Cyber and Securities – Financial Institutions Attack Landscape
Recently Italian bank Unicredit suffered two security breaches. Data of 400,000 customers was stolen, including loan account numbers and Personally Identifiable Information (PII). There is a suspicion the breach had to do with interaction with a 3rd party. This incident is the latest reported in a long history of cyber-attacks against financial institutions. Every hack however, can teach us a lesson.
2016 was a tough year for the financial services industry, which suffered 44 million cyber-attacks, making it the most targeted industry.
The most notorious hit was the SWIFT vulnerability that resulted in an $81 million heist from the Central Bank of Bangladesh. This success encouraged the perpetrators to repeat the attack, reportedly capturing close to $1 billion. In parallel, numerous Bitcoin marketplaces, such as Bitfinex, DAO and Ethereum, came under attack. Bitfinix, a Bitcoin exchange company, lost more than $65 million in one day due to a security breach of multiple wallets.
To this day, Anonymous runs a campaign against financial institutions called OpIcarus. What started as a simple protest against the Bank of England and the New York Stock Exchange quickly escalated into a full-fledged, multi-phase DDoS operation targeting the International Monetary Fund, central banks and global stock exchanges. OpIcarus entered its fifth phase in June this year.
All these attack campaigns pushed the financial services industry towards the center of our Ring of Fire where typically governments and service providers reside.

Information Security Challenges of Financial Institutions
Data Protection
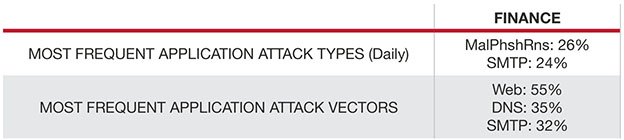
According to Radware’s latest Application and Network Security Report, protecting sensitive data was the top concern for organizations. Financial institutions guard a large variety of sensitive information – PII, account credentials, and credit cards, but also market predictions, interest analysis, investment portfolios and much more. Sensitive data is highly valuable in the Dark markets, where there is a prospering trade in such records. Thus, data is lucrative for both businesses and hackers. These hackers build sophisticated programs to evade protection mechanisms and get ahold of sensitive information. From a defender’s point of view, a clear distinction needs to be made between bot and human activity (using baselines and behavioral analysis) as well as interception of communication with Command and Control (C&C) servers.
Mobile Banking
How do you maintain an easy and user-friendly experience in the most secure way? Let’s be honest with ourselves. How many businesses secure their mobile applications as much as they protect their network or web-based services and applications? What about all the APIs these applications use? Now think of mobile banking – the complexity becomes larger. Many smartphones are vulnerable to all sorts of malware and sensitive information (even usernames and passwords) might be exposed to data harvesting tools. In addition, the mobile application usually interacts via APIs with social media, location and other applications that are installed on the device.
The SSL Challenge
The obvious answer would be to use encrypted data. Indeed, many websites and businesses today go towards 100% SSL/TLS communications. However, it requires quite a large investment in hardware upgrades as processing encrypted traffic requires a lot more computing resources. While new ciphers may result in high latency and challenge legacy systems, old ciphers are insecure. It is important that businesses understand that just SSL is not a replacement for security but it has to be monitored as well, as there are many SSL-based application and DoS attacks (like floods or key renegotiation). Such attacks hit one third of financial institutions.
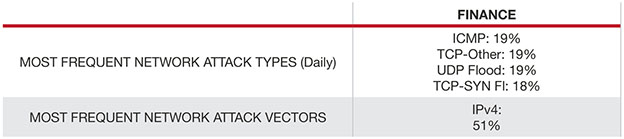
Availability – Characteristics of DDoS Attacks Against Financial Institutions
Financial institutions are known to attract fire, and indeed 28% of them are attacked on a weekly basis. OpIcarus by Anonymous is a campaign targeting stock exchanges and central banks. Burst attacks are increasing thanks to their effectiveness against most mitigation solutions.
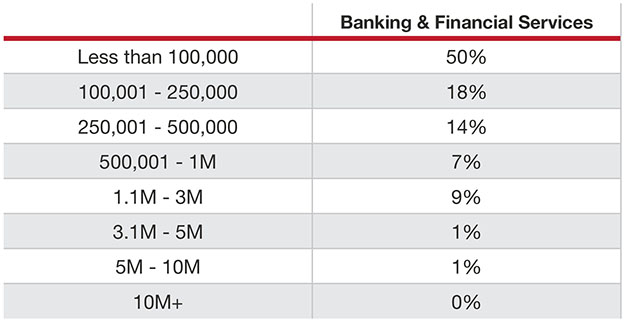
Cyber-Attacks Cost Almost Twice What You May Think
Most companies have not come up with a precise calculation of the losses associated with a cyber-attack. Those who have quantified the losses estimate the damage at nearly double the amount compared to those who do not quantify. Financials estimate the average cost of a cyber-attack to be $500,000.
[You might also like: How Do You Create a Flight Plan to a Never-Ending Journey?]
Compliance: FIPS, PCI DSS, GDPR
FIPS and PCI DSS are just a couple of standards that financial institutions have to adhere to. If such institutions fail an audit or worse – get breached, they will have to carry very high costs for not securing their system properly (up to $4 of the total annual revenue according to the upcoming enforcement of GDPR in May 2018). So while the cost for hackers to launch an attack (a handful of U.S. dollars is the current street price for a simple Cyber-Attack-as-a-Service tool on the Darknet). It is a challenge for both financial institutions and regulators to follow the rapid evolution of adapting agile and efficient methodologies of information-sharing and cross-platform integration in order to be able to think of all risks and provide guidance.
Here are a few thoughts on how to significantly reduce the attack surface and reduce costs associated with cyber-attacks (the five ‘E’s):
- Encryption – TLS is required to secure the communications between the client and APIs for transport confidentiality and integrity of data in transit.
- Employee education – To prevent insider threats and specifically BEC (Business Email Comopromise), make sure employees comply with internal and industry regulations and are attentive to suspicious emails and communications, and handle data with care.
- Exchange of information – Integrating 3rd party application services must not pass along any sensitive information if there’s no clarity on what happens next. Just as well – it is important to challenge incoming data streams and filter possible injections, exploitations and contamination attempts.
- Entity access to data – Strong authorization and multi-factor authentication mechanisms are to be applied on HTTP requests’ behavior. Permissions should be carefully analyzed and mapped.
- Emergency response plan – Know who does what at the moment of an event. Map your risks, understand the impact, prioritize mission critical tasks and practice in advance. It will help to significantly shorten the event elimination cycle, limit brand reputation damage and reduce fines and associated costs.