Originating from ARPANET back in the 70’s, the Darknet is essentially an overlay network, which applies strong privacy and encryption practices. I am often asked what’s the difference between Surface vs. Deep vs. Dark Web, so let me put it as simply as I can – and then let’s examine their relationship and contribution to cyber-attack campaigns that take place more frequently.

Understanding Surface vs. Deep vs. Dark Web
The Surface Web (or Clearnet) contains websites and services that we all use via standard web browsers (Chrome, Firefox, Edge) and can be found using Search Engines (Google, Bing). This means that such websites are indexed on an ongoing basis, where they can recognize their visiting users by their IP addresses. Different sources claim that the volume of data on the Surface Web is only 4%-10% (depending on the source) of the overall internet data.
The Deep Web contains data which is not for public consumption – hence it can be considered a “gray zone”. As such, it may contain reports (scientific, government, subscription-only, etc.), records (medical, financial, etc.), databases (academic, business, etc.), Torrent sites/directories and more. These can be accessed by closed forums, via invitation only or by deeply digging into specific directories/Wikis.
The Dark Web (or Darknet – in contrast to Clearnet) contains various types of illegal data and services that can be accessed only via specific tools (primarily ToR - The Onion Router) as it employs non-standard protocols, ports and cryptography, where the objective is to keep a user’s total anonymity. As we often hear on the media, the Darknet is a fertile ground for illegal trades and content (narcotics, firearms, stolen IDs, child pornography, etc.), although known marketplaces frequently go up and down or are permanently closed (Alphabay, TheRealDeal, Valhalla and others).
[You might also like: The Growth of DDoS-as-a-Service: Stresser Services]
DDoS Attack Campaigns Evolution
If we take a look at the cyber-attack landscape, we witness much more organized and focused Distributed Denial-of-Service (DDoS) attack campaigns that are on a completely different level. The two key factors to observe are:
Factor #1: Attack footprint is hard to predict – The development of recent DDoS attacks over time does not have a clear, predictable footprint. Attacks are longer, while the intensity and changes in volume become more dynamic and do not always present repeating patterns. Attacks are coming from different (often spoofed) sources, originating from different C&Cs, and using multiple vectors - to the effect that they start, disappear, and return in greater intensity. See the attack histogram in Figure 1 below as a nice example:
[caption id="attachment_7684" align="aligncenter" width="624"]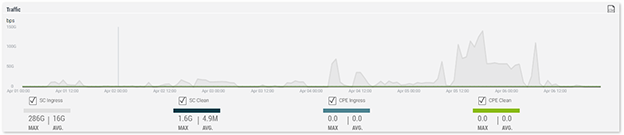 Source: Radware ERT / Cloud Security Services[/caption]
Source: Radware ERT / Cloud Security Services[/caption]
Factor #2: Attacks are more targeted – While many attack tools and exploit packs are available out there, the attack campaigns themselves are targeting specific vertical markets, specific customers, and even specific personas (e.g. corporate executives). For example, take a look at Dragonfly, a cyber-attack group that targeted the energy sector in Europe and North America. The goal of their latest attack campaign, Dragonfly 2.0, was collecting intelligence and gaining access to the networks of the targeted organizations, eventually making the group capable of mounting sabotage operations when required. The attack featured malicious email campaigns during 2016-2017, leveraging an infected document to leak the victim’s credentials to a server outside of the organization, and finally these credentials were used as follow-up attacks on the targeted energy organizations.
Attack Campaigns and the Darknet
So the question is, does the Darknet play a role in helping the perpetrators? Absolutely. If you’re the CISO of a large enterprise, there are specific items that may matter highly to you. For instance, in case of a financial organization (bank, insurance company, etc.), security officers may be interested in eliminating leakage of sensitive data, such as credit card information, online banking records, etc. That said, attackers can easily get relevant training, ideas and even code excerpts (!) from Deep Web sites and Darknet forums such as Evilzone, Hackaday, Hell, Exodus, Exploit, RuTOR, etc. In particular, there are many sites that offer prosperous trade of DDoS attacks tools and services (“DDoS for Hire”). And lastly, the Darknet also allows secured communication channels and forums where attackers can plan, coordinate and execute their complex attack campaigns – that are not limited only to DDoS.
Scientia potentia est: Leveraging Darknet Intel
As coined by Sir Francis Bacon, “scientia potentia est" which means "knowledge is power", is probably relevant today more than ever. But surprisingly, about half of businesses today do not trace the Darknet for leaked information (see Figure 2 below).
[caption id="attachment_7685" align="aligncenter" width="1352"] Source: Radware’s web application security report[/caption]
Source: Radware’s web application security report[/caption]
Apparently, extracting actionable intelligence from the Darknet isn’t always straightforward. Why? Keeping an eye on Darknet data requires resources, expertise and tools. Let’s take a closer look at the key reasons:
First, businesses must be able to get visibility into the raw data that may matter to them. It is way more challenging than accessing the Clearnet where websites and web content are freely accessible and searchable. Yes, in the Darknet there are search engines that can show results for Darknet sites, but they are limited by nature. So getting to the right data may involve deploying a sensor network, honeypots, or decoys as well as using faked social accounts. For example, to get raw data from the Darknet, one often needs to be part of specific forums. Not a simple task, as sometimes content is hidden and can be revealed only when you post a message - and you don’t want to do that in order to not to get exposed.
[You might also like: Bad Packets 2017 – A Year in Review]
Secondly, we need to be able to separate the wheat from the chaff. In other words, one needs to have the capacity (in the form of security analysts or automated tools) to do that on a large scale. Without that, organizations may end up spending precious time and energy trying to analyze unstructured data with no clear context, what will end up in total ineffectiveness.
Third, we need to correlate – get data from both the Clearnet and the Darknet and find the missing links between them. So essentially, examining pieces of information from sources like Facebook, Twitter, etc. may be equally important – for example, many Anonymous hackers have moved to Facebook. Other examples would be Pastebin, where users can upload/store text online (e.g. various user credentials, etc.), Ghostbin (which is used by hacktivists) and others. Ultimately, it’s crucial to take the processed intelligence, and feed it to existing attack prevention tools – DDoS mitigation, WAF, or anti-malware – whether on-prem on in the cloud.
Where is it going to?
Unfortunately, it’s not going to be any easier… Attackers will depend less on the Darknet for getting exploit packs and DDoS tools, and even less for communicating and coordinating their attack plans. As for them, communicating or making plans in the cyber world through secured channels won’t necessarily require the Darknet. The widespread use of mobile apps like Secret, Signal, Telegram, etc. allow for the confidential exchange of ideas and data. These kind of applications don’t save messages metadata, hence messages cannot be traced. Moreover, attackers can write their own Android Package Kit (APK) files - which is the file format used by the Android OS for distribution and installation of mobile apps - and then send a link to it to the group members, so that it doesn’t need to be listed in mobile app stores (e.g. Google Play or the like), at all.
The final word? In the end, it seems that the cat-and-mouse game of constant pursuit, near captures, and repeated escapes between attackers and security solutions is here to stay - and get to the next levels.
Read "Top 9 DDoS Threats Your Organization Must Be Prepared For" to learn more.
Download Now