Education, freedom and knowledge. These are the pillars for higher learning, but have often been used to describe some open source projects and services that have the potential to be abused by those that are not so innocent. Over the last two years, tools like stressers, Remote Administration Tools (RAT) and ransomware have been published under these pretenses, but do they serve a legitimate purpose? These projects have set off an international debate in the information security community and many wonder if they should be available to the public. Often the justification for these projects is that they are intending to show the potential risks so they can be used to prevent infections or reduce potential damage. With stressers, they claim that the services are to be used to improve and test security products and to understand attack behavior targeting their network. But are they?
Ransomware has been at the center of this discussion for about two years now. Ransomware is a malicious type of software that is designed to lock users out of a computer system until the victim pays a ransom to the attacker, normally in Bitcoin. Reports from PhishMe suggest that in Q3 2016, 97% of all phishing emails contained ransomware, while a security expert who requested to stay anonymous told CSO Online that ransomware authors took in close to $1 Billion in 2016. Another group, Malware Hunter Team, reports that there are over 300 different ransomware variants in existence! This is truly a growing problem.
Sites like Github are important to programmers. It gives them the ability to showcase and publish their work, but some projects on the website can be easily used for malicious intent. In 2015 a user and security researcher Utku Sen published Hidden Tear, an open source ransomware project, on Github and argued that it was for educational purposes so students and other researchers could gain a deeper insight into how ransomware works. Others argued that this project laid out the basics for actual malware and those that couldn’t create the software on their own could now do so. In the end, Hidden Tear was abandoned and ultimately detected by antivirus software. But the discussion doesn’t stop there. In 2016, Bleeping Computer’s Lawrence Abrams spotted a strain of ransomware called Magic that had been built using an open source ransomware code, eda2, designed for educational purposes only.
[caption id="attachment_6588" align="aligncenter" width="624"]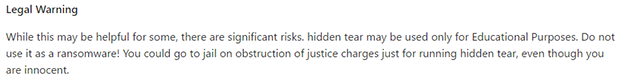 Hidden Tear Legal Warning[/caption]
Hidden Tear Legal Warning[/caption]
Recently Catalin Cimpanu from Bleeping Computers wrote about a service that I discovered called Ranion. Ranion offers Ransomware-as-a-Service on the Darknet and is labeled as “Education purposes only.” The vendor clearly states that the service is for education purposes only but provides a fully functional piece of malware, including an anonymous command and control dashboard to manage your “clients,” also known as “victims”. The vendor even goes as far to offer free customization and will not take any fees from your clients. The service sells for .95 BTC.
[caption id="attachment_6589" align="aligncenter" width="624"]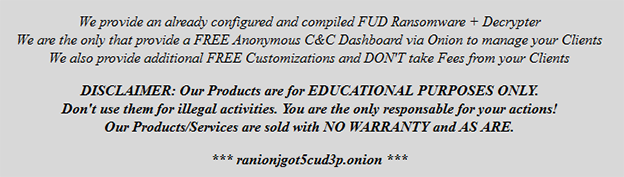 Ranion – Ransomware-as-a-Service[/caption]
Ranion – Ransomware-as-a-Service[/caption]
It’s not just ransomware. On Github you can find several projects labeled as “educational purposes only”including Remote Administration Tools (RATs), like Blackhole. The debate around these open source projects ultimately comes to two points. Those that are new to the industry or still students need to understand how these pieces of malware work by live examples in lab environments, while others like myself say that publishing such tools lowers the entry level for those wishing to pursue criminal activity.
[You might also like: The Rise of Booter and Stresser Services]
A similar issue exists with stresser services, otherwise known as the DDoS-as-a-Service industry. A stresser is an online service designed to launch distributed denial-of-service (DDoS) attacks. Users normally purchase packages based on how large of an attack they want to launch, vectors they wish to use and the duration in which their membership will last. These web based services that offer DDoS-for-hire are priced very low, as little as $19 a month, and can deliver over 1Gbps with multiple vectors. Hidden inside the terms of services are sections designed to place liability in the hands of their users. Normally along the lines of “Permission is granted to stress test dedicated servers and networks owned by you” in the case of Kronos Booter, but these services never check to see if the tester owns the site targeted in the DDoS attack.
[caption id="attachment_6590" align="aligncenter" width="624"]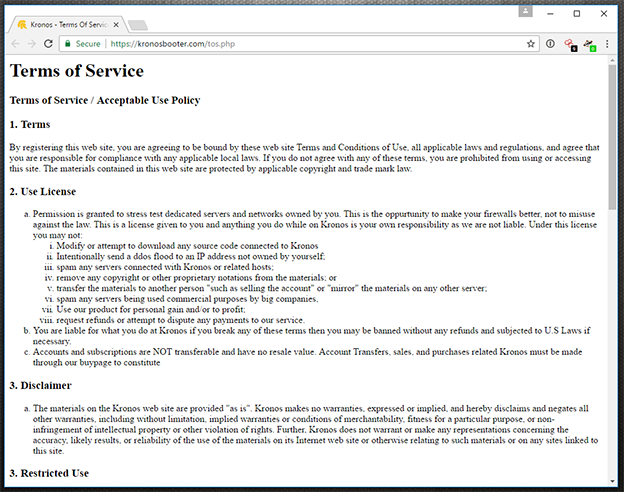 Kronos Booter Terms of Service[/caption]
Kronos Booter Terms of Service[/caption]
While several legitimate services do exist for companies wishing to test their new DDoS mitigation devices, most of these illegitimate stresser services are abused by lower-level criminals looking to target corporate networks and gaming services. Once only advertised in underground forums, they have now become very public with hundreds of services to select from by simply searching on Google for stresser or booter. These sites are often run by teenagers or young adults who don’t know what they are doing. Often, they are just copy-paste clones from posts found in underground forums. One of the main issues is the profit behind these services. Stresser services can launch thousands of attacks a week for illegitimate purposes, making the owners tens of thousands of dollars in the process.
A bigger issue is the traffic that is generated from these services. Many of the attack vectors offered for these services rely on reflection techniques that use vulnerable 3rd party DNS or NTP servers to amplify their attack. Even in the case of renting botnets like Mirai or other Internet of Things (IoT) based botnets, you are using traffic that is generated from illegally compromised devices. These services also advertise that some vectors of attack are untraceable. If the services are for legitimate purposes, why would they advertise “take down your competitors” or “attacks are untraceable”?
So, are these services and projects for legitimate uses? Yes and no. It really depends on the user’s intent. As a researcher, I use different open source projects and services that could be used for malicious intent, but I use them responsibly in closed environments for research purposes only. Their availability makes it easier on me, but at the same token makes it easier for would-be criminals to attempt to run a Ransomware or DDoS-for-Ransom campaign. In my opinion when it comes down to open source projects on Github, they should only be published after responsible disclosing and patching the vulnerability. In the case of stresser services I think they need to put more effort into verifying the ownership of the intended target before the user can open fire.
Read the 2016–2017 Global Application & Network Security Report by Radware’s Emergency Response Team.
Download Now