prevent a number of different potential attack vectors such as Man in The Middle (MITM) and brute-force attacks.
These reports of drained PayPal accounts and stolen credentials have mainly been found on Reddit, but have also been seen on a number of other sites dating back to May 1, 2016. Most of the attention drawn to TeamViewer came on June 1st at around 1pm EST when TeamViewer sustained a 3-hour long denial of service attack aimed at their DNS infrastructure. It should also be noted that earlier in the day an unknown user had posted TeamViewer’s DNS information on pastebin.
Shortly after the outage, TeamViewer issued a statement about the attack and unauthorized connections:
“TeamViewer experienced a service outage on Wednesday, June 1, 2016. The outage was caused by a denial-of-service attack (DoS) aimed at the TeamViewer DNS-Server infrastructure. TeamViewer immediately responded to fix the issue to bring all services back up.”
At the time of the outage, users began going to Reddit to see if there were any updates or information about the cause. Most users ended up here, where several TeamViewer users shared their stories of compromise and event logs proving their devices were compromised.
User Comments
June 1st 2016 – Reddit - I then checked my logs at C:Program Files (x86)TeamViewerTeamViewer11_Logfile.log and sure enough, it shows someone connected to my computer at 2:58 am, right before the paypal purchases/transfers
May 24th 2016 – Tim Oliver's Blog - Someone had actually logged into my TeamViewer from Russia, and FOR THE BRIEFEST OF MOMENTS had direct control of my NUC!
May 17th 2016 – Reddit - I opened the TeamViewer .log file and saw two different[1][2] teamviewer ID with two different IP (one from China and the other one from Japan, the one from China belongs to a small company, a China VPS provider (http://runidc.com/) [3], the one from japan seems to be a free Wi-fi Hotspot)
May 1st 2016 – TeamViewer Forums - on May 1st 2016 (at 13:04 GMT+3, Bucharest, Romania) someone hack intro my PC from TeamViewer and stole all my passwords from browsers (IE, Firefox, Chrome, Opera) with a little software fromhttp://www.nirsoft.net/utils/web_browser_password.html called WebBrowserPassView.
[You might also like: School Networks Getting Hacked – Is It the Students’ Fault?]
Ongoing Campaign
After further research, it was discovered that this has been a persistent problem for the last month. TeamViewer even issued a press release on May 23rd stating that:
TeamViewer is appalled by any criminal activity; however, the source of the problem, according to our research, is careless use, not a potential security breach on TeamViewer’s side. Therefore, TeamViewer underscores the following aspects:
1. Neither was TeamViewer hacked nor is there a security hole
2. TeamViewer is safe to use and has proper security measures in place
3. Our evidence points to careless use as the cause of the reported issue
4. A few easy steps will help prevent potential abuse
Many people have been quick to fault TeamViewer, but are they really at fault? If TeamViewer had been breached, we would be seeing a different set of data points and accounts breached on a much larger scale. This clearly indicated that the issue is client-side, and there are a number of theories to support this idea. The first surrounds the recent database leaks on The Real Deal, a darknet market. Vendor, Peace of Mind has been selling a number of leaked databases with a total of over 100 million credentials. Sites like LinkedIn, Tumblr and Myspace have all been implicated. One of the popular ideas is that the attackers are using leaked credentials to gain access to other digital platforms due to password and username reuse. While this is possible, we have seen other evidence to suggest this is all a result of a malware campaign targeting the client-side application of TeamViewer.
BackDoor.TeamViewer.49
Recently, it was reported by Dr. Web that BackDoor.TeamViewer.49 was:
“A Trojan for Microsoft Windows that is spread by Trojan.MulDrop6.39120. The Trojan's main payload is incorporated into the avicap32.dll library. Trojan.MulDrop6.39120 runs TeamViewer that automatically loads the library to the computer’s memory. All lines, imports, and functions of TeamViewer’s process are actively implemented by this malicious library. The most critical parts of the Trojan’s code are encrypted with base64 and RC4.”
TeamViewer also issued a statement about BackDoor.TeamViewer.49, saying:
“The real issue seems to be the installation of a malware program via the installation over a manipulated Adobe Flash player update. With the installation of the malware program, TeamViewer will be installed on the remote side. Resuming, the current situation unfolds as follows: The aforementioned malware is spread via another malware named Trojan.MulDrop6.39120 which is a forged update of Adobe Flash Player.”
“The executable file of Trojan.MulDrop6.39120 installs the player on Windows. Meanwhile, it covertly saves TeamViewer, BackDoor.TeamViewer.49, and a necessary configuration file on the disc. During the installation, a legitimate installer window of Flash Player is displayed. When users install this malicious Flash Player update, they get a legitimate Flash version, but also the Trojan.MulDrop6 Trojan, which secretly installs TeamViewer on the victim's computer.”
BackDoor.TeamViewer.49 runs parallel with the current attacks, but some things just don’t match up. What has most likely happened is we are currently seeing the introduction of a new exploit kit that is leveraging a vulnerability to gain access to devices with TeamViewer installed on them. Once the attacker gains access to the device, they run a program that retrieves and recovers passwords that are stored in browsers with tools like ChromePass and WebBroswerPassView. Once the attacker has the list of stored passwords, they quickly exfiltrate the file and begin accessing PayPal and Ebay accounts in an attempt to purchase gift cards and other turn-and-burn items that they can quickly resell.
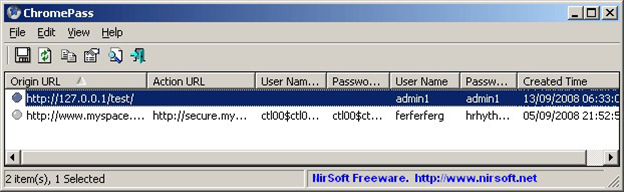
Figure: ChromePass
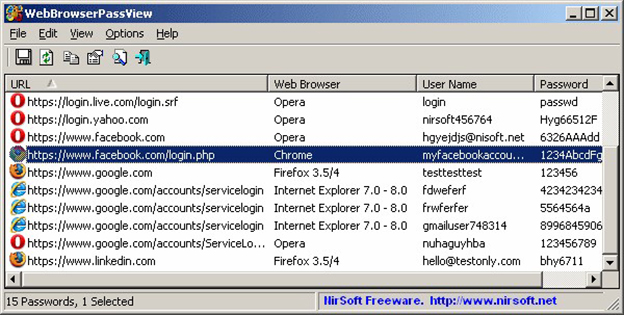
Figure: WebBrowserPassView
Recommendations
One common thread seen with these attacks is that the attackers are motivated by profit at your expense. They are using very basic attack methods to target low-hanging fruit. TeamViewer has provided these recommendations inside of their press release:
TeamViewer strongly recommends:
• Users should avoid all affiliate or adware bundles: While users may think they are just downloading a harmless program, the software could in fact install something else.
• Users ought to download TeamViewer only through the official TeamViewer channels such as the TeamViewer website https://www.teamviewer.com
• Users should protect any user account - whether it is with TeamViewer or any another supplier – by using unique and secure passwords that are frequently changed.
• Users should ensure they have reliable anti-malware and security solutions in place at all times.
It’s also suggested that every user, no matter what the service you use, create a different password for each account. In addition to this you should also use a strong, complex password and change them often. Never store your passwords in your browser. Users should also use 2-factor authentication when possible. To check to see if your service offers two-factor authentication visit https://twofactorauth.org/
Download Radware's DDoS Handbook to get expert advice, actionable tools and tips to help detect and stop DDoS attacks.
Download Now