DoH, or DNS over HTTP/S, is a secure protocol that facilitates encrypted DNS resolution through an HTTPS connection. Unlike traditional DNS resolution methods that utilize unencrypted TCP or UDP connections, DoH offers an increased level of security and privacy. In DoH, the DNS query is encrypted and transmitted as an HTTP message, using the same port as other HTTPS traffic (port 443). This provides a layer of privacy and security, as the DNS query is no longer sent in clear text.
Not All Internet Service Providers (ISPs) Support DoH
DoH is supported by many popular web browsers and operating systems and can be enabled through their settings. With its usage growing rapidly in the United States, many browsers have enabled it as the default setting. Public DNS resolvers have also added support for the protocol.
However, not all internet service providers (ISPs) currently offer support for DoH, although many plan to implement it soon. While DoH provides several benefits, such as increased security and privacy, it also presents several challenges that ISPs need to consider when implementing the protocol.
What prevents Internet Service Providers from supporting DoH?
Implementing DoH can present some challenges for service providers. Some of the challenges include:
- Encryption overhead: DoH requires encryption of DNS queries and responses, which can add overhead to the communication. This can result in increased latency and higher resource utilization for the service provider.
- Protocol compatibility: DoH requires the use of the HTTPS protocol, which may not be supported by all client devices or applications. Service providers may need to provide alternative DNS resolution options for clients that do not support DoH.
- Infrastructure updates: Service providers may need to update their DNS infrastructure to support DoH, including updating DNS servers and configuring new DoH servers. This can require significant resources and expertise.
- Traffic visibility: DoH encrypts DNS queries and responses, which can make it more difficult for service providers to monitor and analyze network traffic. This can make it more challenging to detect and mitigate potential security threats.
- Regulatory compliance: Depending on the region or country, there may be regulations or legal requirements, such as data privacy or encryption regulations, that service providers need to comply with when implementing DoH.
- Security: Exposure to application-level threats such as SSL/TLS vulnerabilities, man-in-the-middle (MitM) attacks and the need for challenge-response mechanisms are some of the security issues that need to be considered. DNS over HTTPS (DoH) is designed to securely transport DNS queries and responses over HTTP/2, but it does not cover zone transfer (XFER) requests. XFER requests are used to transfer a full copy of a DNS zone from a primary server to a secondary server, and typically use the AXFR or IXFR protocol. XFER requests are typically performed over TCP port 53, which is the standard DNS port and will still require support for DNS.
Overall, implementing DoH can require significant resources and expertise from service providers, and may require additional measures to maintain network visibility, security and compliance.
Is there a cost-effective way for Internet Service Providers to support DoH?
A DoH gateway provides a cost-effective means of deploying DoH because it allows ISPs to offer the service without having to upgrade or add DNS servers. A DoH gateway serves as an intermediary between the client and the DNS server by converting encrypted DoH traffic into standard DNS over UDP traffic.
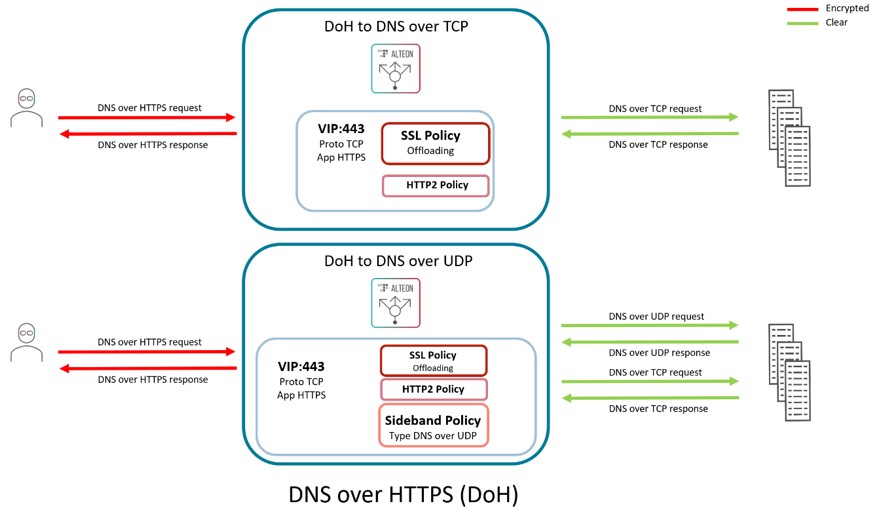
The DoH gateway must be capable of managing the establishment of TCP and SSL connections, decoding DNS queries from HTTP requests and forwarding them to the DNS server. Before being transmitted to the client, the server’s response must also be encrypted and wrapped in HTTP. For a DoH gateway capable of handling high levels of traffic required by ISPs, it is necessary to use a platform with significant CPU resources and hardware SSL acceleration.
For More Information
For over 20 years, Radware has helped ISPs navigate the cybersecurity waters to stay secure and keep their customers safe. Whether it’s implementing DDoS or 5G protection for service providers or helping them grow revenue and margins by offering managed security service provider (MSSP) services, Radware’s cybersecurity experts have the experience and know-how to make it happen. Contact them HERE. They would love to hear from you.