 (image source: NoName057(16))
(image source: NoName057(16)) The 2024 European Parliament election took place from June 3 to June 9. On June 6, NoName057(16) announced a cyberattack campaign targeting the internet infrastructure in Europe. The group claimed an alliance of at least nine groups that would be performing cyberattacks targeting EU countries throughout the most important days of the elections.
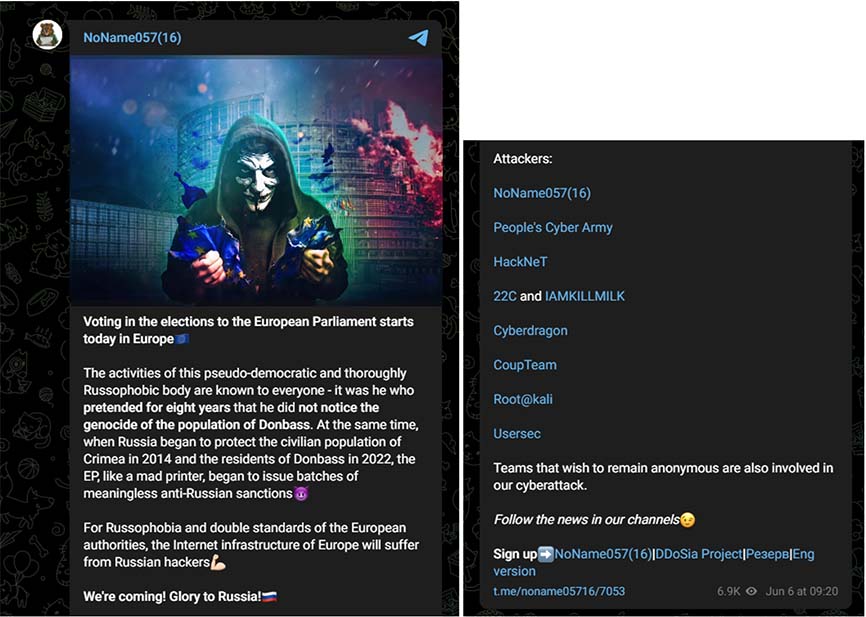 Figure 1: NoName057(16) announcing a cyberattack campaign targeting the EU Elections (source: Telegram)
Figure 1: NoName057(16) announcing a cyberattack campaign targeting the EU Elections (source: Telegram)Below are my findings based on attack claims posted by the nine groups mentioned in the announcement for the period between June 6 and June 10. NoName057(16) referred to more groups that preferred to remain anonymous. However, given hacktivists' primary objective is to draw attention to their cause, I doubt those unnamed contributors. Our records showed very little activity outside of five out of nine groups mentioned by NoName057(16).
Telegram Reach
Of the nine groups mentioned in the announcement, NoName057(16) has the most followers on Telegram. The Cyber Army of Russia, whose channel is called ‘Peoples Cyber Army,’ was the channel with the second most followers, only a few thousand less compared to NoName057(16). The Telegram channels of CyberDragon, HackNeT and 22C closed the ranks with about 1,000 members each.
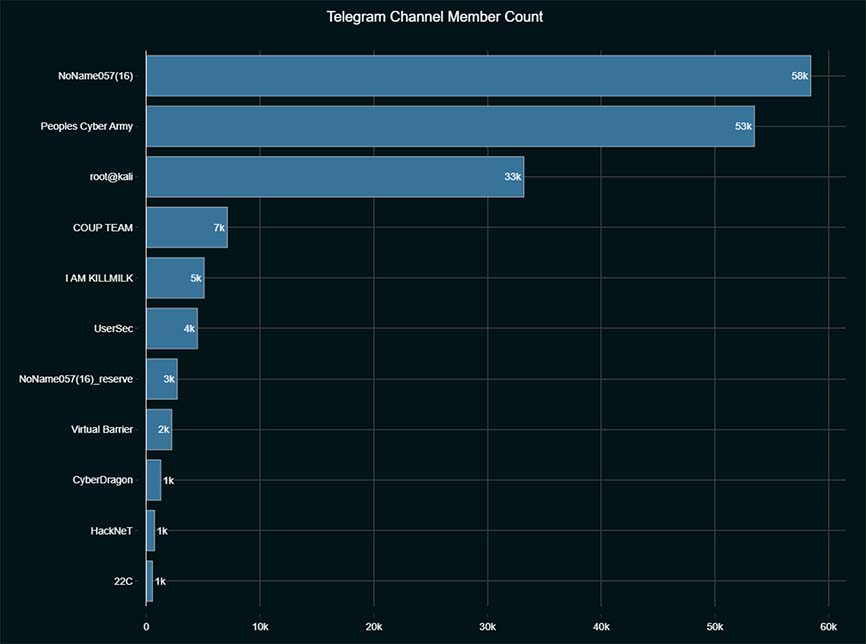 Figure 2: Telegram channel member counts for participating groups (Source: Telegram)
Figure 2: Telegram channel member counts for participating groups (Source: Telegram)DDoS Attacks Claimed on Telegram
Of the nine groups, only five claimed DDoS attacks between June 6 and June 10. NoName057(16), unsurprisingly, claimed the most attacks: 35. HackNeT claimed 18 attacks, CyberDragon 9, the Cyber Army of Russia 8 and Coup Team 1. Note that, as far as I know, HackNeT is not related to the similar-sounding group ‘XakNet Team’ (‘X’ in Russian is pronounced as ‘h’). XakNet Team conducts various threat activities, including DDoS attacks, in support of Russian interests and was identified by Google (Mandiant) as operating in coordination with Sandworm, the advanced persistent threat group operated by Military Unit 74455 of the GRU, the Russian military intelligence service. XakNet Team has been around since March 2022, shortly after Russia invaded Ukraine. HackNeT, in contrast, is a relatively new group that started posting on Telegram in February of this year.
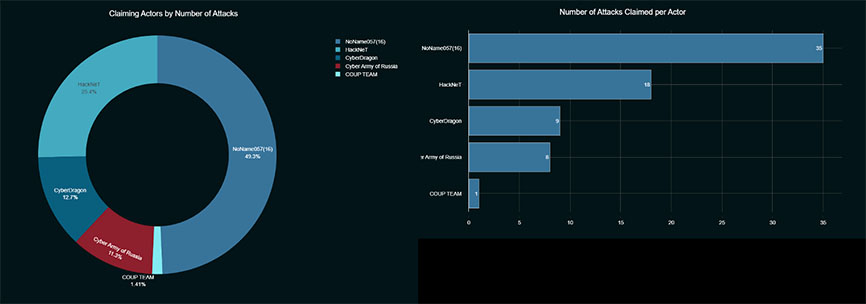 Figure 3: Attacks claimed by actor (Source: Radware)
Figure 3: Attacks claimed by actor (Source: Radware)EU Election Voting Days
The EU election voting is spread over several days and not every country votes on the same day. Most countries in the European Union voted on Sunday, June 9. Estonia, however, was the first to start voting and kept the polling stations open from June 3 until June 9. The Netherlands voted on Thursday, June 6. Ireland voted on Friday, June 7. Czechia voted from Friday, June 7 till Saturday, June 8. Italy, Latvia, Slovakia, and Malta voted on Saturday, June 8.
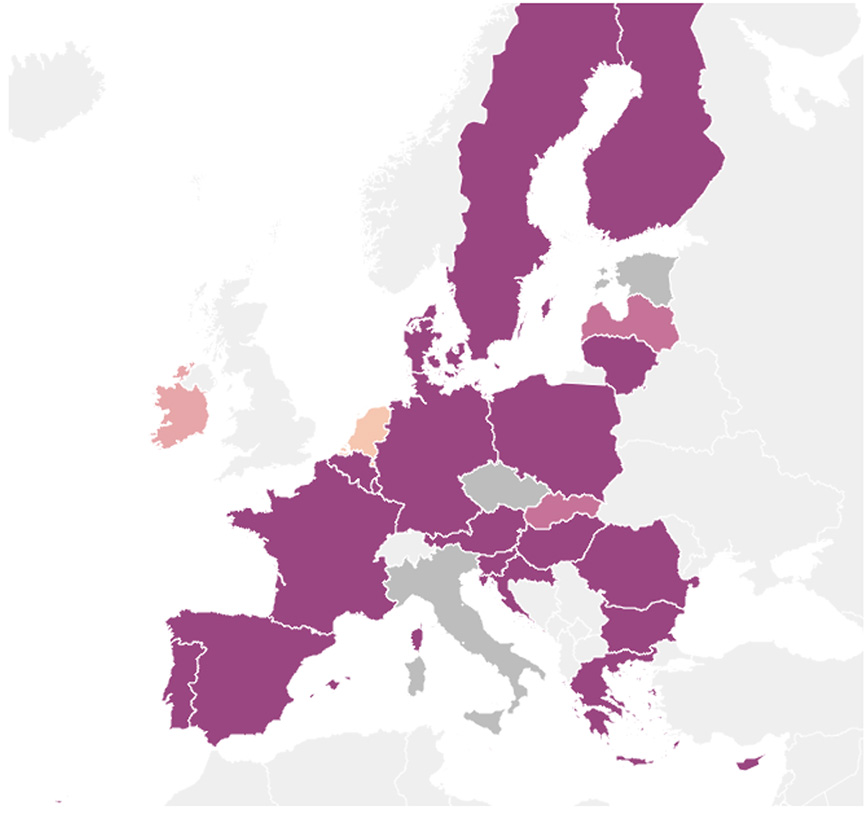 Figure 4: When EU countries vote (source: POLITICO research)
Figure 4: When EU countries vote (source: POLITICO research)DDoS Attacks Claimed per Day
Most DDoS attacks were claimed on Thursday, June 6, and Friday, June 7. All groups, except for Coup Team, contributed to attacks targeting primarily the Netherlands on Thursday and Ireland on Friday.
The attack activity by NoName057(16), HackNeT and Cyber Army of Russia on Monday, June 10, after the elections was not related to the EU election attack campaign. Come Monday, the patriotic hacktivist groups were back to business as usual, targeting countries that demonstrated support for Ukraine.
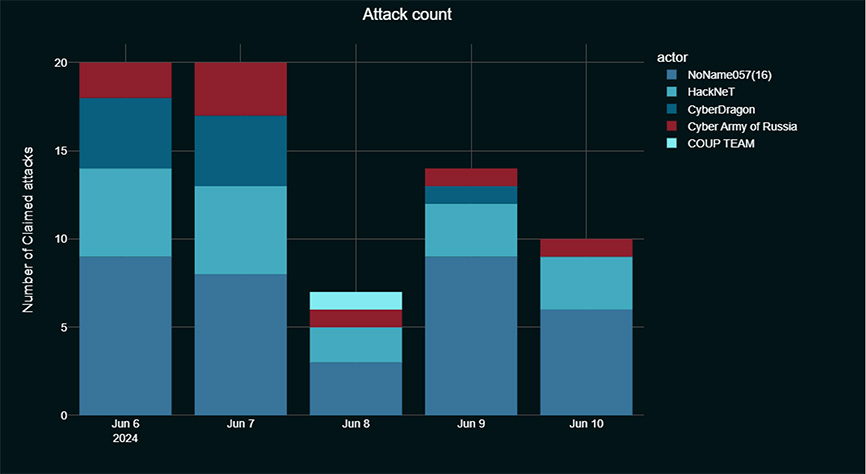 Figure 5: Attack count per day, by actor (Source: Radware)
Figure 5: Attack count per day, by actor (Source: Radware)Targeted Countries
On Thursday, the Netherlands, which voted on the same day, was the most targeted country, with attacks claimed on 13 websites, mostly government and transport related. Three attacks were claimed on targets in Luxembourg, two on targets in Romania and two on targets in Spain.
On Friday, Ireland, which voted on the same day, was the most targeted country with 11 claimed attacks, primarily targeting transport and government websites. France, Czechia and Luxembourg each had three attack claims targeting websites in the country. Czechia, however, was the only country of the latter three where polling stations were open on Friday.
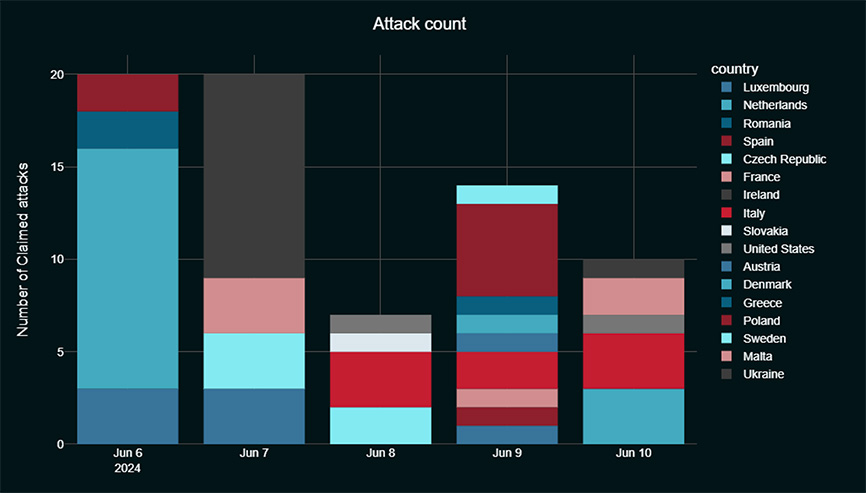 Figure 6: Attack count per day, by country (Source: Radware)
Figure 6: Attack count per day, by country (Source: Radware)On Saturday, June 8, Italy was the most targeted country, with three claimed attacks, while Czechia had two and Slovakia had one attack claim. All three countries had their polling stations open on Saturday. Uncharacteristic of the attack campaign, Coup Team, who performed only one attack during the whole campaign, targeted a social chat service hosted in the United States.
On Sunday, June 9, the last day of voting, when most countries were voting, Poland was the most targeted, with five claimed attacks, followed by Italy, which had two claims. Sweden, Denmark, Austria, Greece, France, Spain and Luxembourg were each targeted once on Sunday.
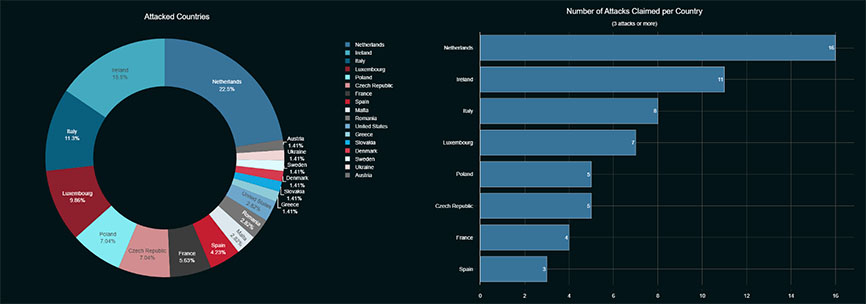 Figure 7: Number of attacks per country (Source: Radware)
Figure 7: Number of attacks per country (Source: Radware)Over the four voting days, the Netherlands was most targeted (16 claims), followed by Ireland (11 claims), Italy (8 claims), Luxembourg (7 claims), Poland (5 claims), Czechia (5 claims), France (4 claims) and Spain (3 claims).
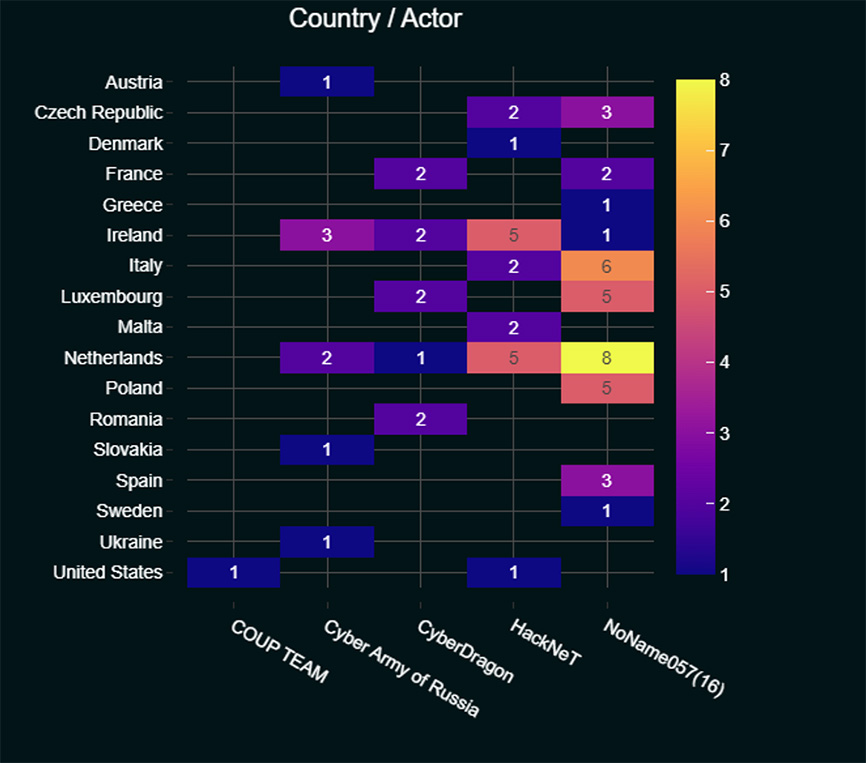 Figure 8: Country/Actor heatmap (Source: Radware)
Figure 8: Country/Actor heatmap (Source: Radware)Most Targeted Web Categories
Overall, transport and travel was the most targeted web category (31 times), followed by government (19 times) and financial services (8 times).
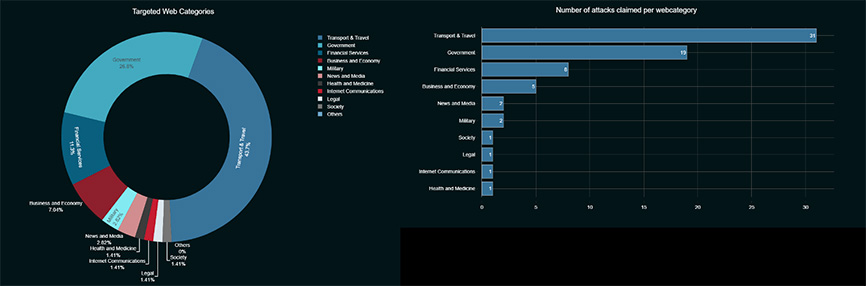 Figure 9: Attacks claimed per web category (Source: Radware)
Figure 9: Attacks claimed per web category (Source: Radware)Transport and travel was the most targeted web category in Ireland while Noname057(16) was the most active attacker for the category. In Luxembourg, financial services websites were the most targeted category while government websites were the most targeted category in the Netherlands. HackNeT primarily attacked government and transport websites.
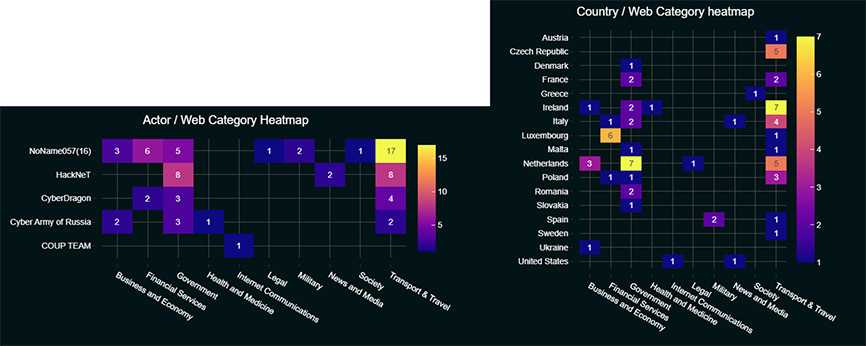 Figure 10: Web category heatmaps (Source: Radware)
Figure 10: Web category heatmaps (Source: Radware)Back to Business as Usual
After the elections, NoName057(16) and its companions got back to targeting countries based on their support of Ukraine, not mentioning the EU elections anymore.
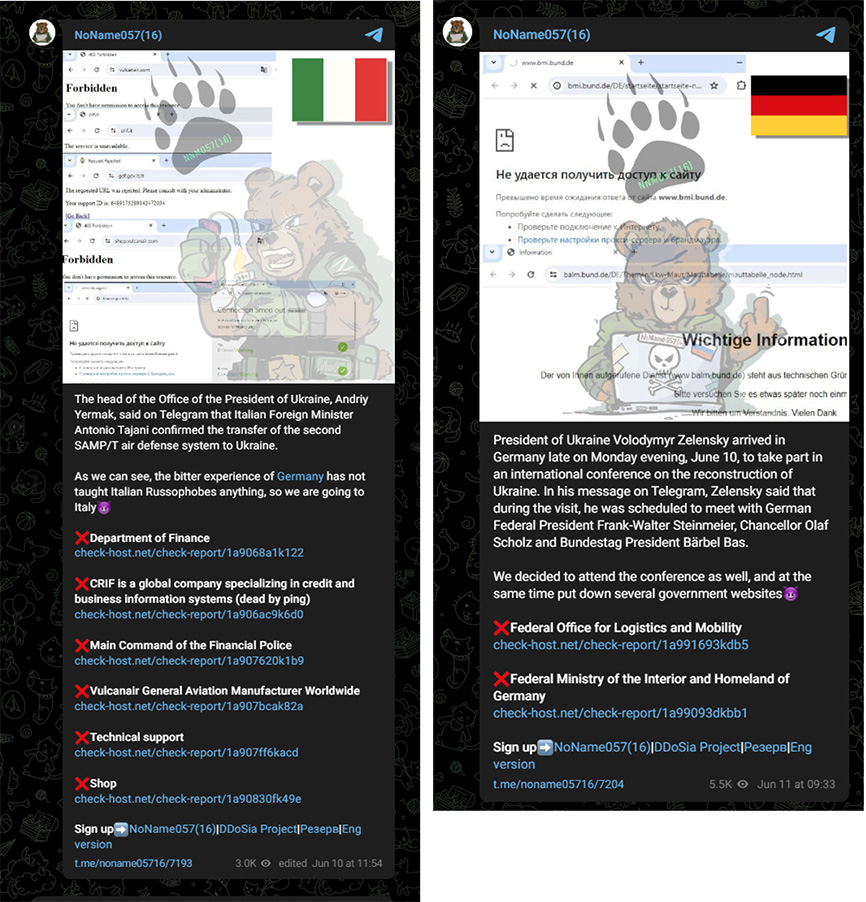 Figure 11: NoName057(16) claiming attacks targeting Italy on June 10 and Germany on June 11 (Source: Telegram)
Figure 11: NoName057(16) claiming attacks targeting Italy on June 10 and Germany on June 11 (Source: Telegram)