A few weeks ago I had the honor of presenting at the Chicago Network Operators Group (CHI-NOG) conference about the current DDoS Threat Landscape and some of the tools people are using to attack networks today. It was the sixth iteration of the event, which continues to grow in size and content, and the second time that I have been fortunate to present about DDoS. Radware was pleased to be a sponsor of the event this year.
 NOGs are Internet Network Operator Groups where networking industry professionals can share ideas, problems, questions, etc., and they have taken the form of regional/continental affiliations. For example, North America has NANOG (North American Network Operator Group) as the main NOG in the region, but we also have smaller regional groups like CHI-NOG in Chicago and the newly formed NYNOG in New York City. The smaller regional groups provide the opportunity to network with more local contacts who may not have the time or budget to travel to the large events, as well as focus on regional interaction and issues.
NOGs are Internet Network Operator Groups where networking industry professionals can share ideas, problems, questions, etc., and they have taken the form of regional/continental affiliations. For example, North America has NANOG (North American Network Operator Group) as the main NOG in the region, but we also have smaller regional groups like CHI-NOG in Chicago and the newly formed NYNOG in New York City. The smaller regional groups provide the opportunity to network with more local contacts who may not have the time or budget to travel to the large events, as well as focus on regional interaction and issues.
[You might also like: 5 Cyber Attack Developments Worth Your Attention]
CHI-NOG has quickly built a reputation as a premier event that attracts some of the best networking minds in the industry as both attendees and speakers. The organizers of CHI-NOG are industry professionals who all work full time jobs and prepare the event in their spare time. Presentations at the event were technical in nature and were delivered by engineers from LinkedIn, Cisco, Nexum, University of Wisconsin-Madison, Equinix, Juniper, Radware, United IX, ESnet, Kentik, and Cachefly. The attendee list continues to grow, attracting around 160 people this year.

Attacking the Network
This year my presentation was about how people attack networks and which tools they’re using to do so. Some of the content was from Radware’s DDoS Handbook, as well as an interesting review of the Anonymous 2016 Toolkit, booter and stresser services, as well as attack operating systems. I received a lot of feedback about how surprised people were by the flexibility and ease of the tools people attack networks with. Most interesting to people seemed to be the scale of attacks that can be purchased for very little amounts of money, of which examples are covered in the presentation below.
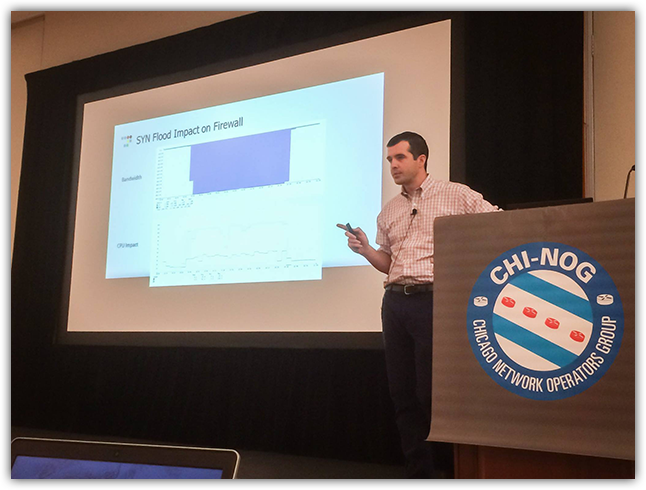
A video of my presentation can be found here:
And the actual presentation can be found here:
If you get the chance to attend, I highly recommend this conference. It’s full of great information and great people, and the organizers are some of the nicest people you’ll meet in the industry. I hope to see you there next year!
Download Radware's DDoS Handbook to get expert advice, actionable tools and tips to help detect and stop DDoS attacks.
Download Now