Over the last few days, Radware’s Security Research Groups have been monitoring a global incident related to a ransomware variant named WannaCrypt, also known as WannaCry, WanaCrypt0r and wcry. On the morning of Friday May 12th, a ransomware campaign began targeting computers around the world. Once a computer was infected, a worm replicated itself across the network, targeting other computers as well. Worms use a computer network to propagate to other machines and infect them with the malicious payload.
The payload in this event contained what is known as ransomware. Ransomware is a type of malware that restricts access to user data by encrypting the files on an infected computer. Once the files are encrypted the attacker demands the victim pay a ransom for the decryption key.

This campaign has spread itself across networks leveraging recently disclosed vulnerabilities in Microsoft’s SMB service. MS17-010, a Microsoft security update issued on March 14th, addressed and patched these remote code execution vulnerabilities in Microsoft’s SMB services.
CVE’s patched in Microsoft’s security bulletin, MS17-010:
- CVE-2017-0143
- CVE-2017-0144
- CVE-2017-0145
- CVE-2017-0146
- CVE-2017-0147
- CVE-2017-0148
These exploits were disclosed in April when The Shadow Brokers leaked the Equation Groups’ software, which included FuzzBunch. FuzzBunch is an exploitation framework similar to Metasploit. Inside of the FuzzBunch framework there are many remote exploits for Windows like EternalBlue and DoublePulsar which are being used in the current WannaCrypt campaign.
It was feared by many researchers that the Shadow Brokers’ dump would be used by criminals to target future victims. This fear became a reality later in April when researchers started noticing a backdoor from the Shadow Brokers’ dump called DoublePulsar infecting computers around the world.
The DoublePulsar SMB plant from the Shadow Brokers’ dump is a backdoor exploit. In the month of April, DoublePulsar infected close to 200,000 computers. This backdoor gives the attacker a persistent foothold in the victim’s computer and can be used to distribute malware, send spam, or launch attacks. EternalBlue is a remote code exploit affecting Microsoft’s Server Message Block (SMB) protocol.
[You might also like: As Cyber Security Programs Lose Their Moorings to Ransom-DoS: Radware Introduces the Ultimate Guide to Cyber Ransom]
Attackers are also using the EternalBlue vulnerability to gain unauthorized access and propagate WannaCrypt to other computers on a targeted network.
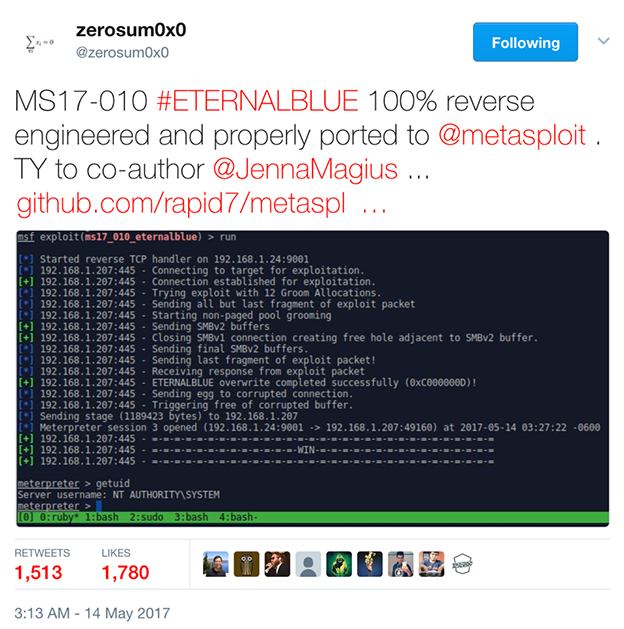
It appears the attackers are using publicly available tools like Fuzzbunch from the Shadow Brokers’ dump or Metasploit to run this campaign. On Github you can find the exploits, payloads and scanners needed to launch an attack against a computer using a number of vulnerabilities found in MS17-010. The author behind the current campaign combined WannaCrypt with the delivery method of abusing a vulnerability in Microsoft’s SMB service for infection. This campaign targeted anyone who did not update their devices after Microsoft released patches for the vulnerabilities in security update MS17-010.
Upon infection, WannaCrypt executes a file that sends an HTTP GET request to a hard coded domain. This is a kill switch. If the request for the domain is successful, WannaCrypt will exit and not deploy. If the request fails, then it continues to carry out infecting the device and others on the network.
When the campaign began on Friday, a security researcher, @MalwareTechBlog, noticed the kill switch domain was unregistered. He promptly registered the domain and directed the request to a sinkhole, effectively preventing this variant from spreading further.
Kill switches
- iuqerfsodp9ifjaposdfjhgosurijfaewrwergwea[.]com (@MalwareTechBlog)
- ifferfsodp9ifjaposdfjhgosurijfaewrwergwea[.]com (@msuiche)
After dropping the first executable and checking the domain for the kill switch, WannaCrypt will drop another executable to scan the IP addresses and attempt to connect to vulnerable devices via the SMB vulnerability on port 445. If there is another vulnerable device on the network, the worm will make the connection and transfer the malicious payload to that device as well.
Over the weekend two other variants appeared: One that had the kill switch removed but failed to infect its targets with WannaCrypt, and the other had a new kill switch domain. This variant was successfully targeting other computers. This discovery was made by @benkow_ and @msuiche registered the domain. Once the domain was registered, he pointed it to a sinkhole to prevent it from spreading as well.
The Tor client is also embedded inside of WannaCrypt. The Tor client is installed on the infected machine so it can receive the encryption keys from the hidden c2 servers on the Tor network.
- gx7ekbenv2riucmf.onion
- 57g7spgrzlojinas.onion
- xxlvbrloxvriy2c5.onion
- 76jdd2ir2embyv47.onion
- cwwnhwhlz52maqm7.onion
Once infected, WannaCrypt users are presented with a notice that their files have been encrypted and demand the victims to pay a ransom of $300 in Bitcoin. Three days after the infection, the ransom increases to $600. When the clock expires after seven days, the victim loses the ability to pay the ransom and decrypt their files. The files on the infected computers are encrypted using a custom AES-128 in CBC mode. At the time of writing, 194 payments totaling $53,453.58 have been made to the Bitcoin wallets hard coded into this version of WannaCrypt.
[You might also like: Ransom, Ransom Everywhere]
[caption id="attachment_7021" align="aligncenter" width="618"] WannaCrypt[/caption]
WannaCrypt[/caption]
WannaCrypt BTC wallets:
At the moment there are no confirmed reports of victims receiving a key for decryption after making a payment. Normally ransomware campaigns have personalized BTC wallets to help identify who has paid the ransom. In the case of WannaCrypt, it’s believed the only way to identify to the author that you have made a payment is by sending the extortionist your transaction ID through their Contact Us section. The current version in circulation is WannaCrypt 4.0.
[caption id="attachment_7022" align="aligncenter" width="624"]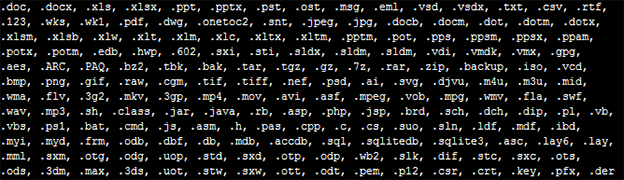 Filetypes that WannaCrypt targets for encryption[/caption]
Filetypes that WannaCrypt targets for encryption[/caption]
This outbreak highlights an evolution in ransomware attacks. No longer does a malware author have to target large swaths of the population via a phishing campaign with the hopes that someone opens an infected document. With the WannaCrypt campaign leveraging EternalBlue, it shows that ransomware is evolving and leveraging different vectors of attack. With this method the author only has to target one vulnerable computer on the network. Once that device is infected, the ransomware will worm across the network, compromising other vulnerable computers.
Users should immediately patch their computers with the latest security updates from Microsoft. MS-17-010 will include the patch for this vulnerability. Microsoft has even pushed an update for Windows XP, which hasn’t seen an update since it went out of support in 2014. Users who cannot update should disable SMBv1 from allowing direct connections. To do this, open Windows features and uncheck the box “SMB 1.0/CIFS File Sharing Support.”
[caption id="attachment_7023" align="aligncenter" width="449"]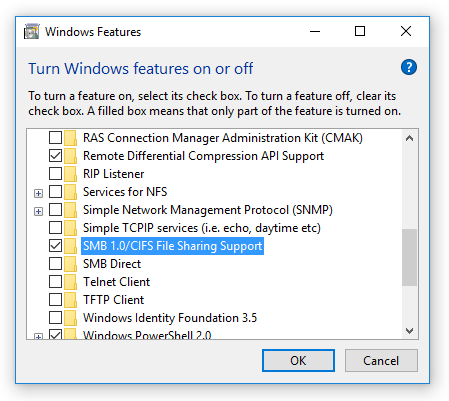 Windows Feature[/caption]
Windows Feature[/caption]
In addition, users should get into the habit of creating backups so in the event they do lose data, all is not lost. Ransom-based attacks are on the rise, and businesses face a growing threat from these financially-driven cyber assaults that hold their data or services hostage. In general, these attacks come in two primary “flavors.” Ransomware and DDoS-for-Ransom. In a DDoS-for-Ransom campaign an attacker will send their victims a letter threatening to attack their organization—rendering its business, operations or capability unavailable—unless a ransom is paid by the deadline. If a ransom is not paid, the attacker will take their target offline with a volumetric denial-of-service attack. In either case companies and users are advised not to pay an extortionist and to seek professional help when needed.
Download the "Cyber Ransom Survival Guide: The Growing Threat of Ransomware and RDoS – and What to Do About It" to learn more.
Download Now