Automated Attacks Are Here to Stay
It seems the future is upon us. Some of you may have heard about the attacks on Brian Krebs’ security researcher and journalist, as well as the attacks on OVH French hosting company. The attacks are accounting for the world’s largest DDoS attacks ever on record, 620Gbps and 1+Tbps respectively. If you’ve read up on these attacks, you’ll also be familiar with the fact that automated bot armies are being leveraged by booter or stresser services. These services are offered by “entrepreneurs” for a nominal fee to their paying clientele. Booter services are not new to the realm of DDoS. What’s changed over the years is the scale and scope these automation engines are achieving. The services command and control networks have grown in number of pwn’d bots and increased capabilities of advanced and effective attack tactics. The exponential population growth of insecure internet-connected devices has enabled this. The Internet of Things (IoT) aka IP-enabled cameras, printers, TVs, refrigerators, etc. have certainly contributed in part because these devices were not developed with security in mind.
Radware’s security research teams have been tracking the IoT growth and correlating attack data, and as expected, we’ve witnessed a significant uptick in attack automation, complexity, and evasion techniques. A few of the key indicators we track are the size, duration and multiple attack tactics leveraged. I suggest a read through our last few ERT reports to gather details around the growing trends.
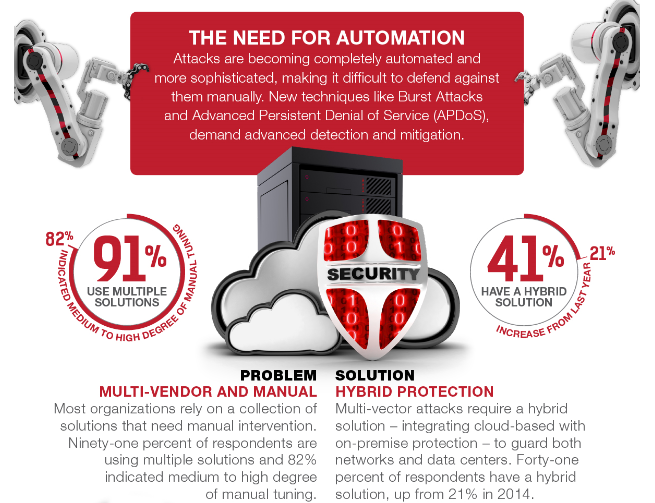
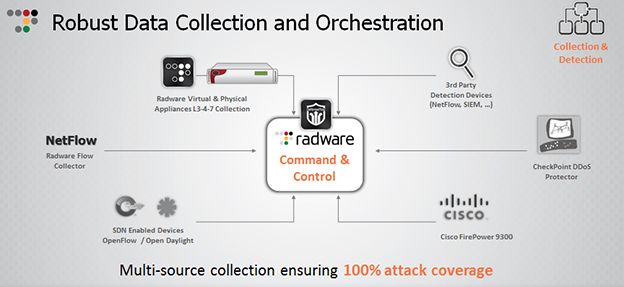
Automated attacks are here and they are proving to have tremendously fierce impact. In order to combat the attacks of tomorrow, you need to fight back with automation, today! We need zero minute mitigations and orchestration of the entire attack lifecycle. An agile command and control approach, like Radware’s DefenseFlow, enables multiple source detection/collection inputs and ability to leverage Radware Defense Messaging and 3rd party API integration. Recent public examples include integration with next generation flow tools Kentik and Deepfield.
[You might also like: Are You Ready for a New Age of Attacks?]
A DDoS attack life cycle can be broken-down into seven simple steps that are all visible to the customer in real-time:
- Detection of an attack – The first step in mitigating a DDoS attack is to detect it. When a protected network is under attack, Radware detects the attack and determines if a traffic diversion to the scrubbing center is required.
- Diversion Initiation – The decision to divert can be made automatically by predefined pipe saturation thresholds and security alerts, which are synced from the customer’s on-premise equipment (CPE) via DefenseMessaging, or manually either by the click of a button in the portal, programmatically via API/SDK, or by contacting Radware by phone/email.
- Traffic Diversion – Once a decision to divert the traffic has been made, the traffic is diverted from the local data center to the scrubbing center
- Mitigation of attack traffic – Dirty traffic enters the scrubbing center where it encounters full multi-layered protection spanning DDoS attacks on the network and application layers, volumetric and non-volumetric attacks, as well as coverage of SSL-based DDoS attacks.
- Return of clean traffic to the protected network – While the attack traffic is being cleansed, only the clean legitimate traffic is routed back to the protected network.
- Cool-down – When the attack has ended, traffic remains diverted for a period of time. This provides quick protection in case a secondary attack is launched.
- Reversion – After the cool down period has ended, and no new attack has been launched, traffic returns to flow in the original peacetime routes; directly to the customer premises.
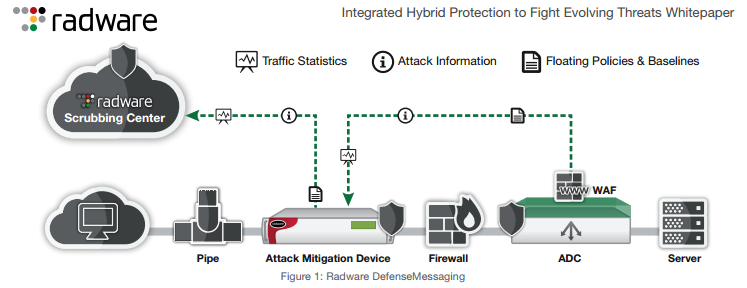
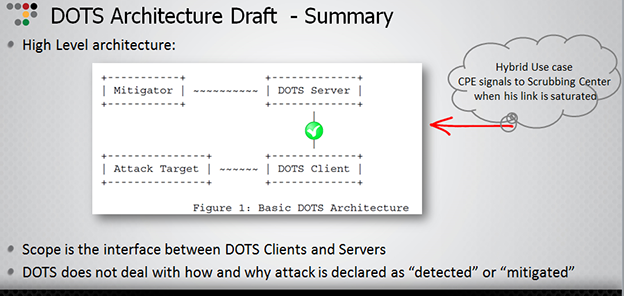
We are working diligently with others in the internet community toward the better good. We joined the DOTS (DDoS Open Threat Signaling) working group along with other vendors and operators to assist in developing a standards-based method of communicating between the DDOS mitigation appliances onsite and the Service Provider. According to the DOTS charter, “The aim of DDoS Open Threat Signaling (DOTS) is to develop a standards-based approach for the real time signaling of DDoS related telemetry and threat handling requests and data between elements concerned with DDoS attack detection, classification, traceback, and mitigation.” I won’t attempt to go through all the details here but rather point you directly to the source. On a very basic view, DOTS defines two main entities: DOTS Client and Server where “client” asks “server” for mitigation services in cases of DoS attack. DOTS’ signaling concept is similar to Radware Defense Messaging.
In closing, It’s a rough road ahead in the face of the impending bot attacks. What will you do to protect your business from the attacks of tomorrow? Consider the impact of automation and how your teams will withstand the near constant beating. Maybe you’re in a position to assist? Consider joining the DOTS working group take your part to secure those IoT devices or influence the adoption of BCP 38.