With more countries taking measures to contain the
coronavirus and more organizations asking employees to work remotely from home
whenever possible, the digitalization of the workplace is accelerating
prematurely.
Organizations, depending on size and use case, leverage
proven technologies such as enterprise VPN and Remote Desk
Protocol (RDP) to provide secure remote access to sensitive resources and
internal applications.
Less than a month ago the industry recovered from a period
of turmoil during which multiple vulnerabilities in enterprise VPN products
from Pulse Secure, Fortinet, Palo Alto, and Citrix were exploited in the wild
during attack campaigns by malicious actors and nation states alike.
RDP requires special care and specific considerations when used for remote access. RDP has been for the most part of 2019, and continues to be, by a fair margin, the most important attack vector for ransomware.
The second most important cause of ransomware infections
is phishing. In a period of fear and doubt, scams are thriving and phishing
attacks leveraging the coronavirus have not been lacking.
[You may also like: The Quest To Automate The Business Of Fake News]
Disinformation and fake news surrounding the coronavirus
does not only drive fear and doubt among the people but becomes a weapon of
influence and political bias. The digitalization of the press and the social
media penetration rate means that information, good and bad, true and fake, is
spreading faster and further than ever. A platform on steroids for weaponizing
disinformation.
While, according to most current reports, only human bots have been architecting fake news, automated machine bots have found their lucrative leverage of the coronavirus through the use of spam bots performing search engine optimization for dubious pharmaceutical products and online drug stores.
Remote Work
On Monday, March 2, 2020, 9to5Google
reported that a Googler in Dublin came down with flu-like symptoms. A week
earlier, an employee in Zurich tested positive for the coronavirus. As a
precaution, Google instructed its Dublin staff to work from home on Tuesday,
March 3. The Dublin office serves as Google's European headquarters and is home
to 8,000 employees. For Google, that Tuesday served as a test and case study
for other sites globally: can it perform at full capacity for an extended
period?
That same Monday, Twitter asked
its entire global workforce of 5,000 people to work from home in order to slow
the spread of coronavirus. Working from home is mandatory for Twitter employees
based in Hong Kong, Japan, and South Korea due in part to government
restrictions. Twitter also announced they are working to ensure internal
meetings, all hands, and other important tasks are optimized for remote participation.
One day earlier, on Sunday, March 1, Twitter announced
the suspension of all non-critical company travel and events. Chief Executive
Jack Dorsey was scheduled to speak at an upcoming SXSW conference in Austin,
Texas-a conference that later would be canceled by city officials over fears
about the rapid spread of coronavirus-but would apparently not make an
appearance. The Twitter policy took effect immediately and continues until the
World Health Organization (WHO) or Centers of Disease Control (CDC) deem it
appropriate to step back from pandemic precautionary measures.
After confirming one of its Seattle-based employees tested
positive for COVID-19, Amazon asked
all of its 50,000 Seattle-area employees who can do their jobs from home to do
so until the end of March. Microsoft issued a similar guidance on Wednesday,
March 4, asking
employees to work from home for at least the next three weeks.
On Friday, March 6, Apple asked
its employees at its Silicon Valley headquarters to work from home if possible
as a precaution. Officials of Santa Clara County, where Apple's 12,000 person
campus is located, had earlier asked large companies to consider measures to
limit close contact. Apple also asked employees in the Seattle area to consider
working from home.
On February 28, 2020, after close consultation with
their partner in the game development industry and the community around the
world, Google made the difficult decision to postpone the
Game Developers Conference that was slated for March 16-20. The conference is
now supposed to take place over the summer while a separate Google 'digital
experience' will allow the company to share important announcements in the short-term.
Google is also moving its North American version of Cloud
Next to an all-digital experience. The event dates remain unchanged but it will
now be a "free, global, digital-first, multi-day event" and will
include online streaming of keynotes, breakout sessions, interactive learning
sessions, and a live Q&A feature with Google employees.
[You may also like: There’s Another Global Pandemic We’re Not Talking About]
Microsoft, Dell Technologies, Red Hat, and Nvidia are
among other
vendors that have to alter upcoming mega-events due to health concerns tied
to the growing spread of the coronavirus. Details for the events are still
being worked out but are expected to follow Google's model. The virtualized event
line-up for the next couple of months includes:
- Microsoft’s MVP Global Summit initially set to
begin March 16 in Redmond, Washington;
- Nvidia’s GTC 2020 event originally scheduled for
March 22 in San Jose, California;
- Adobe Summit that was originally scheduled for
end of March in Las Vegas;
- Red Hat Summit initially scheduled for April 27
in San Francisco; and
- Dell Technologies World originally scheduled for
May 4 in Las Vegas.
On February 26, Zoom announced
that in the last 30 days alone, the average downloads of its video
communications software were up 90% compared to the prior 30-day period. Their
platform saw a 17% increase in user sessions per day and a 3% increase in
average session length. The company has added more new active users so far in
2020 than it did throughout all of 2019, with 3.5 times more monthly active
users in 2020. And that announcement came before the coronavirus outbreak
became as pronounced in the U.S. as it was in other countries like China and
Italy, and before high tech companies started announcing renewed policies for
remote work and online collaboration.
Cisco Webex, the conference service that provides a
default-free plan supporting up to 50 participants per meeting, with meeting
times limited to 40 minutes and online recording storage up to 1GB, is now
offering, in this time of need, free 90-day licenses without time restrictions
and support for up to 100 participants for businesses who are not Webex customers.
Cisco also announced
the expansion of their worldwide meeting capacity, scaling up further in the
United States and Europe, working with non-governmental organizations to enable
schools, while partnering closely with their customers who are rapidly scaling
up their work from home efforts.
[You may also like: Security is on the Verge of a Major Transformation]
The ZDNet
special feature on free video conferencing also reports that Google isn't
offering free conferencing services to new users but is rolling out free access
to its advanced Hangouts Meet video-conferencing capabilities to all its G
Suite customers. This includes larger meetings for up to 250 participants per
call, live streaming for up to 100,000 viewers within a domain, and the ability
to record meetings and save them to Google Drive. These features will be
available at no additional cost until July 1, 2020.
LogMeIn, another experienced video conferencing company
that usually comes with a 14-day free trial, now
provides critical front-line service providers, including eligible
healthcare providers, educational institutions, municipalities, and non-profit
organizations, as well as current LogMeIn customers with free,
organization-wide use of many LogMeIn products for three months through the
availability of its Emergency Remote Work Kits.
Microsoft is offering a new six-month
Office 365 E1 trial offer that includes full meetings, collaboration, and
workflow capabilities and will enable all global customers to start using Teams
immediately.
Pulse Secure offers temporary licenses for its Pulse
Connect Secure product under its Pulse Cares program. The
limited period offer enables secure remote and mobile access from any device to
enterprise services and applications in the data center and cloud until May 31,
2020.
Besides the industry, education is also evaluating its
options to move to remote or online learning. As COVID-19 spreads, health
officials are calling for fewer public gatherings, which forces many
institutions and organizations to explore online activities. For school
officials across the world, there is little time to prepare. The United Nations
recently warned
that school closures in thirteen countries are disrupting the education of
290.5 million students globally, a number without precedent. The UNESCO
Director-General said that, "the global scale and speed of the current
educational disruption is unparalleled and, if prolonged, could threaten the
right to education." UNESCO is providing immediate support to countries,
including solutions for inclusive distance learning.
[You may also like: Agile Security Is Now A Reality]
Only two days after the UNESCO statement, Stanford announced
that its final two weeks of the winter quarter, beginning Monday, March 9, will
not meet in person in order to deal with the outbreak; where feasible, classes will move online. Winter quarter final
exams that were scheduled will need to be provided in take-home format.
Stanford might well be one of the better-equipped universities to implement a
swift move to remote education and leverage its experience with Stanford Online.
Earlier that Friday, March 6, the University of Washington
told its 50,000 students that courses would move online on Monday. Seattle
University (7,000 students) and the Seattle campus of Boston's Northeastern
University have also moved to online courses. Other schools and universities,
currently spared from infections, are taking this same week as an opportunity
for testing online and virtual classes.
MOOCs or Massive Open
Online Courses are not new. As early as 2006, MIT, later joined by other
high profile universities, started experimenting with online courses. Harvard,
MIT, Microsoft, Stanford, and other top universities have been providing open,
self-paced educational content for almost a decade now. Before the coronavirus,
the MOOC market size was estimated at $4 billon in 2018 and demand expected
to grow at a CAGR of 33.6% during the period of 2019 to 2025.
[You may also like: How to Practice Safe Public Wi-Fi Usage]
The attack surface is changing and expanding as many
organizations move to online and digital experiences as a result of the
measures taken to inhibit the spread of COVID-19.
While transforming, organizations are exposing
themselves to more potential threats since they are forced to do so in a
limited and less convenient timeframe. These changes are expected to increase
the attack surface of organizations as they implement quick and often
'temporary that become permanent' solutions to maintain a certain level of
productivity. Most organizations will not have had time to adapt their risk
models accordingly. Assessing and understanding the impact of new services or
solutions will, in most cases, be subjacent to providing a service at any cost.
It is, rolling out new services hastily with emphasis on access and usability
in favor of security.
Below are, in my opinion, the three most immediate threats
organizations face during these times of extreme measures.
Think about the (your) organization, which given a
timeframe of only a few days, needs to provide a scalable remote work option
for employees who were never expected to be working remotely before a pandemic
forced them to. Did I mention the solution needs to be secure? For some, that
might be obvious, but the emphasis in times of high need will be on providing
the access without too many headaches for the user or an insurmountable flood
of support tickets. So, secure, yes, unless it risks delaying the rollout or
making the solution less usable.
One needs to decide on an easy-to-deploy and convenient
access technology that enables the broadest amount of employees to perform their
tasks remotely as much as possible. The obvious choices will be remote desktop
(RDP) and enterprise VPN access solutions, directly binding the remote user
with the organization's network and servers.
While RDP can be a very effective tool to let users quickly connect to a remote desktop and perform their daily tasks from home, threat actors have been known to leverage RDP as an attack vector for ransomware campaigns. It gained traction in 2018 and by Q1 of 2019, it was by far the most preferred infection vector for ransomware.
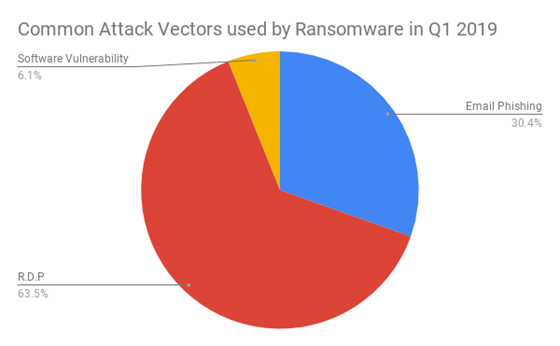 (Image source: Coveware)
(Image source: Coveware)
On cybercrime marketplaces, RDP credentials remain inexpensive as criminals can easily harvest them through brute-force attacks. The going price for RDP credentials was $20 a piece on darknet marketplaces as of September 2019.
It should be clear by now that strong passwords or some
form of multi-factor authentication (MFA) is an absolute requirement when
exposing remote desktop access for home workers. It is advisable to at least
have all employees reset their password as they connect remotely and force them
to choose a new password that complies with a strong password complexity
guidelines. Employees might have been reusing their passwords for one or more
online services-services that might have fallen victim to a breach, resulting
in stolen customer credentials traded on the underground marketplace. Bad
actors will happily leverage these breach batches for performing more efficient
credential stuffing attacks against organizations' exposed services.
The second most prevailing attack vector for ransomware is
Phishing, a vector which will not pass on an opportunity as big as the fear and
concern caused by a fast spreading virus. Phishing will be discussed in its own
paragraph below, but for now, between RDP and Phishing, 94% of ransomware
infection causes are covered!
[You may also like: Ransomware: To Pay or Not To Pay?]
BlueKeep, an
exploit which leveraged a vulnerability in RDP and affected most Microsoft
Windows versions, and which was responsibly disclosed and provided with a
timely fix, became the object of a mass-hacking
campaign in November 2019. Microsoft had warned
this might happen and urged users to patch their systems already back in May
2019. The attack campaign was not a big hit, but one of the consequences of the
attacks was the assessment of the attack surface by researchers, which
confirmed 750,000 systems had RDP exposed to the internet AND were vulnerable
to BlueKeep. Not an insignificant number of systems that were left unpatched
between May and September 2019...
Citrix, the
original inventors of RDP, have been the subject of many controversies in the
beginning of this year regarding their Application Delivery Controller and
Gateway products. The Citrix products provide application-aware traffic
management and secure remote access. A vulnerability published on December 17,
2019 left access gateways exposed to unauthenticated remote code execution
attacks and remote access to a company's protected network and resources.
According to researchers, at the time, over 80,000 organizations were exposed and vulnerable to remote attacks through CVE-2019-19781. Citrix released a set of measures but did not have a fix available until one month later. Between January 9 and 17, it was basically open season on Citrix Gateways as honeypots from multiple researchers (Bad Packets and Rapid7, amongst others) were registering in the wild attack campaigns. Bad Packets assessed the number of exposed endpoints vulnerable to CVE-2019-19781 to be at least 25,000. The US Department of Homeland Security's Cybersecurity and Infrastructure Security Agency published an alert relating to this vulnerability on January 31, 2020 urging people to secure their installations.
On January 10, 2020, the U.S. Department of Homeland
Security's Cybersecurity and Infrastructure Security Agency warned about continued
exploitation of a Pulse Secure VPN vulnerability CVE-2019-11510. A few months
earlier, in October 2019, the NSA and the UK's National Cyber Security Centre
(NCSC) warned of multiple state-sponsored groups exploiting enterprise VPN
flaws. Advanced Persistent Threat (APT) groups had been exploiting recently
disclosed VPN vulnerabilities in enterprise VPN products from Fortinet,
Palo Alto Networks,
and Pulse
Secure. Both NCSC and NSA intelligence agencies confirmed APT groups
targeted several sectors, including military, government, academic, business
and healthcare.
Whether your organization is using or planning on
deploying remote desktop access or enterprise VPN solutions, whatever you do,
make sure you are running the latest software before exposing the service to
the internet. Failing to do so will re-open the hunting season on remote access
solutions!
[You may also like: Nation State Attacks Are on the Rise. Here’s Why You Should Be Worried.]
No major global event goes without malicious actors
exploiting it for Phishing. Coronavirus is, in this respect, no different than
other events. Fear and a continuous need for up-to-date information provides a
great breeding ground for abuse. A lot of phishing campaigns are luring people with
the promise of important or breaking information on COVID-19, enticing them to
click malicious links or open infected attachments. In the UK alone,
coronavirus scams costed victims over
£800k Pound sterling (the equivalent of nearly $1M USD) in the course of
one month (February 2020).
By the end of January, as the global death toll of the coronavirus reached 213 and more than 9,000 cases were reported, malicious actors started leveraging public fear to spread the notorious Emotet malware. Emotet, first detected in 2014, is a banking trojan that primarily spreads through malspam (spam emails) and attempts to sneak into computers to steal sensitive and private information. Emotet versions have evolved over time into a pervasive delivery platform for other malware including banking trojans.
Limited to Japan, these first coronavirus phishing scams discovered by IBM X-Force and Kaspersky warn about infected patients being reported in the victim's local area. The messages, in Japanese, urge victims to open a Word document containing malicious code. The sample message below, one of three samples documented by IBM X-Force, translates as:
Jurisdiction tsusho / facility related disability welfare service provider We become indebted to. Patients were reported about the new type of coronavirus-related pneumonia, mainly in Takeshi, China. Patients have been reported in Tottori Prefecture in Japan, Therefore, please check the attached notice, Thank you for your infection prevention measures. In parallel, we are preparing to publish on the Wamnet Kyoto page.
**************** Kyoto Prefectural Yamashiro Minami Public Health Center welfare room (in charge: Umino) 18-1 Kizu Ueto, Kizugawa City, Kyoto Prefecture 619-0214, Japan Telephone: 0774-72-0979 FAX: 0774-72-8412 ****************
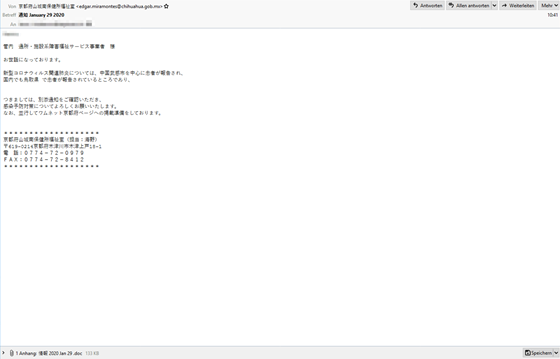 (Image source: IBM X-Force)
(Image source: IBM X-Force)
The different samples each target a different Japanese prefecture with Gifu, Osoka, and Tottori reported as actively exploited. The customized messages underlining the local nature of this phishing attack and also increase the success ratio as people feel more concerned with a message that is close to them.
On February 5th, Sophos reported a global phishing scam exploiting the coronavirus. The email carries the logo of the WHO and exhibits the usual spelling and grammatical mistakes that should act as indicators to victims that this message is not what it seems.
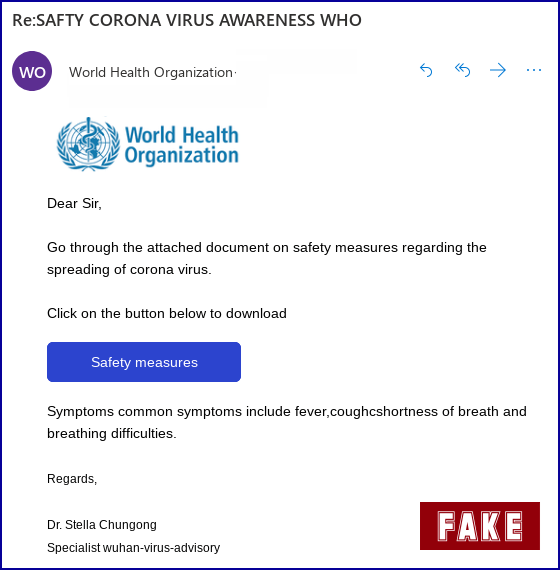 (Image source: Sophos)
(Image source: Sophos)
The link embedded in the message brings users to a compromised music site using insecure HTTP and shows a fake WHO page with a popup form asking for email verification and password. Upon submitting credentials, users are redirected to the real WHO site. A very basic attempt at stealing credentials, brimmed with red flags.
On February 25th, MailGuard reported a widespread email scam in Australia leveraging the coronavirus fear. The malicious emails are signed with "Dr Li Wei" and are titled "CORONA-VIRUS AFFECTED COMPANY STAFF." The sender of the emails is from a freshly registered domain, likely created for the sole purpose of the scam. The message urges victims to open the attached file which allegedly would contain pictures, countries, names, and companies of COVID-19 infected people as of February 22, 2020.
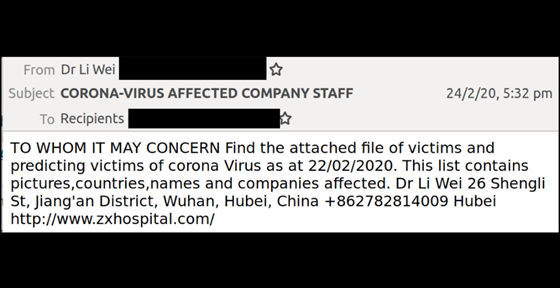 (Image source: MailGuard)
(Image source: MailGuard)
Once again, recipients of the above message should be able
to spot the fact that the email contains several grammatical mistakes, giving
away its malicious nature. You’d think by now, bad guys would have discovered
grammatic and spell checkers and take a little more care in crafting their
messages. Luckily for us, this is still mostly not the case.
On March 5th, Check Point announced that over 4,000 coronavirus-related domains had been registered since the beginning of 2020. Of the 4,000 new domains, 3% were found to be malicious and an additional 5% perceived as suspicious. The malicious or suspicious domain names are typically misspelled versions of a legitimate domain name or use popular keywords such as 'corona' and 'covid.' This technique is known as typosquatting. Compared to other domains registered during the same period, the coronavirus related domains are 50% more likely to be malicious and with a higher probability than recent seasonal themes such as Valentine's day.
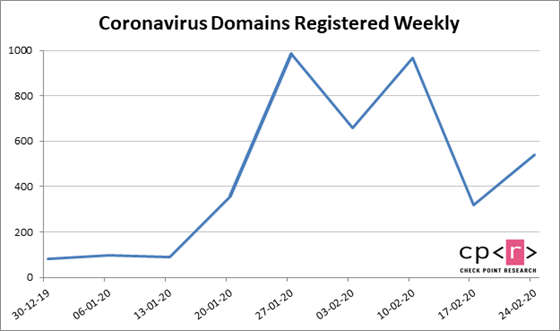 (Image source: Check Point)
(Image source: Check Point)
Needles to say, many of the previously mentioned domains
will eventually end up in phishing attempts.
While automated content generation by machines for
disinformation and fake news campaigns are yet to be reported, automated
(machine) bots are already claiming a fair amount of the malicious activity
surrounding the coronavirus in the form of spam bots. Imperva
recently discovered pharmaceutical spam campaigns performed by bots thriving on
the need for information about the virus.
The most popular and obvious technique is comment spamming. Bots inject popular and often searched keywords into comments on spam and drug-selling sites to increase the visibility and ranking of the site in search results. 'Coronavirus' is a highly trending search term in Google (see image below), and using it on a page will rank that page and the site favorably in search algorithms - a practice which is generally referred to as Search Engine Optimization (SEO).
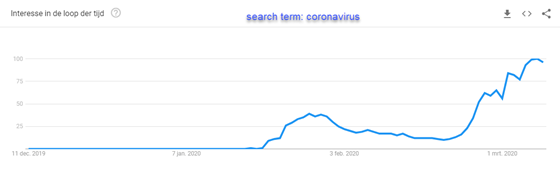 (Image source: Google)
(Image source: Google)
A second application of comment spamming is leveraging popular news and blog sites that attract a lot of readers and placing content with click-bait in the close vicinity of the usual keyword, such as 'coronavirus' in the example below. The click-bait URLs guide readers to dubious online stores in an attempt to grow their sales.
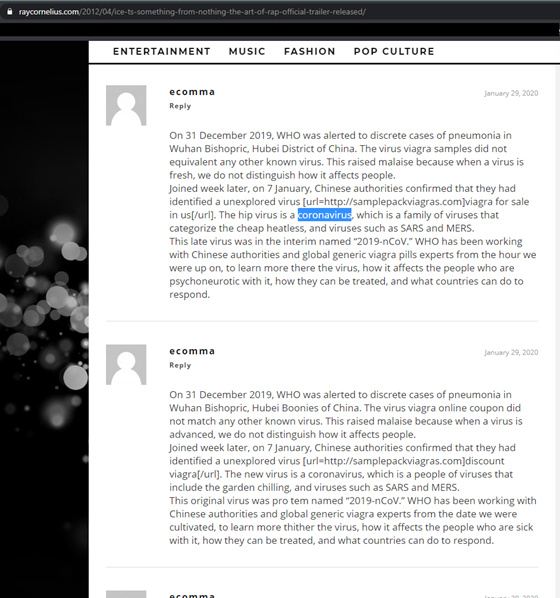 (Image source: raycornelius.com)
(Image source: raycornelius.com)
“We’re not just fighting an epidemic; we’re fighting an infodemic”, said WHO Director-General Tedros Adhanom Ghebreyesus at the Munich Security Conference on February 15, 2020. An 'infodemic' that undermines public trust in information at a time when transparency is essential. Misinformation and fake news proliferate at all levels and anything is fair game in the information wars.
For example, police departments are leveraging the fear of
coronavirus infection in an effort to make drug arrests. The Tavares
Police Department in Florida and the Merrill Police Department in Wisconsin
took to social media offering to test methamphetamine and other drugs for
contamination with coronavirus. "Bring it by our station and we will test
your batch within minutes!" Tavares Police Department said in a Facebook
post depicted below, "If you're not comfortable going into an office
setting, please request any officer and they'll test your Meth in the privacy
of your home. Please spread the word! We are here for you!"
Dean Koontz predicted the outbreak of a virus named 'Wuhan-400', developed in the RDNA labs outside of the city of Wuhan, in his novel 'The Eyes of Darkness' written in 1981. Source: https://twitter.com/NickHintonn/status/1228896027987660800?s=20
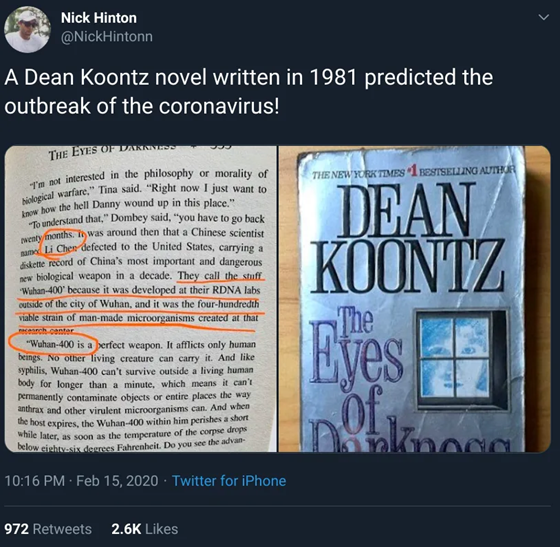
Snopes debunked the Dean Koontz myth here and discovered that when the book was published in 1981, the biological weapon was called 'Gorki-400' and Russian made, while by 2008 the virus had been renamed to 'Wuhan-400' and was Chinese sourced.
On Sunday, January 26, 2020, The Washington Times published
an article with the headline, 'Coronavirus
may have originated in lab linked to China's biowarfare program.'
On February 1, 2020, the most influential Chinese military
website xilu.com published an article
acknowledging the Wuhan coronavirus is man-made and accused the U.S. of
creating the bioweapon against China.
In the meantime, a GOP
senator keeps pushing the theory that the coronavirus is a leaked Chinese
biological weapon gone wrong, despite multiple scientists debunking this theory
that the virus would be a bioweapon gone wrong.
On March 4, 2020, the Chinese military website xilu.com (again) headlined an article that translates as '"Patient Zero" found? US liar is pierced' claiming that patient zero, discovered in Italy, was infected with the virus in Hawaii and had no history of contact with China. The article continues, and I paraphrase the quote translated from the website, that "because this patient does not have any Wuhan contact history, the Russian media believes that the US's previous accusations against China are a lie which has now been pierced!"
On February 22, 2020, the Guardian published an article
with the title 'Coronavirus:
US says Russia behind disinformation campaign.' which quotes:
Experts said the coronavirus disinformation campaign has parallels with previous conspiracy theories traced to Moscow, including a KGB disinformation campaign in the 1980s that convinced many around the world that US scientists created the HIV virus that causes Aids.
Several thousand online accounts – previously identified for airing Russian-backed messages on major events such as the war in Syria, the Yellow Vest protests in France and Chile’s mass demonstrations – are posting “near identical” messages about the coronavirus, according to a report prepared for the state department’s Global Engagement Center and seen by AFP.
The accounts are run by humans, not bots, and post at similar times in English, Spanish, Italian, German and French. They can be linked back to Russian proxies, or carry messages similar to Russian-backed outlets such as RT and Sputnik, the report said.
“In this case, we were able to see their full disinformation ecosystem in effect, including state TV, proxy websites and thousands of false social media personas all pushing the same themes,” said Lea Gabrielle, the head of the Global Engagement Center, which is tasked with tracking and exposing propaganda and disinformation.
And further: Some accounts have falsely claimed the US is waging “economic war on China” and that the virus is a biological weapon manufactured by the CIA.
In another part of the world, a Cyber
pioneer asks: "Is the coronavirus the result of a cyberattack?"
and continues "Those who know how to hack into financial bodies can also
hack pharmaceutical companies and create a virus."
On March 7th, whistleblowers and residents claimed that
China's message on the recovery from coronavirus is not what it seems. Caixin
investigation has found that local companies and officials are fraudulently
boosting electricity consumption and other metrics in order to meet the
'back-to-work' targets. As Beijing started checking Zhejiang businesses'
electricity consumption levels, district
officials ordered the companies to start leaving their lights and machinery
on all day to drive the number up. “They would rather waste a small amount of
money on power than irritate local officials,” Caixan writes. Businesses also
reportedly falsified staff attendance logs.
These a just a handful of examples demonstrating that
disinformation can as entertaining as it can be leveraged by conspiracy
theorists and in geopolitical warfare. The digitalization of press and the rate
of penetration of social media in our daily lives means information is
spreading much faster and way further than ever before, providing a fertile
platform for weaponizing disinformation.
Download Radware's “Hackers Almanac” to learn more.
Download Now