In the first blog, I covered how and why gaming has become the primary source of new application security threat actors, from the critical changes in the gaming industry to how gamers get exposed to marketplaces. In this blog, I will examine the evolution of application hackers. By the end of this six-minute read, you will understand how script kiddies evolve into cybercriminals-as-a-service in only a few months.
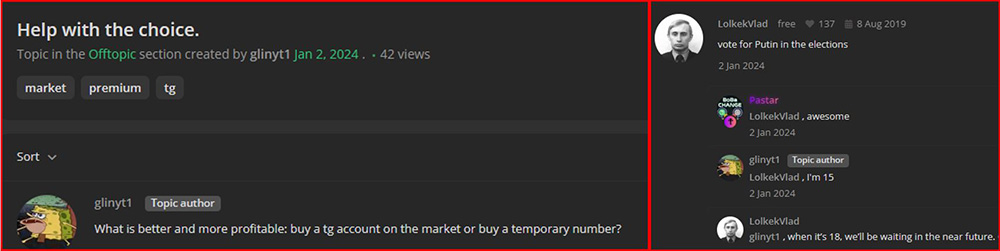
Figure1: 15 Y.O. teen asks in marketplace forums what type of account is more suitable for running telegram bots.
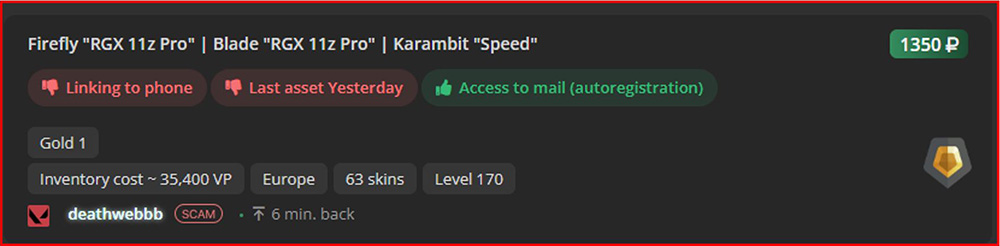
Figure2: Breached gaming account. The main bait that pulls gamers into the underground marketplace.
The Gamer to Hacker Timeline
Step 1: Exposure – Gamers’ first exposure to underground marketplaces
The first part in this blog series covered how gamers get exposed to hacker marketplaces.
Step 2: Division into types of hacking - Hackers’ first career decisions
In our first blog post, we discussed the emergence of hacker marketplaces and how users tend to spend a few months experimenting with hacking tools and tutorials. As they gain experience, gamers often focus on specific hacking techniques and domains, typically related to their game genre.
For example, gamers who enjoy First-Person Shooter (FPS) games, known for their fast-paced and high-adrenaline gameplay, often have an interest in cyber-attacks that provide a similar experience. Two popular types of attacks for this group are account takeover (ATO) attacks and Denial of Service (DDoS) attacks. These attacks are quick and intense, aligning with the psychological "need for speed" of the typical hacker persona.
Strategy game players tend to develop more strategic and puzzle like skills such as reversing and de-obfuscation techniques to interpret and understand code in application defenses. This technical skill is critical for hackers. Understanding defensive techniques and code allows them to develop new methods to bypass these security systems.
Gamers who primarily play Role-Playing Games (RPGs), a genre that requires familiarity with game lore, uncovering secrets through dialogue, research, and exploration, tend to professionalize in active and passive reconnaissance, the pre-attack intelligence gathering phases in the cyberattack chain. These individuals also find themselves equipped with the skills for scamming and stealing sensitive information through social engineering.
Step 3: Hacker Baptism - First hands-on hacking activity
In this stage, gamers evolve into unexperienced hackers or ‘script kids.’ The first hacking attempt is a significant milestone in a hacker’s evolution. It could be their first breached account or their first DDoS attack against a gaming server after losing a game or tournament. This experience leaves the hacker with a sense of power and an adrenaline rush they will strive to recreate. The hacker feels like they have leveled up and, in the process, developed three critical skills:
- Self-learning without a structured framework: hacking techniques evolve rapidly, so the only way to learn is through tutorials and hands-on experience.
- High failure tolerance: initial attack attempts are unlikely to succeed. A hacker needs to build persistence and have strong psychological traits to avoid burnout.
- Proactively seeking assistance: hacking requires various expertise. A hacker can buy tools or consult with forum members for best practices in its self-development.
Step 4: Proactivity - Turning from the silent viewer into the proactive player
In this step, the new threat actor is eager to build his or her reputation as a contributing member within their hacking communities on Discord, Telegram, and underground forums. To achieve this goal, they employ similar techniques as used by popular social media influencers:
- Sharing "freebies" - hackers share hacking resources, such as breached account credentials, for free.
- Engaging in challenges and competitions to demonstrate their skills and earn clout and prizes.
- Providing tutorials and guides to position themselves as experts and gain followers.
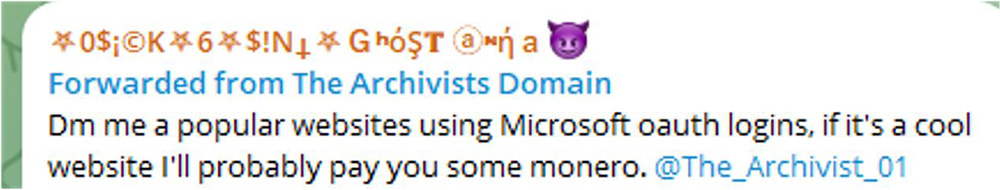
- Collaborating with other well-known figures in the community on joint projects to expose themselves to new audiences and gain credibility.
- Leveraging memes and humor to come across as relatable and entertaining.
The goals are building their reputation, gaining credit on the forum, and getting access to more exclusive content. By becoming well-known in the community, the hacker can attract customers and collaborators for future business ventures in the hacking marketplaces.
Step 5: Business owner - Turning from buyer into seller
In this step, the new threat actor is eager to monetize their skills and build a sustainable business in the underground marketplaces. They transition from becoming a consumer of hacking tools and services into a provider.
To achieve this, they employ tactics similar to startup founders:
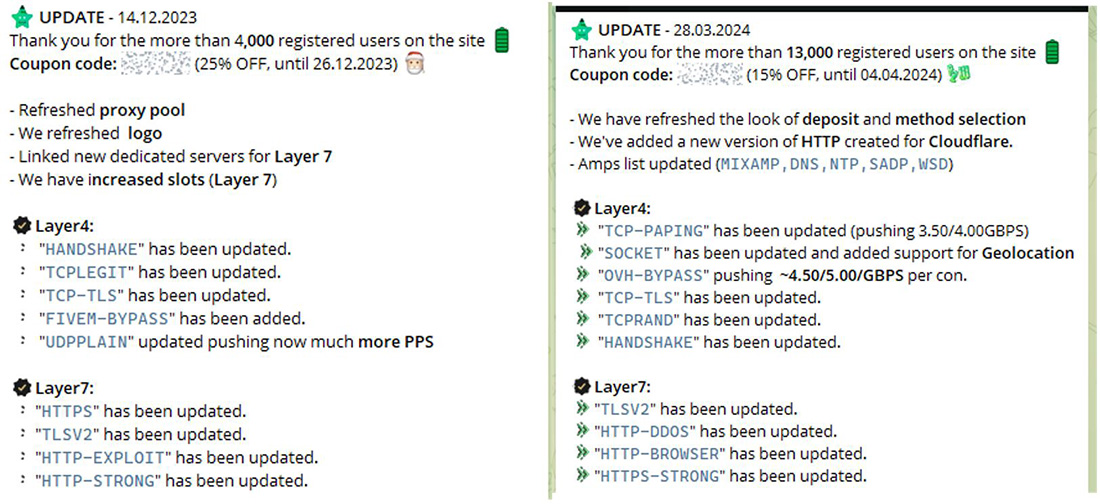
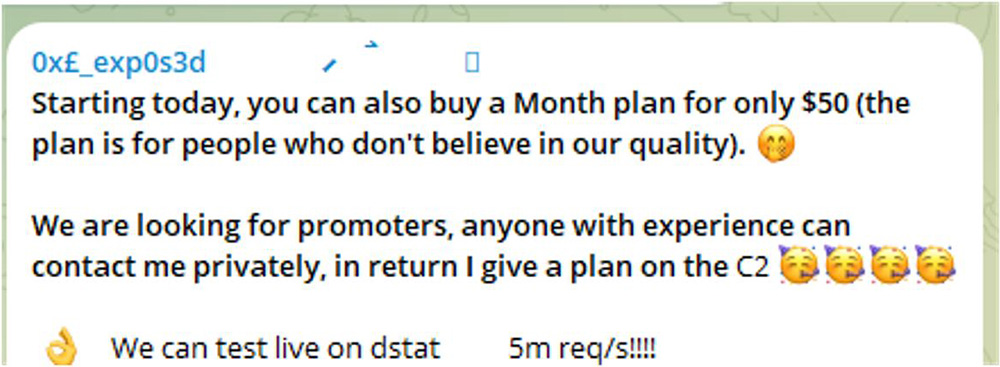
- Developing a unique value proposition—The hacker identifies a gap in the underground market and focuses on developing a tool or service that better fills this need than any existing offerings. This could be a more effective account cracking tool, a stealthier malware strain, or a DDoS-for-hire service with better service levels and greater impact guarantees.
- Building an MVP (Minimum Viable Product)—With the unique value proposition in mind, the hacker builds a basic version of the tool or service. They leverage coding and hacking skills acquired in previous steps to create a functional offering, even if it lacks polish.
- Marketing and promotion—the hacker promotes the new tool or service on underground forums and chat groups where they gained reputation. They offer discounts to early adopters and quietly seed positive reviews to generate buzz and establish credibility.
- Scaling up—As their customer base grows, hackers reinvest profits into better infrastructure to support more users and optimize their attacks. They begin recruiting affiliates and resellers to expand their sales channels.
Step 6: Sustainability - Operating a hacking tool for more than six months
In the final stage of its evolution, the gamer-turned-hacker has achieved a steady state of business operations with a stable income stream. Key focuses at this stage include:
- Diversification - expanding offerings to include multiple attack vectors and targets.
- Professionalization - implementing customer support, SLAs, tiered pricing, and other trappings of legitimate businesses.
- Reputation management - carefully guarding their standing and brand on the underground markets.