Last month I wrote about how cyber criminals are targeting gamers around the world and the steps we need to take to help educate users. While gamers are highly targeted, cyber criminals are not solely focused on the user. They are also targeting the gaming industry and those that support it at high volumes for profit.
For example, ticket sales to Dota2 The International on Damai, an entertainment ticket platform in China, was targeted by scalpers who leveraged bots against a poorly secured application to purchase mass quantities of tickets to the event. Over 26,000 tickets sold out in under a minute, preventing average spectators from purchasing a face value ticket.
 The International 9 Scalpers - https://imgur.com/icpC4XY-
The International 9 Scalpers - https://imgur.com/icpC4XY- Scalpers running bots and stadiums filled with tens of thousands of spectators watching eSporting events is just the beginning. eSports are already competing with traditional sports and will eventually make their way into the Olympics.
In an outlook published by Activate, the forecast shows that the global viewership for eSports alone will reach 520 Million by 2022. To put this in perspective, there were only 11.8 million viewers that tuned into the Monday Night Football this week.
The Growth
eSports is now the fast-growing sport in the world due to the digital transformation of gaming platforms. Internet-connected platforms have not only allowed gamers to connect and compete against users from around the world, but they have also created massive streams of profit for everyone involved.
[You may also like: Gamers Beware: Cyber Criminals Are Coming For You]
Steaming games on YouTube and Twitch also helped usher in a new era of professional gamers and internet personalities as eSport spectators began to emerge in large numbers. For example, The Dallas Cowboys have around 3.9 million fans on twitter compared to the 4.9 million fans that pro gamer Ninja has. On YouTube, The Dallas Cowboy has only 122,000 subscribers where Ninja has 22.4 million subscribers.
Following the rise of eSpectators came sponsorships, big
money, and massive tournaments. This year, 16-year-old Kyle “bugha” Giersdor
won $3 Million in a Fortnite tournament. The shocking part about these numbers
is that this is only the beginning of the gaming transformation.
With the explosive growth of new gamers, there has become more of a demand for cross-platform and cloud-based games so that users can enjoy playing anywhere, as the era of console games begins to lose its market share. As a result, more fans are playing games and watching streams on mobile devices.
[You may also like: The Normalization of DDoS Attacks]
At this point, it’s fair to say that the console era is coming to an end for the average gamer. According to a recent report published by Newzoo, mobile gaming is the largest developing sector in the industry. This is largely due to accessibility and advancements in mobile technology.
The gaming industry has now formed a perfect foundation on
mobile technology, allowing the average user to both game and spectate on their
mobile device from anywhere in the world. Advancements in data processing, graphics,
and 5G technology will help take mobile and cloud gaming to the next level in
the coming years.
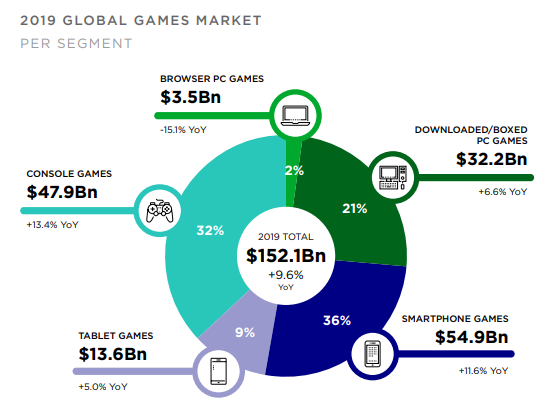 Source: Newzoo
Source: NewzooRevenues in the gaming industry are also outpacing the GDP of some small countries. Players have spent billions of dollars on in-game purchase in Fortnite and Pokemon Go. While this sounds great to an investor, it results in an elevated risk of cyber-attacks for the industry.
Attack Vectors
Over the years, Radware has monitored the growth in cyber-attacks
directed at the gaming industry and mobile platforms. While large-scale DDoS
attacks directed at the gaming industry are still very popular, credential
stuffing attacks have become an extremely common occurrence over the last year.
[You may also like: Credential Stuffing Campaign Targets Financial Services]
Credential stuffing is one of the most commonly used attack vectors by cybercriminals today. It's an automated web injection attack where criminals use a list of breached credentials to gain access and take over accounts across different platforms due to poor credential hygiene. Typically, cyber criminals will stuff gaming networks to steal and resell in-game items that users have purchased. While this doesn’t sound very profitable, the gaming industry is making billions on in-game content. As a result, criminals have found a way to get in on the action.
A Distributed Denial-of-Service (DDoS) attack occurs when multiple infected devices flood a targeted system to make it or network resources unavailable. Typically, attackers will target gaming networks or the users themselves. While law enforcement has gone to great extents to dismantle Booters and Stresser services, the problem still grows, leaving some companies to act on their own. Recently Ubisoft announced that it will sendcease and desists letters to websites and people hosting stresser services.
To view near real-time DDoS attacks, visit: https://livethreatmap.radware.com/
[You may also like: Empowering the Infosec Community]
Protections
This gaming industry is growing at a rapid rate and requires companies to get ahead of their problems now. To defend against these attacks, organizations need to deploy a WAF that can properly fingerprint and identify malicious bot traffic like retail bots, as well as automated login attacks like credential stuffing, directed at gaming applications.
When it comes to defending against DDoS attacks, one of the biggest challenges in mitigating an attack against a gaming platform is distinguishing the difference between legitimate and malicious users. Only an advanced anti-DDoS solution can successfully distinguish the difference between the two, allowing legitimate users the ability to access gaming content during an attack.
Download Radware's “Hackers Almanac” to learn more.
Download Now