What Are Botnets?
Botnets—a combination of the words “robot” and “network”—are networks of hijacked computers and internet-connected devices that are infected by malware (i.e., malicious software). The malware runs bots on the compromised devices without the knowledge of device users.
Botnets are usually controlled by a botmaster or bot herder. The bot herder turns these hijacked computer devices into remote-controlled “zombie” computers. By linking compromised devices in large numbers, it becomes possible to create botnets that can be leveraged against various targets to carry out distributed denial of service (DDoS) attacks, account takeover, data theft and several other types of attacks.
This is part of a series of articles about bot protection.
In this article:
What is an IoT Botnet? | A Radware Minute
Botnets are used by threat actors for several types of malicious activity:
Email spam: Botnets have often been used to widely distribute email spam. This allows for drive-by downloads triggered without user intervention, phishing links that fool unsuspecting users into clicking and automatically installing malware, and various other malicious acts.
Financial breaches: Botnets are known to have infiltrated financial institutions including banks and payment processors to exfiltrate confidential consumer and business data, which can be further used to carry out other forms of fraud.
Information theft: Malicious actors have used botnets to cast a wide net to steal personal and organizational data which can be further abused to carry out fraud, impersonation, blackmail and financial crimes.
Targeted intrusions: Botnets can be used to execute credential stuffing attacks, in which lists of breached and stolen username and password pairs are rapidly entered to gain access to devices and user accounts, both on devices and websites or applications. In a similar manner, botnets can also be used for credential cracking attacks, in which random passwords are generated and entered in the hope of eventually guessing the correct password.
DDoS attacks: Botnets have been responsible for some of the most large-scale distributed denial of service (DDoS) attacks. Through their sheer volume, these attacks can slow down unprotected networks and servers, and disrupt the normal functioning of websites, mobile applications, and APIs. DDoS attacks have often been linked to criminal networks and nation states with the intention of crippling or even bringing down their adversaries' networks. They can affect the normal functioning of public goods such as power, water, sanitation systems, financial institutions, marketplaces and other types of targets that can cause inconvenience, disruption, or frustration to their users.
Ad fraud: Botnets have been used to execute ad fraud, in which legitimate ads and their embedded links are replaced by fraudulent ads with embedded links that bring traffic (and potentially, revenue) to websites controlled by the bot herder. Botnets are also used to generate fake clicks on ads to generate false impressions and game the ad-tech ecosystem for profit.
Crypto-currency mining and fraud: Botnets can leverage the processing power of thousands or even millions of infected devices to mine crypto-currencies and steal access to coin lockers or wallets.
Learn more in our detailed guide to botnet defense tools.
Bot herders create botnets by spreading malware to infect PCs, smartphones and internet of things (IoT) devices including security cameras, smoke detectors, digital video recorders and many other smart devices. This is achieved through various means such as social engineering, website and application vulnerabilities, exploit kits, and Trojan software which infect targeted devices without alerting their owners.
Exploit kits can be purchased on the dark web or created by hackers and are often concealed in seemingly legitimate downloadable files, including free software, music, or video content. Malware can even be of the self-installing “drive-by” type that is widespread on shady websites, and doesn’t even need to be clicked on to infect a device.
After the bot software is installed on compromised zombie computers, they are ready to receive commands from their bot herders to execute actions based on the intentions of their controller. The controller of a botnet can direct its activities through communication channels based on network protocols such as IRC and HTTP, both as peer-to-peer networks or directed by a central command and control (C&C) device.
Distributed Denial-of-Service (DDoS) Attacks
In a DDoS attack, the bot herder instructs the botnet to flood a target server or network with excessive traffic, overwhelming its capacity and causing service disruptions. By sending massive amounts of requests simultaneously from thousands of compromised devices, the attack prevents legitimate users from accessing the service.
Botnets carrying out DDoS attacks have affected large-scale targets, including government websites, online gaming platforms, and financial institutions, often resulting in downtime and financial loss.
Spam Distribution
Botnets are frequently used to distribute spam emails, which can contain malicious attachments, phishing links, or other harmful content designed to deceive recipients. By sending spam from a vast number of infected devices, bot herders can bypass spam detection mechanisms and amplify the reach of their campaigns.
Spam botnets are also used for “drive-by downloads,” where malicious software installs automatically when recipients open certain emails, further expanding the botnet.
Credential Theft
Botnets facilitate credential theft by running large-scale attacks aimed at harvesting login details for accounts. This includes credential stuffing, where breached usernames and passwords are repeatedly tested against various services to gain unauthorized access.
Botnets may also use keyloggers to capture keystrokes, stealing credentials from infected devices directly. Stolen credentials are often sold on underground markets or used to conduct identity theft, fraud, and further cyberattacks.
Click Fraud
Click fraud botnets manipulate online advertising by generating fake clicks on ads, making it appear as though users are engaging with the content. Each infected device mimics genuine user behavior, driving fraudulent ad impressions or clicks that lead to ad revenue for the bot herder.
This threat costs advertisers millions in wasted ad spend and also undermines the integrity of the ad-tech ecosystem by skewing performance data and inflating campaign costs.
Cryptocurrency Mining
Botnets can also be used for illegal cryptocurrency mining by exploiting the processing power of infected devices. Each compromised device in the botnet contributes its CPU or GPU resources to mining cryptocurrencies like Bitcoin or Monero, without the device owner’s knowledge.
This unauthorized mining can degrade device performance, increase electricity costs, and reduce the lifespan of the hardware. Mining botnets are highly profitable for attackers, especially when they consist of thousands of high-performance infected devices.
Botnets can perform the same functions as individual bots, but on a far larger scale. They're able to carry out often overwhelming attacks on their targets. Though most conventional bots are based on scripts and web browsers, botnets can also be built on malicious software that is designed for rapid infestation across many vulnerable devices.
Once installed, the botnet software can often function with administrative privileges on the infected device. This gives bot herders virtually unhindered access to the device’s memory, processor, data storage and allows the botnet controller to remotely execute any actions that the device user is capable of performing.
Botnets are capable of:
- Reading and writing system data
- Gathering personal data from infected devices
- Sending files and other data
- Monitoring users’ activities
- Searching for vulnerabilities in other devices
- Installing and running any applications
Command and Control (C&C) of botnets are generally carried out by two methods:
Centralized: The Client-Server Botnet Model
The first known botnets initially used to be exclusively controlled using client-server models in which a domain, website, or Internet Relay Chat channel controlled by the bot herder is contacted by the bot software on infected devices to both receive orders and transmit data back to the controller. This centralized command model is rarely used anymore as various global law enforcement and security agencies have tracked and shut down their central servers in recent years, thus crippling botnets that were based on this model.
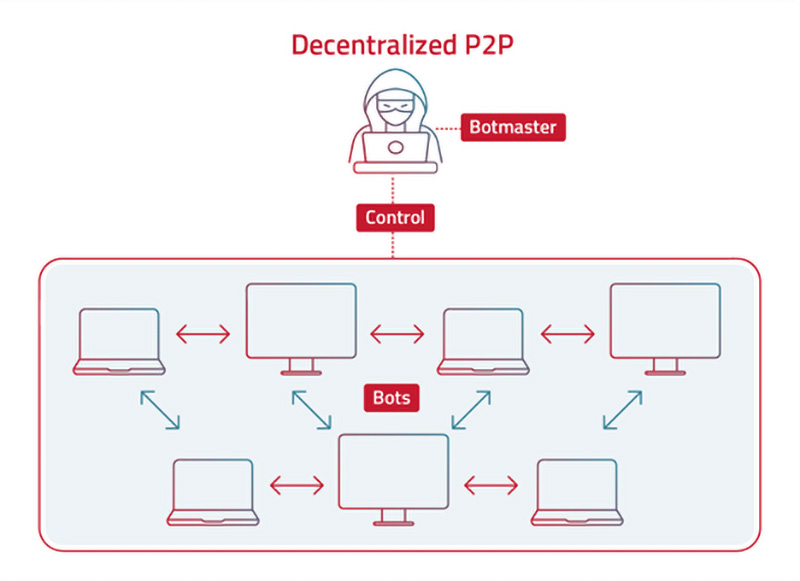
Decentralized: The Peer-to-Peer Botnet Model
Due to aggressive action by security agencies in cracking down on centralized C&C botnet servers around the world, the decentralized P2P model is now almost universally used to control botnets. This eliminates centralized control which has a single point of failure that is vulnerable to being shut down by law enforcement agencies and replaces it with decentralized peer-to-peer control. P2P botnets find other infected devices by scanning random IP addresses to establish contact. If a machine is infected, it conveys its list of installed bots to the infected machine that contacted it, which can then relay updates and commands from the botnet controller to herd the new additions to the botnet to execute commands.
As bot technology and the sophistication of botnets grow increasingly more capable and powerful, new, record-setting botnets are uncovered every few months that eclipse the size and attack potential of previous botnets. Three of the largest, most damaging botnets in the recent past have been:
Mirai Botnet
The Mirai botnet was uncovered in 2016 and was responsible for massive 1 Terabit/second DDoS attacks on OVH, a French web hosting firm. Dyn, a DNS service provider, was also attacked by Mirai, which took some of the most prominent websites around the world offline, including Netflix, Twitter, Reddit and Github.
3ve Botnet
3ve was a botnet used to carry out ad fraud using nearly 2 million PCs and over a million compromised IP addresses. It clicked on ads on over 10,000 fake websites and raked in an estimated $30 million in fraudulent gains before it was taken down by the FBI.
Mantis Botnet
In 2022, a small but incredibly powerful botnet named “Mantis” infected a relatively small number of about 5000 servers and launched an unprecedented 26 million RPS (requests-per-second) DDoS attack using the HTTPS protocol against ISP, media, telecommunications, finance, and gaming websites. Using powerful servers rather than far less powerful IoT and desktop PCs allowed the Mantis botnet to carry out HTTPS attacks that require far more computational resources to execute.
HTTP/2 Rapid Reset Vulnerability
The HTTP/2 rapid reset vulnerability exploited a flaw in the HTTP/2 protocol, which allows attackers to trigger a rapid series of reset streams to overwhelm a server. Attackers leveraged this vulnerability to create record-breaking distributed denial of service (DDoS) attacks that involved millions of requests per second.
The HTTP/2 protocol’s popularity among high-performance websites and applications increased the potential impact, as many major services rely on it. These attacks, which could cause severe service interruptions, were especially effective against services dependent on HTTP/2, prompting patching and protocol updates from affected vendors to mitigate further risks.
911 S5 Botnet
The 911 S5 botnet was a significant threat that operated a vast network of proxy servers by compromising devices, allowing attackers to access these proxies for various malicious purposes, including hiding their activities behind the legitimate IPs of infected machines.
This botnet allowed criminals to perform activities such as ad fraud, credential theft, and other cybercrimes using the stolen IPs to evade detection. An international law enforcement collaboration dismantled the 911 S5 botnet, leading to the arrest of its administrator and disrupting its operations.
1. Network Security Measures
Implementing strong network security measures is crucial for defending against botnets. A well-configured firewall can block malicious traffic from entering the network, and intrusion detection systems (IDS) or intrusion prevention systems (IPS) can monitor traffic for suspicious patterns.
Network segmentation helps isolate critical systems, limiting the spread of malware if a device is compromised. Regular network traffic analysis is essential for detecting anomalies, such as unusual communication patterns indicative of botnet activity. Organizations should also regularly patch network devices like routers and switches to close vulnerabilities that botmasters might exploit.
2. Bot Management
Effective bot management is key to preventing botnet attacks and mitigating their impact. One approach involves deploying advanced bot detection tools that can differentiate between legitimate users and automated bot traffic based on behavioral analysis. These tools use machine learning algorithms to recognize anomalies in request patterns, device characteristics, and session activity, helping to identify and block malicious bots in real-time.
Integrating bot management solutions with web application firewalls (WAFs) can provide an added layer of security, blocking requests from known botnet IP addresses and suspicious traffic sources. Another crucial aspect of bot management is rate limiting and CAPTCHA enforcement. By implementing rate limiting, organizations can restrict the number of requests a user or bot can make within a given timeframe, reducing the impact of automated attacks. CAPTCHA tests are effective against simple bots that cannot solve human verification challenges, deterring many types of automated abuse.
3. Endpoint Protection
Endpoint protection is critical to stop botnets from infecting individual devices. Using a comprehensive endpoint detection and response (EDR) solution ensures that all devices connected to the network are monitored for malware, suspicious behavior, and known botnet signatures.
Antivirus and anti-malware software should be kept up to date on all endpoints to detect and remove threats. Additionally, organizations should enforce strict policies for software installation, requiring users to only install applications from trusted sources. Regular device scanning and patch management practices further reduce the risk of malware infections.
4. Email and Web Filtering
Many botnets propagate through phishing emails and malicious websites. Email filtering solutions can block phishing emails and attachments that contain malware. These filters scan incoming messages for indicators of compromise, such as suspicious links, untrusted domains, or known malicious attachments.
Similarly, web filtering software can prevent users from accessing malicious websites where botnet malware might be hosted. By blocking access to high-risk domains and URLs, web filters protect against drive-by downloads that could compromise a device without user interaction.
5. Access Controls and Authentication
Implementing robust access controls and multi-factor authentication (MFA) can prevent botmasters from exploiting compromised credentials to expand their botnets. Role-based access controls (RBAC) should be employed to limit access to sensitive systems and data, ensuring that even if a botnet compromises a device, its access is restricted.
MFA adds an additional layer of security, requiring more than just a password for authentication. This significantly reduces the likelihood of successful credential stuffing or brute-force attacks orchestrated by botnets.
6. User Awareness Training
Educating users is a fundamental defense against botnets. User awareness training should focus on identifying phishing emails, avoiding suspicious downloads, and practicing good cybersecurity hygiene, such as using strong, unique passwords. Regular simulations of phishing attacks can help reinforce this training.
Users should also be trained to report any unusual device behavior, which could indicate that a botnet has compromised their machine. By fostering a security-conscious culture, organizations can minimize human errors that lead to malware infections.
7. DDoS Mitigation
Organizations should implement DDoS mitigation strategies to protect against botnet-driven attacks. This includes deploying DDoS protection services, such as cloud-based scrubbing solutions, which can absorb and filter out malicious traffic before it reaches the target network. Rate limiting and traffic shaping can also help manage excessive traffic loads during an attack.
Additionally, working with internet service providers (ISPs) to reroute traffic during an attack can help maintain service availability. Regularly testing DDoS response plans ensures that the organization is prepared to respond quickly and effectively if an attack occurs.
Bot Mitigation
The most crucial security defense against botnets is a solution such as Radware Bot Manager. Our solution leverages a combination of Radware’s patented intent-based deep behavioral analysis, collective bot intelligence, semi-supervised machine learning, device and browser fingerprinting, and anomaly detection based on variance from normal user flows.
Account Takeover (ATO) Protection
Radware Bot Manager protects against Account Takeover attacks, and offers robust protection against unauthorized access to user accounts across web portals, mobile applications, and APIs. Utilizing advanced techniques such as Intent-based Deep Behavior Analysis (IDBA), semi-supervised machine learning, device fingerprinting, and user behavior modeling, it ensures precise bot detection with minimal false positives. The solution provides comprehensive defense against brute force and credential stuffing attacks, and offers flexible bot management options including blocking, CAPTCHA challenges, and feeding fake data. With a scalable infrastructure and a detailed dashboard, Radware Bot Manager delivers real-time insights into bot traffic, helping organizations safeguard sensitive data, maintain user trust, and prevent financial fraud.
DDoS Protection
In addition to bot detection and mitigation, solutions such as Radware’s Cloud DDoS Protection Service and DefensePro are an essential component to prevent DDoS attacks, which are one of the hallmark applications of malicious botnets.