It was the best of times, it was the worst of times, it was the age of 5G networks, it was the beginning of a new threat landscape the likes of which have never been faced before.
The commercial rollouts of 5G networks beginning in 2020 set up a tale of two prospects, a story full of twists and turns that would surely delight Charles Dickens.

1.The promise of blazing fast data speeds and lower latency services on mobile networks that enable largescale deployment of IoT devices; and
2.The certainty of new attack vectors launched through the vastly expanded number of access points in 5G networks’ distributed architecture 5G technology forever changes expectations for the mobile network experience.
All traffic is in the cloud, and computing elements and services are closer to the edge of the network, which improves performance and makes it easier for service providers to scale services. The 5G infrastructure is ideal for the deployment of IoT devices because it can handle massive amounts of data with very low latency from mobile connections.
[You may also like: 5G Security Considerations for Security Providers]
Network performance improvements and IoT capabilities promise to help businesses move even faster to create value for customers by taking advantage of productivity gains and new market opportunities. Yet uncertainty about this new technology is prevalent.
Ready or Not
The majority of respondents to Radware's annual global survey indicated that they are not prepared for 5G network rollouts in their countries. Companies in APAC and EMEA were more likely to say that they are at least somewhat prepared compared to organizations in Latin America. Service provider/telecom companies were more likely than any other vertical to say that they are prepared to handle 5G rollouts (58% vs. 16%–34%), although 13% said that they won’t address 5G before 2022.
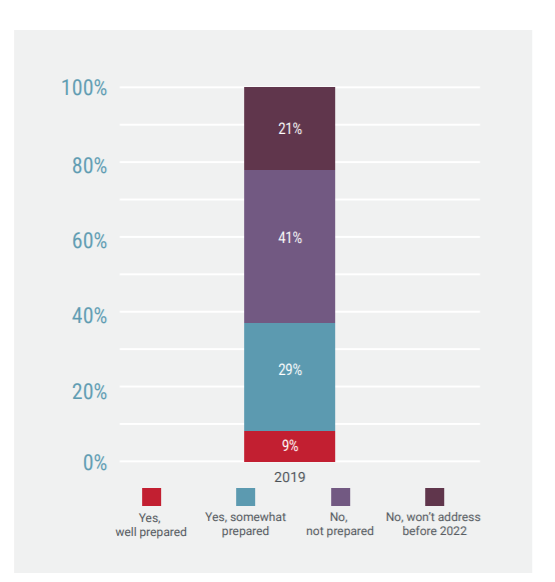 Enterprises’ preparation for 5G network rollouts.
Enterprises’ preparation for 5G network rollouts.
The distributed architecture of 5G networks introduces a whole new set of security threats. In particular, IoT devices typically have low security measures embedded at endpoints, making them ideal launch points for coordinated malware attacks by botnets within and outside networks.
Thirty-eight percent of respondents said that they don’t know if they have experienced DDoS attacks originated by IoT botnets. Lack of visibility by enterprises into attack surfaces could spell trouble in the future when 5G networks are more prevalent.
[You may also like: 5G, Security, IoT, and ROI: Some Assembly and Automation Required]
Service providers are further along in their preparations for 5G than enterprises. Fifty-eight percent of service provider respondents indicated that they feel prepared for the 5G rollout, compared to 38% of total respondents. Since service providers are the entities that are actually deploying 5G networks, it makes sense that respondents from this group are further ahead in their comfort level with the changes that the technology will bring.
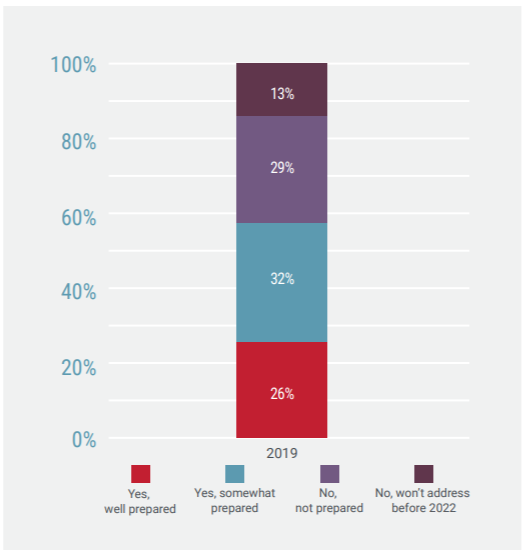 Service providers’ preparation for 5G network rollouts.
Service providers’ preparation for 5G network rollouts.
The difference in confidence levels points to an opportunity for service providers to educate enterprise customers about the benefits of 5G as well as what the changing threat landscape means for their businesses.
Enterprises are concerned about outbound traffic generated by connected devices as well as network elements at the edge of the network. In the global industry survey, 36% more service provider respondents vs. all respondents see outbound threats originating from connected 5G devices as the greatest risk of 5G technology.
Concerns About IoT Abound
Yet organizations are eager to take advantage of IoT devices. International Data Corporation (IDC) estimates that, by 2025, there will be 41.6 billion connected IoT devices generating 79.4 zettabytes (ZB) of data.
When it comes to IoT connected devices, respondents are most worried about malware propagation (44%), followed by no visibility (20%), denial of service (19%) and permanent denial of service/bricks (11%).
[You may also like: Securing the Customer Experience for 5G and IoT]
These concerns are warranted. IoT devices have no standard of security built in. The emphases in the development of this equipment are data collection and price sensitivity for production and sales. The burden of the security vulnerabilities is something that enterprises have never had to deal with before.
Enterprises may assume that service providers will provide protections for IoT device security in the network. For service providers that already need to protect their own network assets against threats launched from IoT devices, offering 5G security as a managed service is a possible incremental revenue opportunity.
Taking the Good With the Bad
To protect against 5G security threats, service providers must implement solutions to safeguard these protection points in the network infrastructure.
[adbutler zone_id="276005"]
Because of its distributed nature, the deployment of 5G networking infrastructures is dramatically different than that of previous generations of mobile networks. Network functions are virtualized, so services can expand beyond service providers’ networks to external network domains to be physically closer to connected devices for more efficient delivery. Faster data speeds and lower latency combine to enable a whole new world of possibilities for service providers and enterprises.
But the increased size of the attack surface and susceptibility of IoT connected devices will require both service providers and enterprises to quickly get up to speed on new security requirements. Gaining visibility into what is happening at all access points is critical for protecting 5G networks.
In an already tight labor market for security professionals, finding talent that has the expertise to lead 5G-related initiatives is challenging. Instead, enterprises will likely turn to service providers to offer security measures for inbound traffic from the internet.

Read Radware's “2019-2020 Global Application & Network Security Report” to learn more.
Download Now