Internet of Things (IoT) botnets have forever changed cyber-security. When an IoT botnet - which is a group of internet-connected computers, appliances or devices that have been co-opted to launch a cyber-attack – is unleashed, the results can be devastating.
Nearly any internet-connected device can be considered an IoT device. With humanity’s growing reliance on the internet, the number of devices capable of being hacked and used as part of a botnet has increased dramatically. By 2020, there will be over three IoT devices for every human on planet earth.
As a result, what was once the storyline for a science fiction movie (household appliances being hacked and turned against humanity) now reality. From fish tanks to dishwashers to automobiles, here are seven of the strangest IoT devices that have been hacked in recent years.
Cayla – The Illegal Espionage Apparatus
[caption id="attachment_8185" align="aligncenter" width="594"] Source: ParentingHub https://parentinghub.co.za/2014/10/my-friend-cayla/[/caption]
Source: ParentingHub https://parentinghub.co.za/2014/10/my-friend-cayla/[/caption]
With waist-length golden hair and a voice designed to warm a child’s heart, Cayla has brought delight to millions of children throughout Germany. In reality, she’s an “illegal espionage apparatus” that must be destroyed immediately, according to Germany’s Federal Network Agency.
Once hackers are in control of this Wi-Fi – enabled interactive doll, they can use its cameras and microphones to see and hear whatever Cayla does, allowing hackers to track their location or potentially heist profits from the local street-side lemonade stand. Most importantly, when the security on these Internet-connected devices are neglected, they can be unwittingly conscripted into an army of hacked machines known as a botnet.
[You might also like: Smart Homes of Tomorrow – Connect all the things!]
Ocean’s 14?
[caption id="attachment_8187" align="aligncenter" width="1072"] The Shark Reef Aquarium at Mandalay Bay and not the casino in question. Source: MGM Resorts https://www.mgmresorts.com/en/things-to-do/mandalay-bay/shark-reef-aquarium.html[/caption]
The Shark Reef Aquarium at Mandalay Bay and not the casino in question. Source: MGM Resorts https://www.mgmresorts.com/en/things-to-do/mandalay-bay/shark-reef-aquarium.html[/caption]
When it comes to stealing data, hackers will use any means at their disposal. Casinos are some of the most secure organizations/facilities on the planet, which is why one group of hackers elected to hack a casino via a thermometer in an aquarium in the lobby.
After accessing the casino’s network, hackers located the high-roller database and extracted it via the thermostat. This heist might not have been as daring as Ocean’s Eleven, but for those high-rollers who had their personnel data compromised, both they and the casino were left with a losing hand.
Hacking One Page at a Time
[caption id="attachment_8188" align="aligncenter" width="810"] Source: PC Mag https://www.pcmag.com/article2/0,2817,2411967,00.asp[/caption]
Source: PC Mag https://www.pcmag.com/article2/0,2817,2411967,00.asp[/caption]
Printing at the office can be a risky proposition. You run the risk of a coworker viewing something that is personal. You have to undergo the hellish task of loading legal-sized paper into tray 2. Or you risk invoking the wrath of finance from using the expensive color printing options. But one stands above them all: if your organization’s network-connected printer is hacked by a digital assailant. It suddenly makes a “PC LOAD LETTER” message seem like a cakewalk.
Successful hacks of printers have allowed hackers to siphon off the printer’s memory to access print jobs containing sensitive files, such as contracts, corporate data or patient information. In addition, corporate passwords can be compromised if the printer leverages role-based permissions.
It could also boil down to a scene straight out of the movie Office Space.
[caption id="attachment_8189" align="aligncenter" width="784"] Office Space, 20th Century Fox[/caption]
Office Space, 20th Century Fox[/caption]
[You might also like: Smart Homes of Tomorrow – This is Not What We Expected]
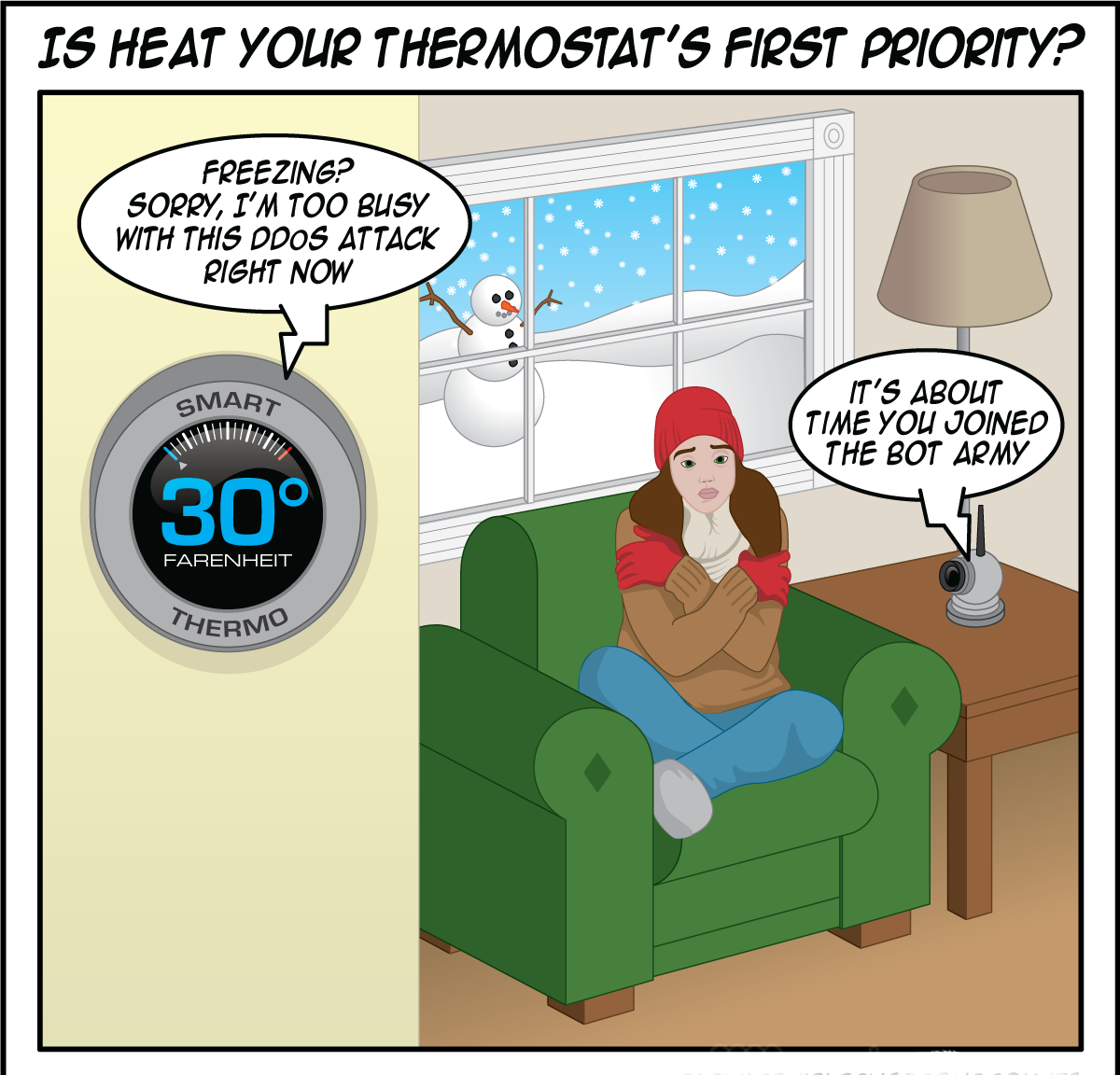
Turning Up the Freeze
The next generation of internet-connected thermostats has become a perennial favorite of hackers, as seen by the aforementioned casino example. But in 2016, hackers put the freeze on the citizens of Lappeenranta, Finland when they managed to hack the environmental control systems in two apartment buildings via thermostats.
In their attempt to fight off the attack, the environmental systems were rebooted – and subsequently stuck in an endless loop that left residents in the cold for nearly a week.
A True Nightmare – Hacked Baby Monitors
[caption id="attachment_8190" align="aligncenter" width="1055"] Source: https://servicemasteranchorage.com/2016/02/29/128/oh-my-gosh-face/[/caption]
Source: https://servicemasteranchorage.com/2016/02/29/128/oh-my-gosh-face/[/caption]
Baby monitors have come a long way since their introduction in the 1930s. What started has simple one-way radio transmitters have evolved into sophisticated WiFi-enabled, smart devices that have a receiver, video camera, infrared vision and a host of other capabilities.
These same high-tech capabilities have turned these titans of toddler security into a true nightmare. Hackers seek opportunity, and these barely-secure devices can be hacked virtually anywhere in the world via their Wi-Fi connections. Baby monitors are a perfect example of how seemingly innocuous, internet-connected devices can be pooled by hackers to launch massive denial-of-service attacks.
Becoming a Backseat Driver
Automotive cyber-security experts Charlie Miller and Chris Valasek have made waves (or speedbumps) in recent years by hacking into Chrysler Jeep Cherokees. What started as sending remote commands via the system that queries the GPS system has turned straight into a plot from an action movie such as Fast and Furious. They’ve now proven that a hacker can remotely turn the steering wheel or activate the parking brake, all at highway speeds. The long feared concept that somebody could turn you and your automobile into a crash test dummy is quickly becoming a reality.
https://www.youtube.com/watch?v=MK0SrxBC1xs
A Not-So- Smart, Smart TV
Smart TVs now represent the majority of new television sales. According to market research firm IHS Markit, 69 percent of all new sets shipped in North America in 2017 were internet-capable, and the percentage will increase throughout 2018. Internet connectivity brings a lot of appealing functionality: the ability to stream content via popular apps such as Hulu and Netflix, as well as the ability to find content quickly using voice commands.
It also brings a security nightmare out of the data center and into the living room. These TVs also come with substantial data collection, and because they’re internet enabled, that means they can be hacked and data can be compromised. Hackers can change channels, play offensive content or heist detailed data about the TV’s users. And with TVs becoming the centerpiece of consumers’ increasingly connected homes, it won’t be long before a hacker can leverage a compromised set to potentially control other smart-home devices, from the aforementioned thermostats and cameras to washing machines and speakers.
A relaxing evening of binge watching Netflix can turn into domestic hell when the TV changes channels, the washing machine does a load of laundry and your stove starts to boil water.
Download "When the Bots Come Marching In, a Closer Look at Evolving Threats from Botnets, Web Scraping & IoT Zombies" to learn more.
Download Now