Over the last several weeks, we have all become conditioned to mega leaks. 117 million from LinkedIn, 360 million from MySpace, 68 million from Tumblr and 127 million from Badoo. That’s over a half a billion emails and usernames up for grabs! This is a gold mine for hackers. Researchers are not the only ones that obtain and analyze leaked databases. Often times, hackers will keep databases for themselves so they can conduct malicious activity with the credentials.
But what if the hackers do not wish to use the data? If the hacker’s intention is to profit from the data, they will usually list it for sale on a number of different Darknet markets. While there are a number of items that one can find on the Darknet, in this blog I will be talking about buying and selling items related to fraud.
Fraud has always been a big business for hackers, but now they have semi-legitimate markets where they can publicly sell their stolen goods. On a number of different Darknet sites, you can purchase anything from accounts & bank drops, to data dumps, personal information and credit cards. Most of the time you don’t even have to look that hard to find them.
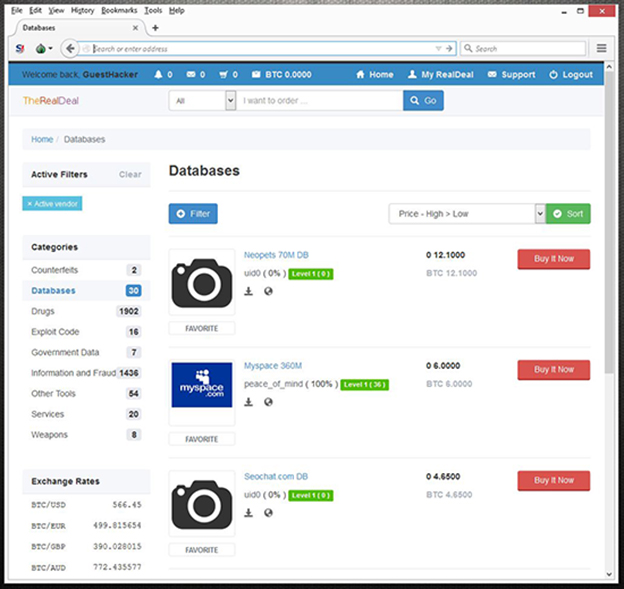
TheRealDeal (a Darknet market) has been very popular lately. This is the marketplace where the hacker, Peace of Mind, has been selling old databases that have never been publicly released. On this site, the hacker or hackers behind this account are selling user credentials for a fraction of a cent. For just a few Bitcoins, you can own over 100 million usernames and password. This is huge. Most people today still reuse old passwords and have the same login credentials across multiple platforms. An attacker can use this data set in an attempt to take control of another personal account to gain even more information, or they can use the email list for large scale phishing campaigns.
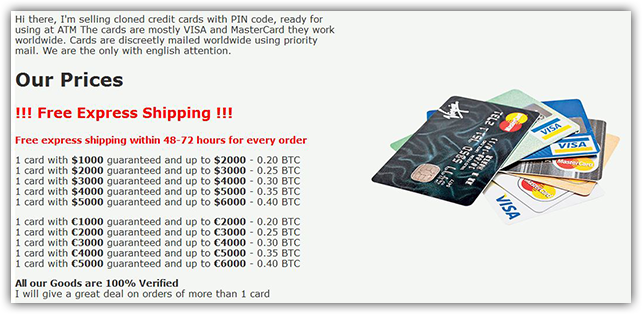
Another item that you can find on the Darknet is personal information, including PayPal accounts, credit cards, identification and Social Security numbers. I find this very concerning. You can purchase “Fullz,” which is carder slang for full personal package. A full package of data includes first name, last name, address, city, state, zip, e-mail, DOB, IP address, phone number and SSN. The sad truth is a Fullz package goes for as little as .0008 BTC or around 45-50 cents per record. Some CCV vendors also sell cloned credit cards with PIN numbers provided by professional skimmers. These clones are mainly VISA and MasterCard accounts and can even be used at ATMs. One vendor sells clone cards individually. One card with a $5,000 guarantee can sell for as little as .40 Bitcoin, or around $200.
[You might also like: How Mark Zuckerberg’s LinkedIn, Twitter and Pinterest Accounts were Compromised]
You can even purchase hacking services to hijack accounts and steal personal information. There are a number of sites on the Darknet that offer Facebook, LinkedIn, Twitter, Instagram and Gmail hacking services. These services normally sell for around .5 Bitcoin, or $250. If you want to steal information off of a website or server via an SQL injection, the price varies but usually starts around 1 Bitcoin or $500.
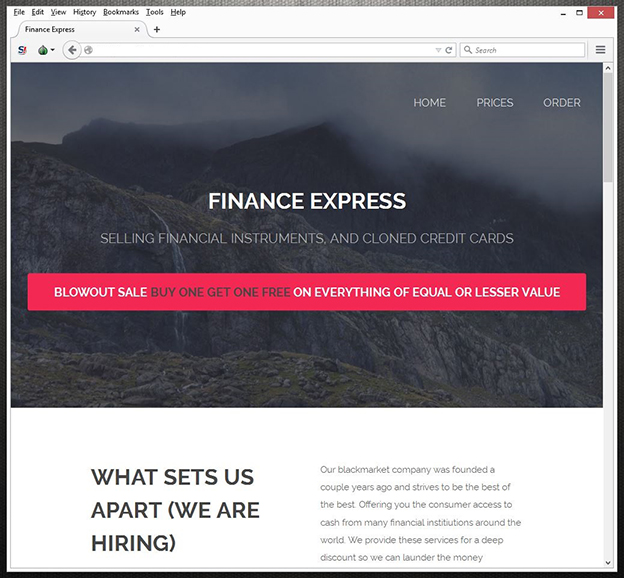
The Darknet can be a very scary thing when it comes to fraud. Fraud takes up a large section of most markets. Almost every marketplace has a fraud category that is loaded with fresh credit cards and personal information.
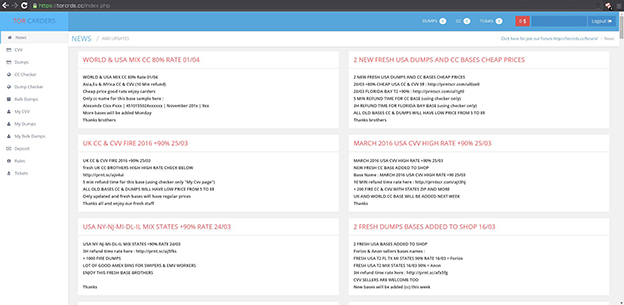
In the long run, there is not much you can do to stop this activity. Fraud has and always will be a cornerstone for hackers. The Darknet has only provided them with a market to sell their goods with some layer of protection. However, the Darknet is not the only place that you can find this kind of information. Sites like TorCrds also sell stole credit card number on the Clearnet.
In the end, it really comes down to your personal security. First and foremost, always be on alert for phishing emails. Recently, PhishMe reported that 93% of phishing emails contain ransomware, but phishing emails are also designed to steal information from unwary users. In addition to this, it’s also recommended to monitor your credit and bank statements, keep your system up to date with the latest updates and patches, use strong passwords and use 2 factor authentication when possible. You should also disable any file sharing services not in use. While browsing, be careful where and who you give your personal information to. Always verify the company that you are doing business with and always use encryption. If you store personal data and files on your computer, consider using encrypted file storage.
In the end, if you suspect that you are a victim of fraud, report it to the authorities right away. You can also file a complaint with the FBI’s Internet Crime Complaint Center, IC3.
Additional information can be found at:
https://www.usa.gov/online-safety
http://www.actionfraud.police.uk/
Download Radware's DDoS Handbook to get expert advice, actionable tools and tips to help detect and stop DDoS attacks.
Download Now